Kubernetes-Native Authentication in OpenShift using External Authentication
This guide describes how to configure OpenShift to accept OIDC tokens issued by an external identity provider, enabling standardized Kubernetes-native access workflows across managed and self-managed OpenShift environments.
What this reference architecture covers
This reference architecture covers the following deployment paths:
-
ROSA with Hosted Control Planes (HCP) — the primary reference implementation
-
Azure Red Hat OpenShift (ARO) HCP — under active development toward GA
-
Self-Managed OpenShift 4.20+ — Generally Available; Technology Preview on 4.19
All three paths use Red Hat Build of Keycloak (RHBK) as the reference external identity provider. However, any standards-compliant OIDC provider can be used.
Who this is for
This reference architecture is designed for platform engineers, cluster administrators, and architects who are evaluating or implementing authentication workflows within OpenShift environments.
Experience with the following is assumed:
-
OpenShift cluster administration
-
Authentication and identity management concepts
-
OIDC and OAuth 2.0 protocols
-
Command-line tooling (
oc,rosa, orazdepending on environment)
What you will learn
By following this reference architecture, you will understand:
-
How OpenShift External Authentication differs from the built-in OAuth server
-
How to configure an OIDC provider for OpenShift integration (The Red Hat Build of Keycloak is used as the reference implementation in this guide)
-
How to enable and configure external authentication within OpenShift self hosted and managed environments
-
The specific configuration steps for each supported deployment environment
-
How to assign OpenShift RBAC policies to external identities
-
How to access OpenShift using CLI and Web Console with external credentials
Architecture overview
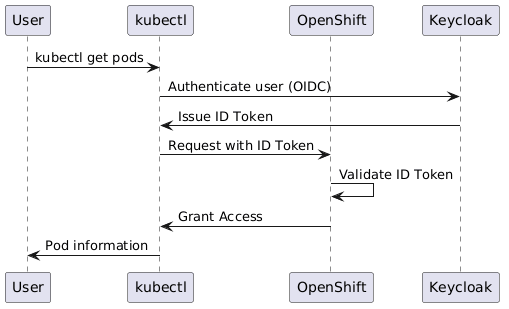
The following diagram illustrates the authentication flow when OpenShift External Authentication is enabled:
Navigation
Use the left navigation panel to move through this reference architecture:
-
Architecture Overview — benefits, components, and deployment options
-
ROSA HCP — Red Hat OpenShift Service on AWS (ROSA) with hosted control planes (HCP)
-
ARO HCP — Azure Red Hat OpenShift (ARO) with hosted control planes (HCP)
-
Self-Managed OpenShift — Use within standalone OpenShift environments
-
Red Hat Build of Keycloak Configuration — Reference identity provider setup
-
Accessing OpenShift with External Credentials — Accessing OpenShift using the CLI and Web Console with externally obtained credentials