OpenShift is an enterprise application platform based on the Kubernetes orchestration tool. It can deploy applications from a number of sources, including prebuilt images as well as from source. In this article, I will talk about Source-to-Image (S2I) and how to automate the entire process using Git webhooks. You can follow along and try it out yourself for free at the OpenShift Interactive Learning Portal.
Source-to-Image
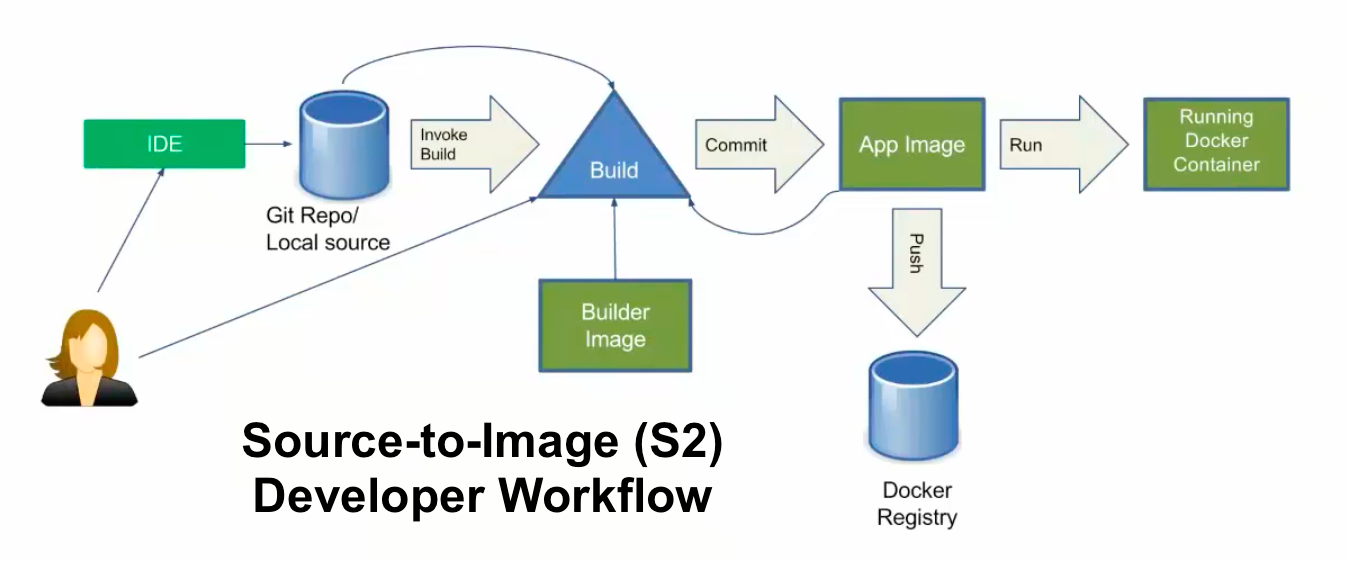
S2I is a process that takes source code for an application stored in a source control management tool like Git or SCM and puts it on a base image using BuildConfig, then deploys the application using DeploymentConfig. Below is a simple diagram that helps us to understand the entire process. In this process, if the code is updated on Git by a developer, we have to trigger a build manually by using this command:
oc start-build <build name>
However, OpenShift provides a great way to deal with the automatic triggering of the BuildConfig by using webhooks. Let's see a quick demo of it. To do so, I am using learn.openshift.com running on OpenShift 4.2 CRC.
[ You might also enjoy reading: Troubleshooting handshake errors in OpenShift ]
To launch the application using the S2I process, which creates ImageStream, BuildConfig, DeploymentConfig, and the service in one go, you can do something like this:
$ oc new-app --name=demo https://github.com/ashutoshbhakare/php
$ oc expose svc demo # to create the route
Now let's try to integrate OpenShift and GitHub by using webhooks. To achieve this, we need a webhooks URL and a secret, which authenticates our GitHub trigger to OpenShift. So whenever a developer updates the GitHub source code, it immediately triggers the build to OpenShift. Webhooks is an API call that is running on port 6443. To get the webhooks URL and secret, we can use:
$ oc describe bc demo
Which returns the output below:

In the above example, https://openshift:6443 must be replaced with our OpenShift's master URL, per my learn.openshift.com online labs.
To get the secret:
$ oc get bc demo -o yaml | grep secret
secret: N58sBgReryjBwYIBp4FV
secret: u1BaRZVDxAfvsT5lC3tX
We are going to use the second value, which is for generic webhooks: payload URL for GitHub.
Add the webhook
This was the most tricky part of the online labs.
Now let's go to GitHub and add the webhook payload URL to it. By clicking settings and the Selecting Webhooks option → Add Webhook, we will copy the entire payload URL like above and paste the secret in the text box.

This is how the GitHub and OpenShift webhooks integration successfully completed. We can test that by changing the Git code, which should result in the info below, which shows the recent deliveries.

[ Learn the basics of using Kubernetes in this free cheat sheet. ]
Wrap up
Source-to-Image (S2I) can help to automate the process of launching an application by using Git webhooks. The process can be straightforward, and you can demonstrate it yourself at the OpenShift Interactive Learning Portal.
저자 소개
Ashutosh is an open source software advocate, docker community leader, Fedora active contributor, Red Hat / SUSE Certified Instructor with 19 years of experience as a trainer and consultant.
유사한 검색 결과
[node:rh-smart-meta-title]
Simplify Red Hat Enterprise Linux provisioning in image builder with new Red Hat Lightspeed security and management integrations
Can Kubernetes Help People Find Love? | Compiler
Scaling For Complexity With Container Adoption | Code Comments
채널별 검색
오토메이션
기술, 팀, 인프라를 위한 IT 자동화 최신 동향
인공지능
고객이 어디서나 AI 워크로드를 실행할 수 있도록 지원하는 플랫폼 업데이트
오픈 하이브리드 클라우드
하이브리드 클라우드로 더욱 유연한 미래를 구축하는 방법을 알아보세요
보안
환경과 기술 전반에 걸쳐 리스크를 감소하는 방법에 대한 최신 정보
엣지 컴퓨팅
엣지에서의 운영을 단순화하는 플랫폼 업데이트
인프라
세계적으로 인정받은 기업용 Linux 플랫폼에 대한 최신 정보
애플리케이션
복잡한 애플리케이션에 대한 솔루션 더 보기
가상화
온프레미스와 클라우드 환경에서 워크로드를 유연하게 운영하기 위한 엔터프라이즈 가상화의 미래
