OpenShift Pipelines based on Tekton provides a Kubernetes-native CI/CD framework to design and run your pipelines. You do not need a separate CI/CD server to manage or maintain.
An important aspect of OpenShift Pipelines is that each step of the CI/CD pipeline runs in its own container thereby allowing each step to be customized as required.
A typical CI/CD pipeline is a set of tasks, and each task is a set of steps. Further, a task is run as a Kubernetes Pod, and each step of the task is a separate container in the Pod.
The diagram below will help to visualize the relationship between task, step, pipeline. and Pod.
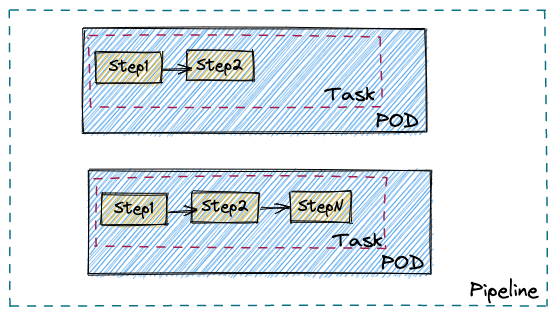
By virtue of the task running as a Kubernetes Pod, it is possible to customize each step with respect to container resource requirements, runtime configuration, security policies, attached sidecar, and others.
Let’s say you are looking for a safe way to handle one of these requirements:
- Run a task requiring additional privileges
- Run a step in the task with unsafe sysctl settings (for example, kernel.msgmax) and capture some test data
This is where the combination of OpenShift sandboxed containers and OpenShift Pipelines can help you.
With a single line change to the associated Pod template used to run the tasks, you can provide an additional isolation layer by leveraging the Kata container runtime.
The one line change is adding the following statement to the Pod template spec: runtimeClassName: kata
Sample Pod template spec
…
spec:
pipelineRef:
name: mypipeline
podTemplate:
…
runtimeClassName: kata
…
A short video demo can be viewed here:
In the remainder of the blog, we will see a complete example of using OpenShift sandboxed containers with OpenShift Pipelines. Specifically, we will use the pipelines tutorial and an example TaskRun with Kata container runtime.
Prerequisites
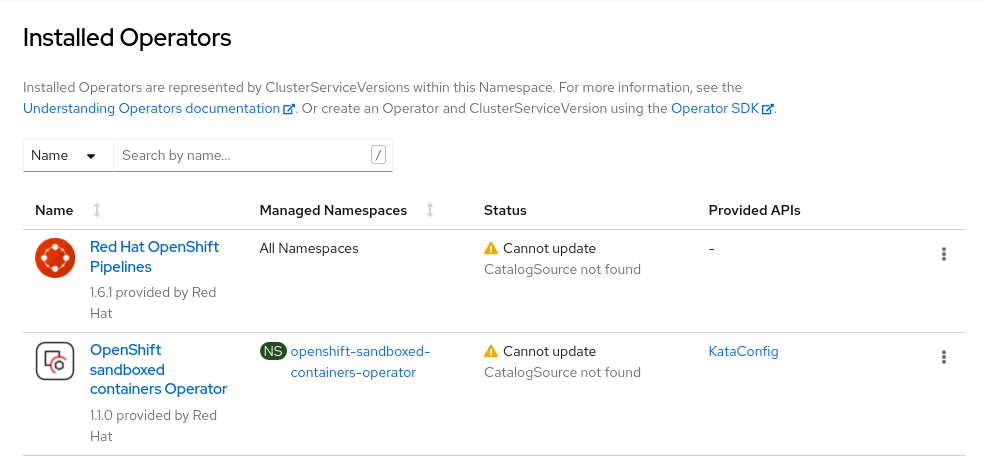
Make sure Red Hat OpenShift Pipelines Operator and OpenShift sandboxed containers Operator are installed.
Create KataConfig by following the instructions given in this doc:
Pipelines Tutorial - Using Kata runtime
Setup
$ git clone https://github.com/openshift-pipelines/pipelines-tutorial.git
$ cd pipelines-tutorial
$ ./demo.sh setup-pipeline
[...snip…]
Tasks
NAME TASKREF RUNAFTER TIMEOUT CONDITIONS PARAMS
∙ fetch-repository git-clone --- --- url: string, subdirectory: , deleteExisting: true, revision: master
∙ build-image buildah fetch-repository --- --- IMAGE: string
∙ apply-manifests apply-manifests build-image --- --- ---
∙ update-deployment update-deployment apply-manifests --- --- deployment: string, IMAGE: string
[...]
$ ./demo.sh run
INFO: Running API Build and deploy
tkn -n pipelines-tutorial pipeline start build-and-deploy -w name=shared-workspace,volumeClaimTemplateFile=01_pipeline/03_persistent_volume_claim.yaml -p deployment-name=pipelines-vote-api -p git-url=https://github.com/openshift/pipelines-vote-api.git -p IMAGE=image-registry.openshift-image-registry.svc:5000/pipelines-tutorial/pipelines-vote-api --showlog=true
? Value for param `git-revision` of type `string`? (Default is `master`) kata
Entering kata here will use the ‘kata’ branch, and the pipelines-tutorial will be using Kata containers runtime.
Verify by checking the runtimeClassName attribute in the Pod yaml.
$ oc -n pipelines-tutorial get pod -o yaml pipelines-vote-api-64c4984b9c-w2gr7 | grep -i kata
runtimeClassName: kata
$ oc -n pipelines-tutorial get pod -o yaml pipelines-vote-ui-58767bc8f4-dnlsk | grep -i kata
runtimeClassName: kata
You can see the one line change here.
Observe the resource consumption on the web console
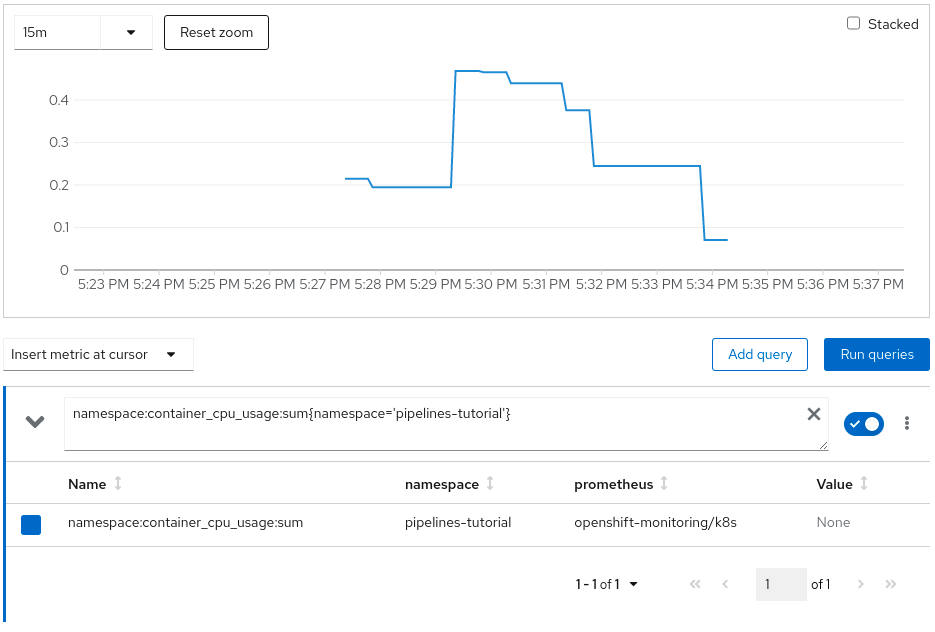
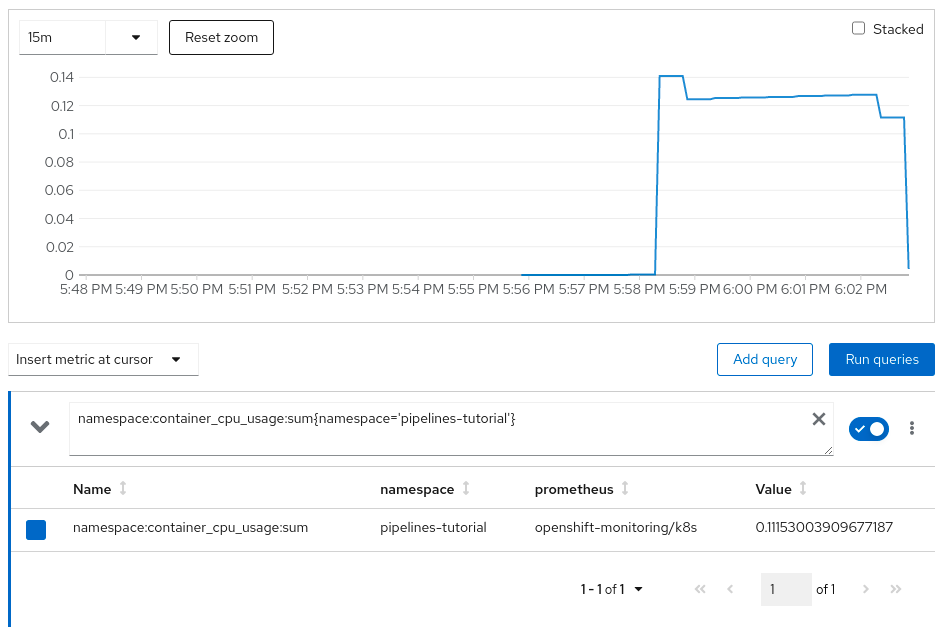
CPU Utilization:
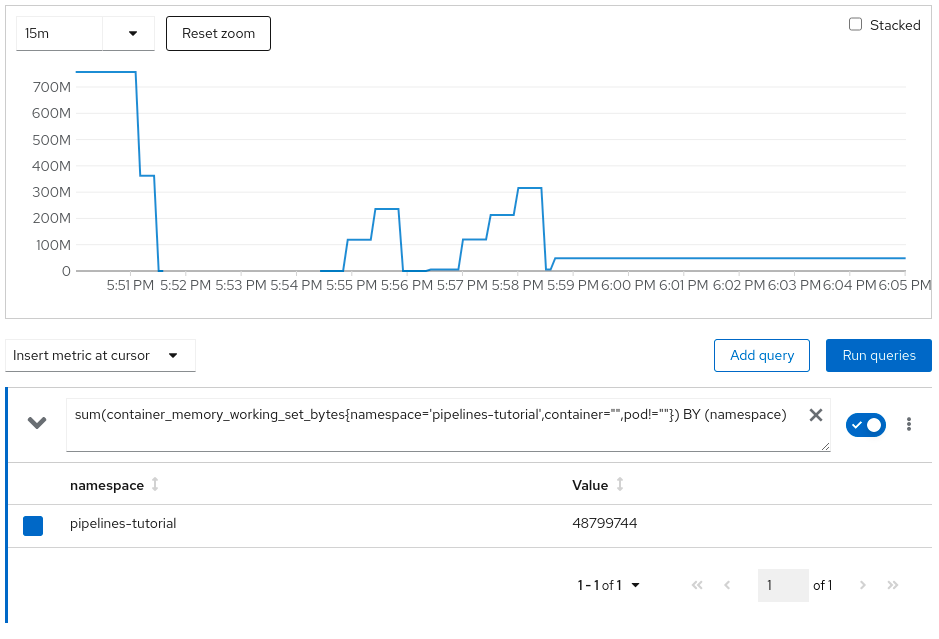
Memory Utilization:

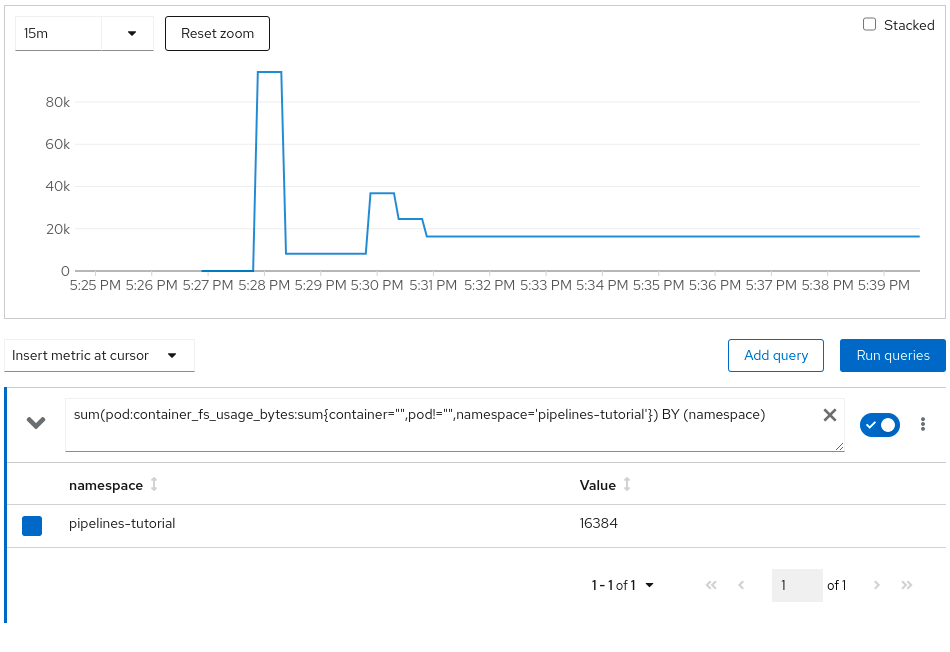
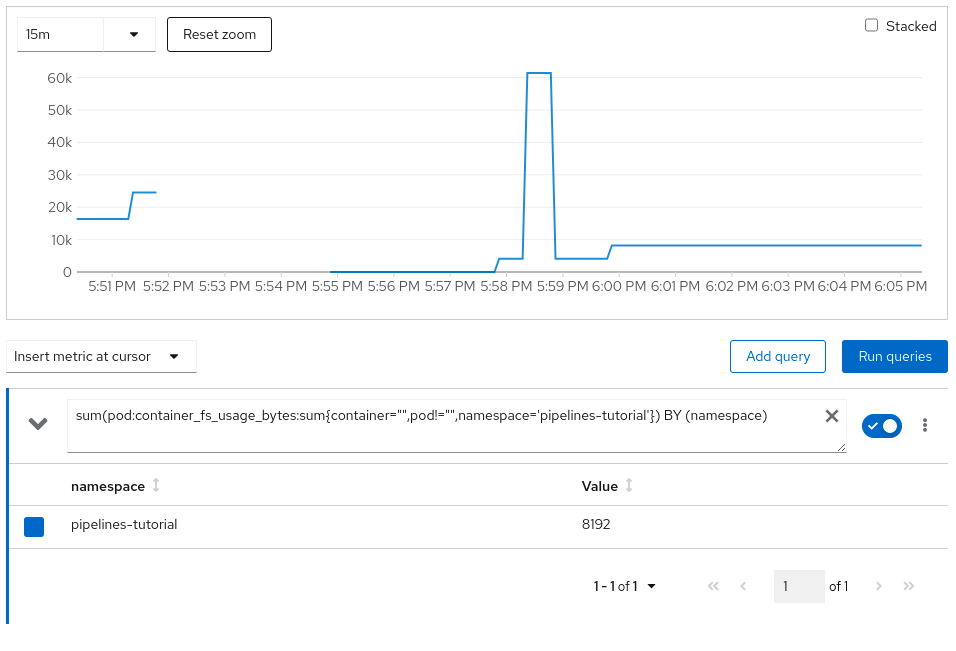
File System Utilization:
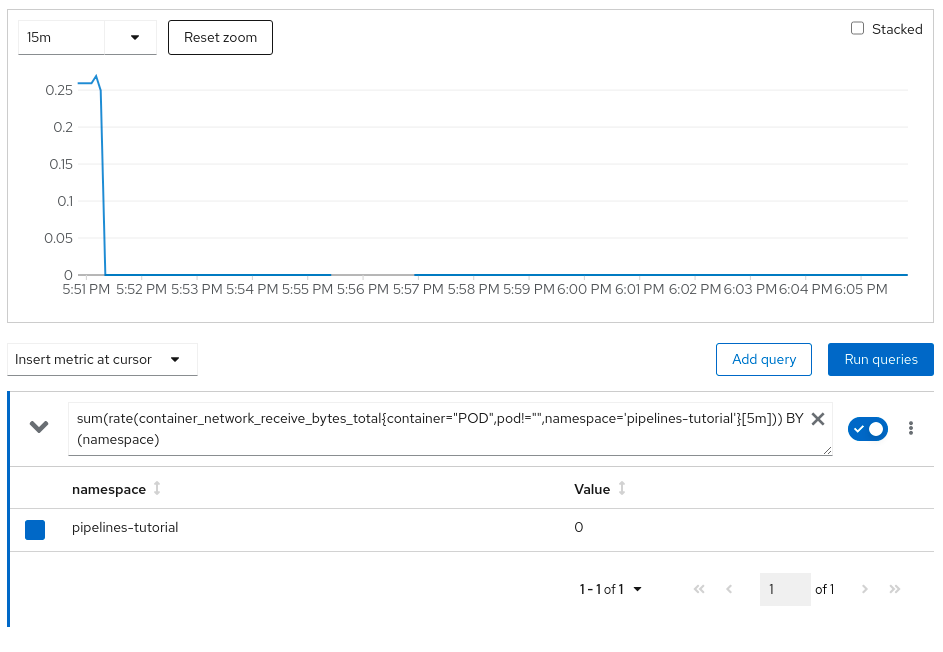
Network Utilization:

Pipelines Tutorial - default cri-o runtime
Setup
Follow the same steps as highlighted in the previous section, but enter main (or simply press ‘Enter,’ which will take default) when prompted to enter git-revision instead of kata.
Observe the resource consumption on the web console
CPU Utilization:
Memory Utilization:
File system Utilization:
Network Utilization:
Conclusion
As you can see via the pipeline demo example, providing an additional isolation layer to some of your cloud-native CI/CD tasks using Kata containers runtime is extremely easy. However, it should also be noted that this additional isolation layer comes with a small amount of resource overhead as reflected in the resource utilization charts. There is always a trade-off, and you will need to decide what is applicable for your environment.
저자 소개
Pradipta is working in the area of confidential containers to enhance the privacy and security of container workloads running in the public cloud. He is one of the project maintainers of the CNCF confidential containers project.
유사한 검색 결과
Why building fast does not guarantee success
The agentic paradox and the case for hybrid AI
The Great Stack Debate | Compiler: Stack/Unstuck
The Fractious Front End | Compiler: Stack/Unstuck
채널별 검색
오토메이션
기술, 팀, 인프라를 위한 IT 자동화 최신 동향
인공지능
고객이 어디서나 AI 워크로드를 실행할 수 있도록 지원하는 플랫폼 업데이트
오픈 하이브리드 클라우드
하이브리드 클라우드로 더욱 유연한 미래를 구축하는 방법을 알아보세요
보안
환경과 기술 전반에 걸쳐 리스크를 감소하는 방법에 대한 최신 정보
엣지 컴퓨팅
엣지에서의 운영을 단순화하는 플랫폼 업데이트
인프라
세계적으로 인정받은 기업용 Linux 플랫폼에 대한 최신 정보
애플리케이션
복잡한 애플리케이션에 대한 솔루션 더 보기
가상화
온프레미스와 클라우드 환경에서 워크로드를 유연하게 운영하기 위한 엔터프라이즈 가상화의 미래

