许多公司选择红帽 OpenShift 作为开发和运行所有应用的通用平台,从而避开了异构环境带来的种种困扰。他们不仅可以在红帽 OpenShift 上构建和运行新的云原生应用,还能将传统应用迁移到该平台上。
使用 OpenShift 的一个主要优势是,开发人员只需学习一个接口,而无需了解平台的底层细节。这可以显著提高生产力。
AWS 上的红帽 OpenShift 服务(ROSA)
一些选择采用 OpenShift 的客户希望能够进一步简化工作。他们希望自己的团队不必分心为集群提供基础架构以及管理这些集群,而是可以从一开始就富有成效,只专注于开发应用。对于这类客户,AWS 上的红帽 OpenShift 服务 (ROSA) 会是一个不错的选择。
ROSA 完全托管在 Amazon Web Services (AWS) 公共云上,并由红帽和 AWS 联合维护。这意味着,控制平面和计算节点完全由红帽站点可靠性工程师 (SRE) 团队管理,并由红帽和 Amazon 联合提供支持。这涵盖了所有节点上的 ROSA 安装、管理、维护和升级。
ROSA 的部署选项
ROSA 主要有两种部署方式:一种是部署在公共集群中,另一种是部署在 PrivateLink 集群中。在这两种情况下,我们都建议将 ROSA 部署在多个可用区内中,从而确保弹性和高可用性。
公共集群主要用于没有严格安全要求的工作负载。在这种情况下,集群将部署在私有子网内的虚拟私有云 (VPC) 中,其中包含控制平面节点、基础架构节点以及用于运行应用的工作节点。但是,它仍然可以从互联网访问,因此除了 VPC 外,还需要一个公共子网。
此公共子网上部署的 AWS 负载平衡器(弹性和网络负载平衡器)允许 SRE 团队和访问应用的用户(即集群的入口流量)进行连接。对于用户,负载平衡器会将流量重定向到基础架构节点上运行的路由器服务,再从那里转发到其中一个工作节点上运行的目标应用。SRE 团队将使用专用的 AWS 帐户,通过不同的负载平衡器连接到控制节点和基础架构节点。
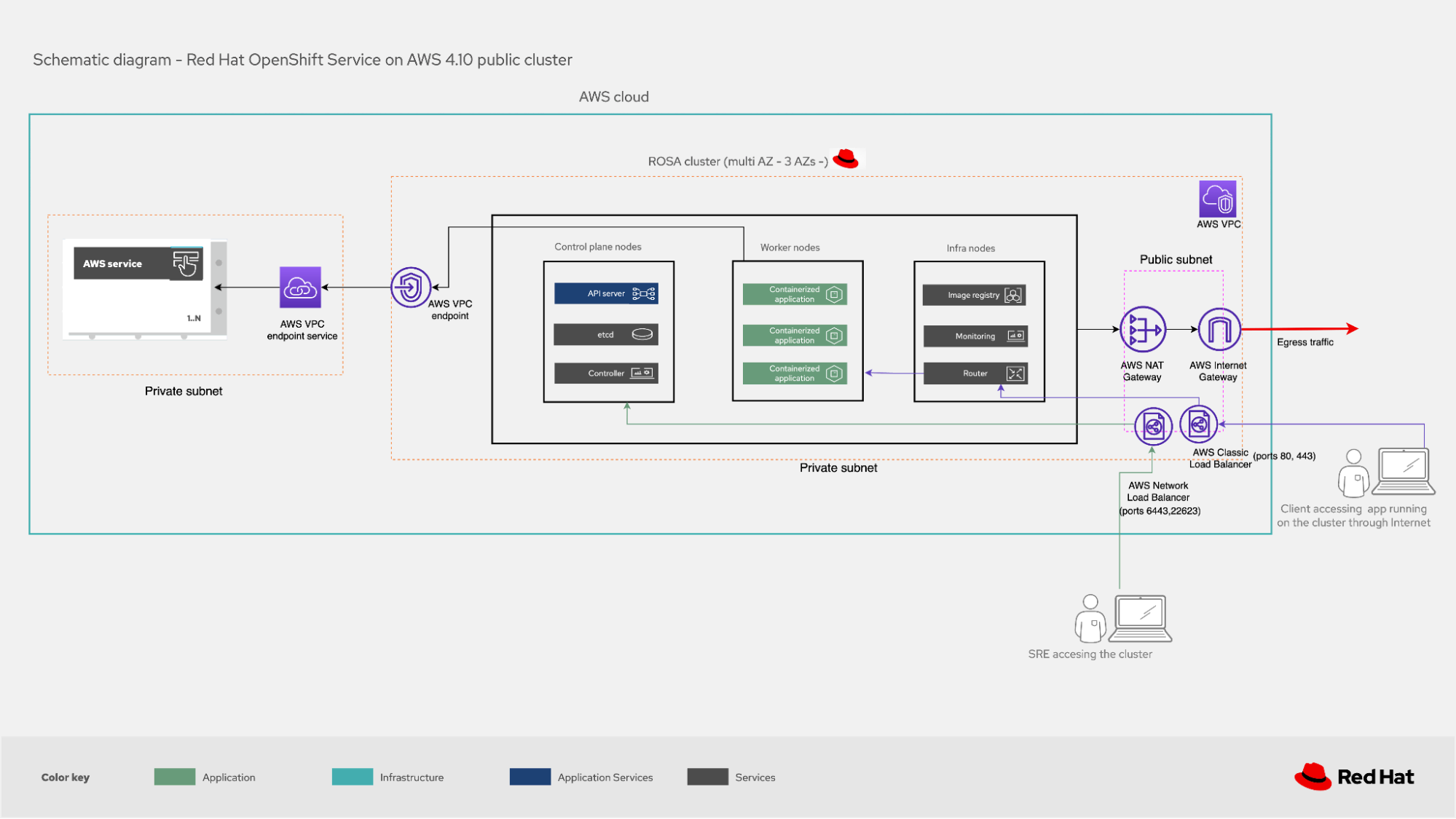
图 1. ROSA 公共集群
对于具有更严格安全要求的生产工作负载,我们建议部署 PrivateLink 集群。在这种情况下,集群所在的 VPC 只有一个专用子网,这意味着它根本无法从公共互联网访问。
SRE 团队使用专用的 AWS 帐户,通过 AWS PrivateLink 端点连接到 AWS 负载平衡器。负载平衡器根据需要将流量重定向到控制节点或基础架构节点。(创建 AWS PrivateLink 后,需要经过客户批准,SRE 团队才能通过 AWS 帐户进行访问。)用户连接到 AWS 负载平衡器,由负载平衡器重定向到基础架构节点上的路由器服务,然后再从那里路由到运行目标应用的工作节点。
在 PrivateLink 集群实施中,客户通常选择将集群的出口流量重定向到本地基础架构或 AWS 云中的其他 VPC。为此,他们可以使用 AWS Transit Gateway 或 AWS Direct Connect,这样就无需在集群所在的 VPC 中部署公共子网。即使需要将出口流量定向到互联网,也可以通过 AWS Transit Gateway 连接到公共子网具有 AWS NAT 网关 和 AWS 互联网网关的 VPC。

图 2. 采用 PrivateLink 的 ROSA 私有集群
在公共和 PrivateLink 实施中,ROSA 集群都可以使用 AWS VPC 端点与集群所在的 VPC 以及所需的服务进行通信,从而与其他 AWS 服务进行交互。
连接集群
SRE 团队登录 ROSA 集群并执行管理任务时,建议使用 AWS Security Token Service (STS)。权限分配应遵循最少权限原则,确保仅分配完成任务所必需的角色。令牌是临时的且只能使用一次,因此如果需要在令牌过期后再次执行类似的任务,则必须申请新的令牌。
STS 的使用扩展到 ROSA 集群与其他 AWS 服务的连接,例如 EC2(需要为集群启动新服务器时等等)或 EBS(需要持久存储时)。
总结
采用 DevOps 方法并使用 OpenShift 等企业级 Kubernetes 平台进行应用部署,这样的现代化部署方式适用于所有类型的客户。客户可以选择在本地托管并自行管理,但如果不想自行管理,ROSA 也是一个选择。ROSA 集群可以与许多 AWS 服务交互,这有助于客户充分利用其平台。
了解更多
关于作者
Ricardo Garcia Cavero joined Red Hat in October 2019 as a Senior Architect focused on SAP. In this role, he developed solutions with Red Hat's portfolio to help customers in their SAP journey. Cavero now works for as a Principal Portfolio Architect for the Portfolio Architecture team.
