According to our recent survey of IT decision-makers, security is the biggest area of concern relating to container adoption, with security issues causing application deployment delays among 54% of the respondents.
Kubernetes is, first and foremost, a tool for development and DevOps teams to accelerate and scale containerized application development, deployment, and management. Providers such as Red Hat, Amazon, Microsoft, and Google have added security features to enhance the base capabilities in Kubernetes. At the same time, commercial security vendors have stepped up to offer enterprise-ready security solutions for more advanced use cases.
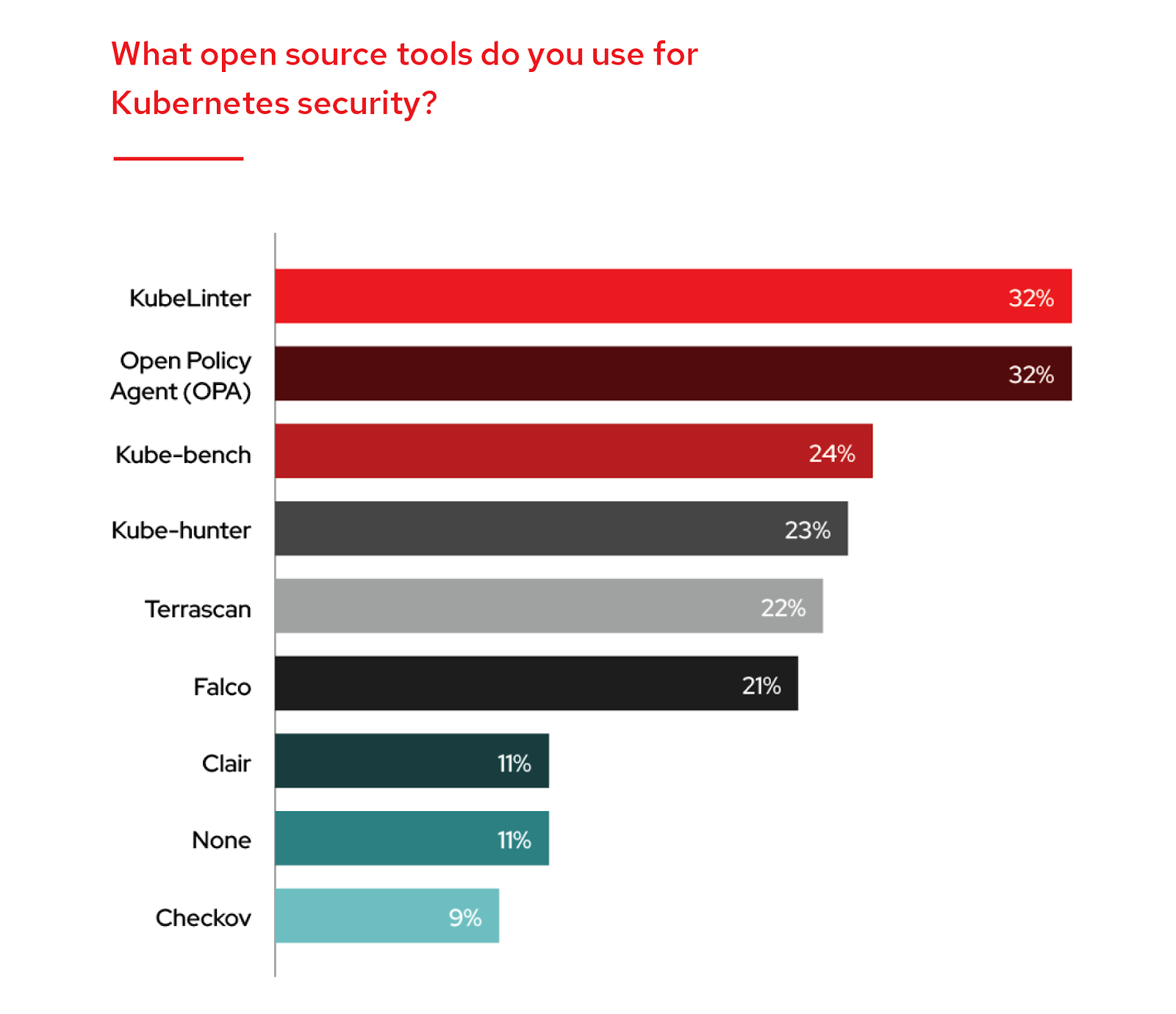
In parallel, the Kubernetes community has been very active in releasing open source security tools to fill in the security gaps present in Kubernetes. Customers have a rich selection of open source security tools to choose from, and our survey results show that no single open source security tool dominates the Kubernetes security market.
Below, you will find the top eight most popular open source Kubernetes security tools identified by our survey respondents.
1: Open Policy Agent (OPA)
32% of respondents secure Kubernetes with the Open Policy Agent (OPA). While OPA is a general-purpose policy engine, it is a very powerful tool for enforcing context-aware security policies. With the deprecation of Pod Security Policy initiated as of Kubernetes v.1.21 (and complete removal by v.1.25), many organizations will likely turn to OPA to fill in that gap.
2: KubeLinter
Tied for first place, KubeLinter is a static analysis tool that scans YAML files and Helm charts. KubeLinter analyzes Kubernetes YAML files and Helm charts and checks them against a variety of best practices, with a focus on production readiness and security.
KubeLinter ships with default checks, designed to give you useful information about your Kubernetes YAML files and Helm charts. This helps teams check early and often for security misconfigurations and DevOps best practices. Some common examples of these include running containers as a non-root user, enforcing least privilege, and storing sensitive information only in secrets.
3: Kube-bench
Nearly a quarter of respondents use Kube-bench, a tool that audits Kubernetes settings against security checks recommended in the CIS Benchmark for Kubernetes. The scans are configured using YAML files, and the tool itself is written in Go, a familiar language to Kubernetes developers.
This tool is particularly useful when self-managing the control plane components.
4: Kube-hunter
Built by the same team behind Kube-bench, Kube-hunter looks for exploitable security weakness in Kubernetes clusters. One of the more useful features of Kube-hunter is the ability to exploit the vulnerabilities it discovers to look for further exploits. 23% of respondents use Kube-hunter.
5: Terrascan
Built on top of OPA, Terracan is an open source static code analyzer for Infrastructure as Code that is used by 22% of respondents. With over 500+ Policies for security best practices across various applications, including Terraform, Kubernetes (JSON/YAML), AWS, Azure, GCP, Kubernetes, and GitHub, Terrascan can detect security vulnerabilities and compliance violations and mitigate risks before provisioning infrastructure.
6: Falco
The only open source tool in this list that is built for runtime security, Falco is used by 21% of respondents to protect running containerized applications in Kubernetes. Falco also provides security policies that use contextual data from Kubernetes and kernel events to detect anomalous application behavior indicative of a threat.
7: Clair
Clair is an open source security tool used for scanning container images for known vulnerabilities. Clair is a static analysis tool, so it will not be able to detect vulnerabilities at runtime. Clair is used by 11% of respondents.
8: Checkov
Similar to Terrascan, Checkov is a static code analyzer for Infrastructure as code that is used by 9% of respondents. The latest version of Chekov introduced context-based analysis. It detects misconfigurations using graph-based scanning of cloud infrastructure that is provisioned with applications such as Terraform, Terraform plan, Cloudformation, Kubernetes, Dockerfile, Serverless, or ARM Templates.
It should be noted that while most respondents use at least one open source security tool for Kubernetes, nearly 1 in 10 have opted against using any open source security tool.
Sobre o autor
Ajmal Kohgadai is Principal Product Marketing Manager for Red Hat Advanced Cluster Security for Kubernetes. Prior to its acquisition by Red Hat, he was the Director of Product Marketing and Growth at StackRox, a leading Kubernetes security company.
Mais como este
OpenShift: integração consistente para a empresa híbrida
Reforçada, pronta e sem custo: a segurança para containers evoluiu
Collaboration In Product Security | Compiler
Keeping Track Of Vulnerabilities With CVEs | Compiler
Navegue por canal
Automação
Últimas novidades em automação de TI para empresas de tecnologia, equipes e ambientes
Inteligência artificial
Descubra as atualizações nas plataformas que proporcionam aos clientes executar suas cargas de trabalho de IA em qualquer ambiente
Nuvem híbrida aberta
Veja como construímos um futuro mais flexível com a nuvem híbrida
Segurança
Veja as últimas novidades sobre como reduzimos riscos em ambientes e tecnologias
Edge computing
Saiba quais são as atualizações nas plataformas que simplificam as operações na borda
Infraestrutura
Saiba o que há de mais recente na plataforma Linux empresarial líder mundial
Aplicações
Conheça nossas soluções desenvolvidas para ajudar você a superar os desafios mais complexos de aplicações
Virtualização
O futuro da virtualização empresarial para suas cargas de trabalho on-premise ou na nuvem