Network controls and segmentation methods allow you to control, segregate, and visualize Kubernetes traffic. These methods help you isolate tenants and better secure communications flow between containerized applications and microservices.
August is “Network Controls” month in Red Hat’s monthly Security series! Since March 2021, the Red Hat Security Ecosystem team has published monthly articles and videos on DevOps Security topics to help you learn how Red Hat can help you master the practice called DevSecOps.
By explaining how to assemble Red Hat products and introducing our security ecosystem partners, we aim to aid in your journey to deploying a comprehensive DevSecOps solution.
Network controls defined
Network controls are typically implemented in a running Kubernetes cluster, and the goal is to provide a defense-in-depth approach to protect Kubernetes network traffic. The following security methods make up the Network Controls category:
-
CNI / SDN: Software-defined networking (SDN), which provides a programmable, adaptable network fabric that is provisioned in real-time to support dynamic networking security requirements and is typically implemented with a container networking interface (CNI).
-
Network Policies: control traffic flows at the IP address or port level, and can be enhanced with cluster ingress and egress traffic controls, logging and network visualization.
-
Ingress, Egress Traffic Controls: provide protection of network traffic within a running cluster between pods.
-
Hardening Service Mesh: includes network segmentation, authentication and authorization for containerized applications and microservices.
-
Network Visualization: provides a graphical user interface showing the network traffic and relationships in order to control and identify suspicious activity.
-
Packet Analysis: capturing live pod network traffic to typically debug issues in the communication between services.
-
API Management: controlling access to APIs and securing API traffic.
Network controls integrated in DevSecOps
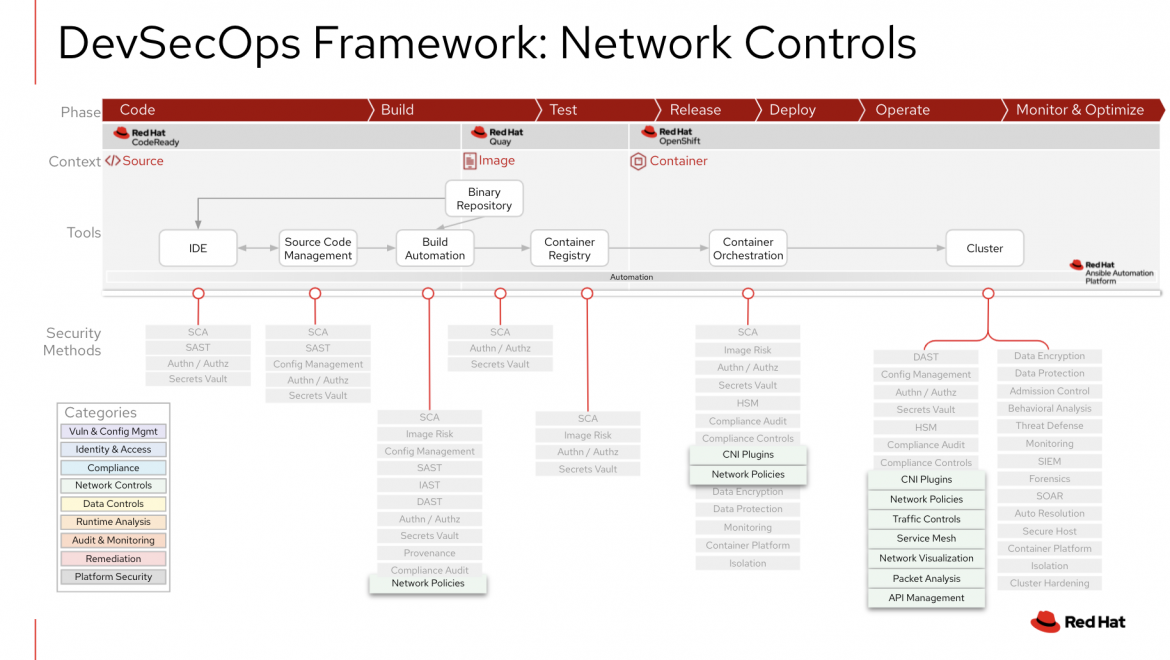
As pictured in the DevSecOps framework below, network controls integrations are typically found on the right side of the DevSecOps life cycle in a running cluster. The table that follows details some, but not all, of the common integrations to consider for network controls.
|
Integration Point |
Description |
|
Build Automation |
While most network controls are integrated in the running cluster, Kubernetes Network Policies provide an Infrastructure-as-code (IaC) approach to network configuration, which is key to adopting DevSecOps. Adding Network Policies within a GitOps and CI/CD process allows you to know who has access to what, audit changes and manage network policy drift. |
|
Container Orchestration |
Network Policies and CNI plugins help to set up Kubernetes networking during pod creation. |
|
Running Cluster |
Implementing network controls in the running cluster is the key integration for this category in order to achieve the defined features in each security method above. Some benefits include controlling access to endpoints outside of your Kubernetes cluster, automating compliance checks, monitoring all traffic within your cluster, and alerting on suspicious activity. Proper network controls configurations will also help provide a Zero Trust Architecture approach to networking, which assumes networks and network traffic is untrusted by default. Both Red Hat and our Security ISV Ecosystem provide capabilities in this category to add to a defense-in-depth approach to DevSecOps. |
Enhance and extend Network Controls with Red Hat partners
Combining Red Hat OpenShift Container Platform Network Control features with Red Hat’s certified ecosystem security partners can help your organization's DevSecOps practice.
If you are looking to enhance and extend Red Hat’s security capabilities in Network Controls, take a look at the following Red Hat Partners:
-
Aqua Security free trial and Operator.
-
Palo Alto Prisma Cloud Compute Edition and webinar.
-
Sysdig free trial and webinar.
-
Tigera Calico Enterprise and Operator.
For more information, visit "Modernize and secure applications with DevSecOps," or begin your discussion with us on enhancing container security and adopting DevSecOps. For similar blog posts on Red Hat’s DevSecOps Framework, search for previous months’ categories (Data Controls, Compliance, Identity and Access and Application Analysis) and stay tuned for upcoming posts.
À propos de l'auteur
Dave Meurer currently serves as a Principal Solution Architect on the Red Hat Global Partner Security ISV team, where he owns technical relationships and evangelism with security independent software vendor partners of Red Hat. Before joining Red Hat, he spent nine years in the Application Security industry with Synopsys and Black Duck, where he served in similar roles as the director of technical alliances and sales engineering.
Meurer also worked for Skyway Software, HSN.com, and Accenture in various management and application development roles. When he’s not thinking about Kubernetes, security, and partners, he enjoys being the VP Sales of North Central Tampa for his wife (the CEO) and 5 kids (Inside Sales).
Parcourir par canal
Automatisation
Les dernières actualités en matière de plateforme d'automatisation qui couvre la technologie, les équipes et les environnements
Intelligence artificielle
Actualité sur les plateformes qui permettent aux clients d'exécuter des charges de travail d'IA sur tout type d'environnement
Services cloud
En savoir plus sur notre gamme de services cloud gérés
Sécurité
Les dernières actualités sur la façon dont nous réduisons les risques dans tous les environnements et technologies
Edge computing
Actualité sur les plateformes qui simplifient les opérations en périphérie
Infrastructure
Les dernières nouveautés sur la plateforme Linux d'entreprise leader au monde
Applications
À l’intérieur de nos solutions aux défis d’application les plus difficiles
Programmes originaux
Histoires passionnantes de créateurs et de leaders de technologies d'entreprise
Produits
- Red Hat Enterprise Linux
- Red Hat OpenShift
- Red Hat Ansible Automation Platform
- Services cloud
- Voir tous les produits
Outils
- Formation et certification
- Mon compte
- Ressources développeurs
- Assistance client
- Calculateur de valeur Red Hat
- Red Hat Ecosystem Catalog
- Rechercher un partenaire
Essayer, acheter et vendre
Communication
- Contacter le service commercial
- Contactez notre service clientèle
- Contacter le service de formation
- Réseaux sociaux
À propos de Red Hat
Premier éditeur mondial de solutions Open Source pour les entreprises, nous fournissons des technologies Linux, cloud, de conteneurs et Kubernetes. Nous proposons des solutions stables qui aident les entreprises à jongler avec les divers environnements et plateformes, du cœur du datacenter à la périphérie du réseau.
Sélectionner une langue
Red Hat legal and privacy links
- À propos de Red Hat
- Carrières
- Événements
- Bureaux
- Contacter Red Hat
- Lire le blog Red Hat
- Diversité, équité et inclusion
- Cool Stuff Store
- Red Hat Summit

