In a previous Red Hat article, VP of Red Hat Product Security, Vincent Danen, discussed the question "Do all vulnerabilities really matter?" He emphasized that "a software vulnerability has the potential to be exploited by miscreants to harm its user." The key word here is "potential". If the potential for exploitation is high, or if an exploit for a vulnerability is already in use in the wild, then these vulnerabilities pose a greater risk and must be prioritized and addressed promptly.
Red Hat uses CISA as a source for known exploited vulnerabilities
The Cybersecurity and Infrastructure Security Agency (CISA) leads the US national effort to understand, manage, and reduce risk to their cyber and physical infrastructure. CISA maintains a Known Exploited Vulnerabilities (KEV) catalog, otherwise known as the CISA catalog.
In November 2021, CISA issued the binding operational directive CISA BOD 22-01. This directive requires that all US Government federal agencies (USG) identify and remediate all vulnerabilities listed in the CISA catalog in their information systems. Additionally, this catalog is available to the public so other non-USG customers can be aware of the listed exploited vulnerabilities and seek immediate remediations. The vulnerabilities listed have been observed to be exploited in the wild, presenting an elevated risk.
In response, Red Hat created a program to resolve vulnerabilities added to the KEV list as quickly as possible. This program helps Red Hat to continue strengthening our security posture across our software portfolio while maintaining our reputation as a trustworthy partner.
How well did Red Hat remediate exploited in the wild vulnerabilities?
As described in CISA BOD-22-01, CISA has three main criteria for adding vulnerabilities to the KEV:
- A Common Vulnerabilities and Exposures (CVE) ID
- Clear remediation guidance
- Reliable evidence of exploitation in the wild
In 2023, the CISA catalog included 20 CVEs that impacted Red Hat products. The following table displays the breakdown by severity.
Severity rating | Total Red Hat Flaw counts | In the wild exploitation | In the wild exploitation as a percentage of total flaw counts |
|---|---|---|---|
All | 1644 | 20 | 1.2% |
Critical | 12 | 1 | 5.3% |
Important | 336 | 15 | 4.5% |
Moderate | 1047 | 3 | 0.3% |
Low | 247 | 1 | 0.4% |
The amount of vulnerabilities exploited in the wild was fairly low, accounting for 1.2% of the total flaws that impacted Red Hat in 2023. Once Red Hat is notified that a CVE is added to the CISA catalog, Red Hat provides a fix for the vulnerability within an average of 10 calendar days (notably faster than the 21 calendar days that CISA gives for the vulnerability to be resolved).
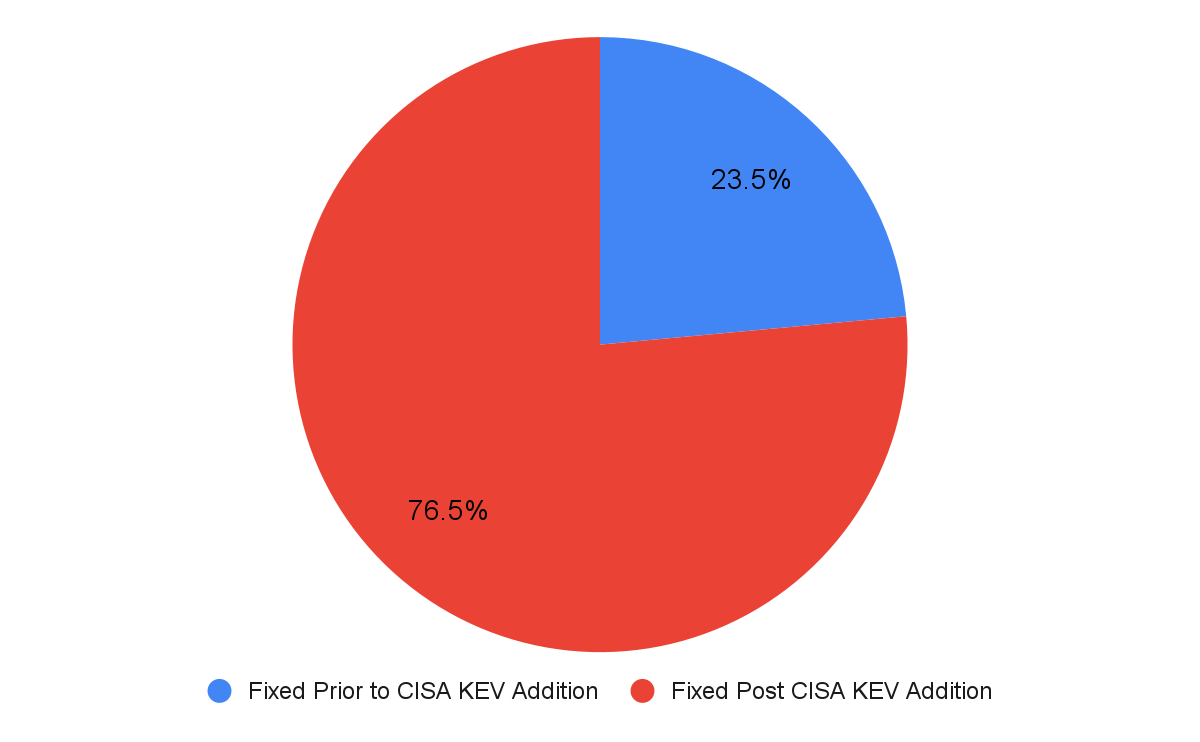
It is also important to note that Red Hat has released errata for approximately 24% of these Exploit CVEs before they were added to the CISA catalog.
More than half of the exploited in the wild vulnerabilities pertain to the WebKitGTK package. WebKit is one of the three big web rendering engines. The exploit primarily targets iOS users and sometimes macOS users, as well as any software using the JavaScript Just in Time (JIT) compiler. To better enhance the security of Red Hat software, Red Hat has disabled the JavaScript JIT mechanism in the 8.8 z-stream and 9.2 z-stream RHEL releases. This action is expected to cut down on the volume of WebKit vulnerabilities by half going forward.
Security awareness
Red Hat Product Security's awareness and visibility into reported exploited vulnerabilities enable us to proactively address rising threats and fix vulnerabilities that truly matter. These actions allow Red Hat to remain a trusted vendor and partner to our customers. At Red Hat, openness and transparency are embedded in our culture. This culture of transparency influences our customer interactions and allows us to be a trusted partner. Sharing pertinent information makes our community well-informed and well-versed, especially when it comes to security.
저자 소개
Leonardo Firicano joined Red Hat in 2021 as a Business Analyst for Product Security. Leo brings his experience and skills to Product Security, having held previous roles as a technical business analyst, a project analyst, and a data analyst within the finance industry. Leo holds a bachelor’s degree in Finance and Information Systems from Suffolk University and an MBA from Northeastern University.
Marco Benatto is a Senior Product Security Engineer at Red Hat and experienced Linux developer who has worked with several userspace applications and is currently focused on kernel-space and filesystems, with a background in memory management.
유사한 검색 결과
Confidential clusters for Red Hat OpenShift: Developer Preview now available on Microsoft Azure with AMD SEV-SNP
Integrating Red Hat Lightspeed with CrowdStrike for enhanced malware detection coverage
Collaboration In Product Security | Compiler
Keeping Track Of Vulnerabilities With CVEs | Compiler
채널별 검색
오토메이션
기술, 팀, 인프라를 위한 IT 자동화 최신 동향
인공지능
고객이 어디서나 AI 워크로드를 실행할 수 있도록 지원하는 플랫폼 업데이트
오픈 하이브리드 클라우드
하이브리드 클라우드로 더욱 유연한 미래를 구축하는 방법을 알아보세요
보안
환경과 기술 전반에 걸쳐 리스크를 감소하는 방법에 대한 최신 정보
엣지 컴퓨팅
엣지에서의 운영을 단순화하는 플랫폼 업데이트
인프라
세계적으로 인정받은 기업용 Linux 플랫폼에 대한 최신 정보
애플리케이션
복잡한 애플리케이션에 대한 솔루션 더 보기
가상화
온프레미스와 클라우드 환경에서 워크로드를 유연하게 운영하기 위한 엔터프라이즈 가상화의 미래

