하이브리드 클라우드 보안은 단순히 어려워지는 단계를 넘어 한계점에 도달하고 있습니다. 보안은 항상 결승선 없는 경쟁이었지만, Red Hat의 2026년 State of Cloud-Native Security 리포트에 따르면 현재 많은 조직이 통제된 혼돈의 악순환에 빠져 있습니다. 이러한 상황에서 벗어나려면 팀은 사후 대응적인 문제 해결 수준을 넘어 보안을 병목 구간에서 표준으로 전환하는 기본 보안 관행 및 정책에 전략의 기반을 두어야 합니다.
클라우드 네이티브 인시던트의 현실
이 리포트는 보안 인시던트가 이제 거의 모든 조직이 겪는 보편적인 경험이 되었다는 냉정한 기준을 제시합니다. 97%의 조직이 지난 1년 동안 최소 1건의 클라우드 네이티브 보안 인시던트를 경험했다고 보고했습니다. 이러한 인시던트는 정교한 일회성 공격만이 아닙니다. 오히려 "일상적인 실수"로 인해 발생하는 경우가 많습니다.
가장 자주 보고되는 인시던트 유형은 다음과 같습니다.
- 잘못 구성된 인프라 또는 서비스(78%): 보안 노출의 주요 원인이며, 주로 복잡한 환경에서의 수동 오류로 인해 발생합니다.
- 알려진 취약점: 워크로드가 "알려진 불량" 코드로 배포되어 피할 수 있는 위험에 노출되고 있습니다.
- 무단(Unauthorized) 액세스: 민감한 데이터 노출로 빈번하게 이어지는 지속적인 운영상의 장애 요인입니다.
이러한 인시던트는 IT 부서를 넘어 실질적인 비즈니스 비용을 초래합니다. 조직의 74%가 보안 우려로 인해 지난 12개월 동안 애플리케이션 배포가 지연되거나 늦춰졌습니다. 응답자의 92%는 배포 지연 외에도 보안 문제 해결 시간 증가(52%), 개발자 생산성 저하(43%), 고객 신뢰 상실(32%) 등 상당한 영향을 경험했습니다. 간단히 말해, 보안은 더 이상 단순한 기술적 체크리스트가 아니라 비즈니스 민첩성을 위협하는 주요 위험 요소입니다.
캡션: 설문조사 대상 조직에 “향후 12개월 동안 다음 각 요소가 조직의 클라우드 네이티브 보안 전략에 어느 정도 영향을 미칠 것으로 예상하십니까? (다소 또는 강력한 영향)”라고 질문했을 때의 응답 결과입니다.
성숙도의 역설: 자신감과 실제 전략의 차이
이 리포트에서 가장 주목할 만한 결과 중 하나는 인지된 준비 상태와 실제 전략 사이의 격차입니다. 56%의 조직은 일상적인 보안 태세를 "매우 선제적"이라고 설명합니다. 하지만 실제로 성숙하고 명확하게 정의된 클라우드 네이티브 보안 전략을 보유한 조직은 39%에 불과합니다.
이는 팀이 미래 지향적인 태세를 지향하지만, 실제로는 많은 조직이 상황에 맞춰 "임기응변"으로 대응하고 있음을 시사합니다. 실제로 약 22%의 조직이 어떠한 명확한 전략도 없이 운영되고 있습니다. 이러한 체계의 부족은 다음과 같은 보안 가드레일을 일관되게 채택하지 못하는 결과로 이어집니다.
- Identity와 액세스 관리(IAM) : ID가 핵심 제어 수단으로 널리 인식됨에 따라 약 75%의 도입률을 보입니다.
- 컨테이너 이미지 서명 : 소프트웨어 무결성을 위해 이 기능을 구현한 조직은 전체의 절반 정도에 불과합니다.
- 런타임 보호 : 구현이 여전히 불완전하여 많은 팀이 의도적인 거버넌스보다는 기본 설정에 의존하고 있습니다.
이 데이터는 성숙도가 높을수록 성과가 크다는 점을 강조합니다. 잘 정의된 전략을 갖춘 조직은 고급 가드레일을 도입할 가능성이 훨씬 높으며, 성숙도가 낮은 조직에 비해 소프트웨어 공급망 보안에 대해 61%라는 훨씬 높은 신뢰도를 보였습니다.
투자 동향의 변화: 자동화 및 공급망
조직들은 이러한 격차를 인식하고 2026년 예산을 재조정하고 있습니다. 초점이 개별 포인트 툴에서 플랫폼 통합으로 이동하고 있으며, 보안을 소프트웨어 라이프사이클에 직접 구축하는 추세입니다.
향후 1~2년간의 주요 투자 우선순위는 다음과 같습니다.
- DevSecOps 자동화 : 60% 이상의 조직이 CI/CD 파이프라인 내 보안 자동화에 투자할 계획입니다. 목표는 수동 '게이트'에서 '코드형 보안'으로 전환하여 인적 오류를 줄이는 것입니다.
- 소프트웨어 공급망 보안 : 56%의 조직이 이 영역을 우선순위로 두고 있습니다. 공급망 공격이 급증함에 따라 SBOM(Software Bills of Materials) 및 출처 확인을 통해 오픈소스 종속성과 컨테이너 이미지를 검증하는 것이 시급해졌습니다.
- 런타임 보호 : 응답자의 54%는 크립토재킹이나 악성 컨테이너 동작과 같은 활성 위협을 실시간으로 감지하고 차단할 수 있는 방어 체계를 확장할 계획입니다.
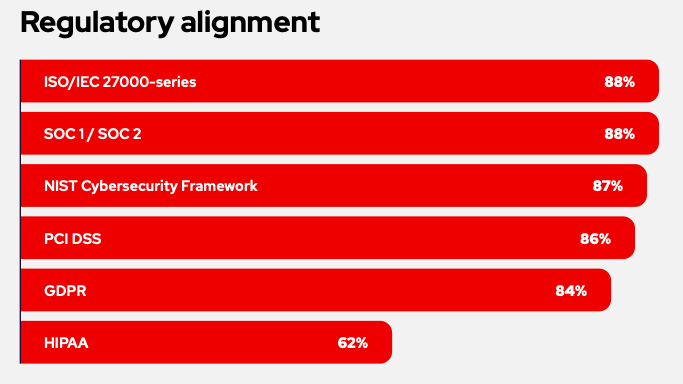
컴플라이언스는 더 이상 뒷전으로 밀려날 문제가 아닙니다. 64%의 조직이 2026년 투자 결정에서 EU 사이버 복원력법(CRA)이 주요 동인이 될 것으로 예상합니다. 이로 인해 보안 거버넌스는 '있으면 좋은 것'에서 이사회 수준의 필수 요건으로 전환됩니다.
새로운 리스크 영역: AI 및 클라우드 보안
2026년, AI는 클라우드 네이티브 팀에 양날의 검이 되었습니다. 58%의 조직은 AI 도입이 현재 보안 계획의 핵심 동인이라고 답했지만, 실제 거버넌스는 구현 속도보다 '위험할 정도로 뒤처져' 있습니다.
보고서에 따르면 클라우드 환경의 생성형 AI와 관련하여 거의 모든 응답자가 우려를 나타냈으며, 96%의 응답자가 상당한 우려를 표명했습니다. 이러한 우려는 단순히 이론적인 것이 아니며, 다음과 같은 세 가지 특정 리스크를 중심으로 발생합니다.
- 일반적인 우려 사항: 응답자의 96%가 클라우드 환경의 생성형 AI에 대해 우려하고 있습니다.
- 주요 우려 사항: 여기에는 민감한 데이터 노출, 승인 없이 사용되는 섀도우 AI 툴, 안전하지 않은 타사 AI 서비스 통합 등이 포함됩니다.
거버넌스 격차: 이러한 우려에도 불구하고 조직의 59%는 문서화된 내부 AI 사용 정책이나 거버넌스 프레임워크를 갖추고 있지 않습니다.
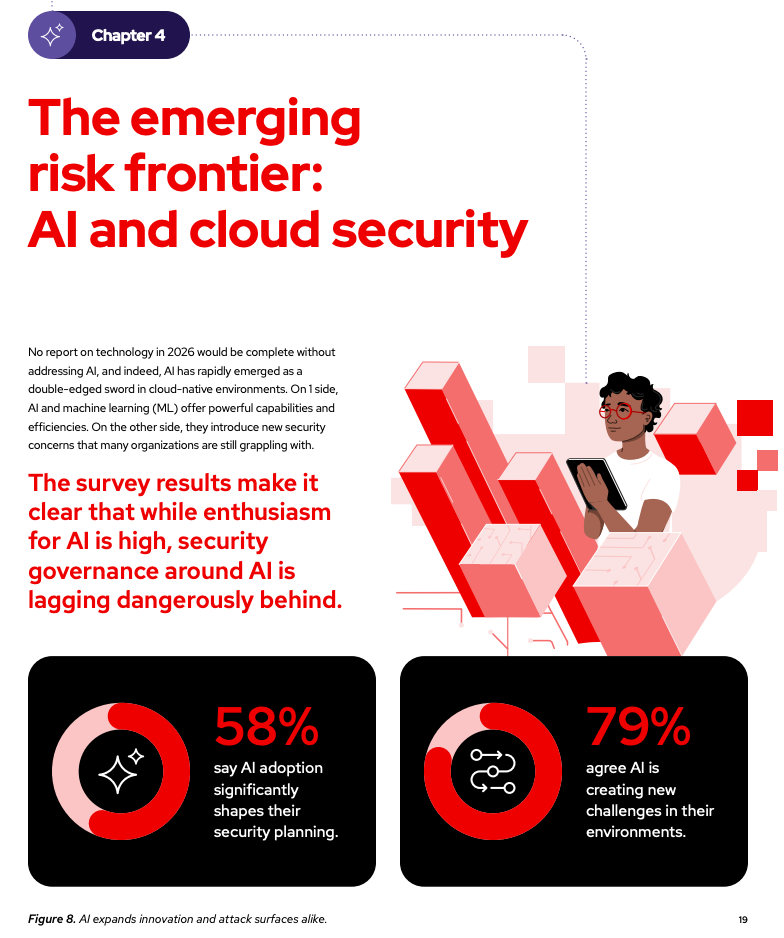
명확한 규칙이 없으면 AI 기반 동작이 구성을 변경하거나 정상적인 프로세스 외부에 독점 코드를 유출할 위험이 있으며, 이는 결과적으로 기존 ID 및 공급망 리스크를 증폭시킵니다.
2026년 데이터 기반 권장 사항
이 리포트는 클라우드 네이티브 혁신 속도가 기존 보안을 공식적으로 앞질렀다는 명확한 시사점을 제시하며 마무리됩니다. 성숙도의 역설을 해결하기 위해 조직은 임시방편적인 대응에서 벗어나 구조화된 플랫폼 중심 접근 방식을 도입해야 합니다.
2026년을 위한 5가지 핵심 조치
- 공식 전략 수립: 조직은 사후 대응에서 사전 예방 태세로 전환하는 구조화된 경로를 마련하여 임시방편적인 대응 수준을 넘어서야 합니다.
- 가드레일 및 자동화 포함: 보안은 플랫폼의 기본 보안 요소로 포함되어야 하며, DevOps 또는 플랫폼 엔지니어링 팀이 개발자에게 마찰을 주지 않고 확장할 수 있도록 실행해야 합니다.
- 공급망 무결성 우선순위 지정: 필수 이미지 서명 및 종속성 검사를 구현하세요. 한 응답자가 언급했듯이 모두가 오픈소스를 사용하지만, 종속성을 검사하거나 서명하는 경우는 거의 없습니다. 이러한 일반적인 상황에서 예외가 되는 것이 회복 탄력성 확보에 매우 중요합니다.
- 피드백 루프 구축: 관측성과 보안 데이터를 통합하여 런타임 위협 감지에서 얻은 인사이트를 개발 프로세스에 피드백하고 가장 중요한 수정 사항의 우선순위를 지정하세요.
- 지금 바로 AI 사용 관리 시작: 조직은 외부 규제가 마련될 때까지 기다릴 수 없습니다. 지금 즉시 다기능 팀을 구성하여 허용 가능한 AI 사용 및 데이터 처리에 관한 가이드라인을 수립해야 합니다.
2026년에 보안은 더 이상 추가 기능이 아닌 클라우드 네이티브 아키텍처의 핵심 구성 요소입니다. 보안을 비용 센터가 아닌 비즈니스 민첩성의 주요 동인으로 취급하는 조직이 성공할 것입니다.
리소스
적응형 엔터프라이즈: AI 준비성은 곧 위기 대응력
저자 소개
Red Hatter since 2018, technology historian and founder of The Museum of Art and Digital Entertainment. Two decades of journalism mixed with technology expertise, storytelling and oodles of computing experience from inception to ewaste recycling. I have taught or had my work used in classes at USF, SFSU, AAU, UC Law Hastings and Harvard Law.
I have worked with the EFF, Stanford, MIT, and Archive.org to brief the US Copyright Office and change US copyright law. We won multiple exemptions to the DMCA, accepted and implemented by the Librarian of Congress. My writings have appeared in Wired, Bloomberg, Make Magazine, SD Times, The Austin American Statesman, The Atlanta Journal Constitution and many other outlets.
I have been written about by the Wall Street Journal, The Washington Post, Wired and The Atlantic. I have been called "The Gertrude Stein of Video Games," an honor I accept, as I live less than a mile from her childhood home in Oakland, CA. I was project lead on the first successful institutional preservation and rebooting of the first massively multiplayer game, Habitat, for the C64, from 1986: https://neohabitat.org . I've consulted and collaborated with the NY MOMA, the Oakland Museum of California, Cisco, Semtech, Twilio, Game Developers Conference, NGNX, the Anti-Defamation League, the Library of Congress and the Oakland Public Library System on projects, contracts, and exhibitions.
유사한 검색 결과
과거의 운영 방식에서 벗어나 IT의 미래 구축
추론에서 에이전트까지: Red Hat AI 3.4를 통해 기업의 AI 확장
Technically Speaking | Build a production-ready AI toolbox
Technically Speaking | Platform engineering for AI agents
채널별 검색
오토메이션
기술, 팀, 인프라를 위한 IT 자동화 최신 동향
인공지능
고객이 어디서나 AI 워크로드를 실행할 수 있도록 지원하는 플랫폼 업데이트
오픈 하이브리드 클라우드
하이브리드 클라우드로 더욱 유연한 미래를 구축하는 방법을 알아보세요
보안
환경과 기술 전반에 걸쳐 리스크를 감소하는 방법에 대한 최신 정보
엣지 컴퓨팅
엣지에서의 운영을 단순화하는 플랫폼 업데이트
인프라
세계적으로 인정받은 기업용 Linux 플랫폼에 대한 최신 정보
애플리케이션
복잡한 애플리케이션에 대한 솔루션 더 보기
가상화
온프레미스와 클라우드 환경에서 워크로드를 유연하게 운영하기 위한 엔터프라이즈 가상화의 미래
