This is one story of how Red Hat Insights created a new recommendation to address a high impact vulnerability that might affect Red Hat customers. Red Hat Insights does this regularly for issues that involve Red Hat products, but what makes this one interesting is that it shows that Red Hat Insights can alert on high-visibility issues that are not delivered by Red Hat.
In this case, a 3rd party vulnerability was made public on September 16. Red Hat developed and tested a detection mechanism for the issue, then created a series of new Insights recommendations to enable our customers to detect it.
This answers two of the common questions we get about the Advisor service that is one of the services offered as a part of Red Hat Insights - how are new recommendations made, and how fast can they be created?

Red Hat Insights is a managed service that continuously analyzes platforms and applications to help enterprises manage hybrid cloud environments. Insights uses predictive analytics and deep domain expertise to reduce complex operational tasks from hours to minutes. Insights is included with your subscriptions for Red Hat Enterprise Linux, Red Hat OpenShift, and Red Hat Ansible Automation Platform.
The Advisor service is one of the most well-known services featured in Insights. This is the original Insights service where we take the knowledge and findings from Red Hat support and turn them into actionable and proactive recommendations through the Insights analytics. Insights also has a Vulnerability service, but in this instance we have a security issue that isn’t related to a CVE (Common Vulnerabilities and Exposures) in the Red Hat database. We include this issue in the Advisor service only.
How does a new recommendation get created? Let’s walk through an example using what just happened.
On September 16, news broke of an “Open Management Infrastructure Remote Code Execution Vulnerability.” Linux servers attached to certain Microsoft Azure services are exposed to this vulnerability. An HTTP/S listening port could allow remote code execution and provide root access to a server. This is a severe bug and many Linux systems, including Red Hat Enterprise Linux (RHEL) systems are affected. This is also an issue introduced in software that is not maintained by Red Hat. We want to make sure our customers are aware of it so that they can take appropriate action to protect their data and defend themselves from malevolent actors.
Once Red Hat was made aware of this vulnerability, we began assessing the impact. We got to work trying to figure out how we could make our customers aware of the problem. We immediately engaged in our process for creating a new insights recommendation for identifying the security vulnerability.
Red Hat teams around the globe worked to duplicate the exploit and document the method to find at-risk servers. A short time later Red Hat was able to create and enable new Insights recommendations highlighting multiple resolution options for Red Hat Enterprise Linux customers affected by this vulnerability.
This resulted in creating, testing, and implementing five recommendations for this issue with varying criticality based on the analysis performed by Insights.
This information will let you sort the systems and address the most critical issues based on your company’s needs.
-
If we detect that a vulnerable version of the Open Management Infrastructure (OMI) software is installed, but doesn’t appear to be running.
-
If we detect that a vulnerable version of the OMI software is installed and the process is running or the service is enabled.
-
If we detect that a vulnerable version of the OMI software is installed and is listening for connections.
-
If we detect that a vulnerable version of the OMI software is installed, is listening, and the network socket is externally accessible.
-
If we detect that a vulnerable version of the OMI software was installed by a method other than rpm. Since we can’t check the OMI software version we default to critical out of an overabundance of caution.
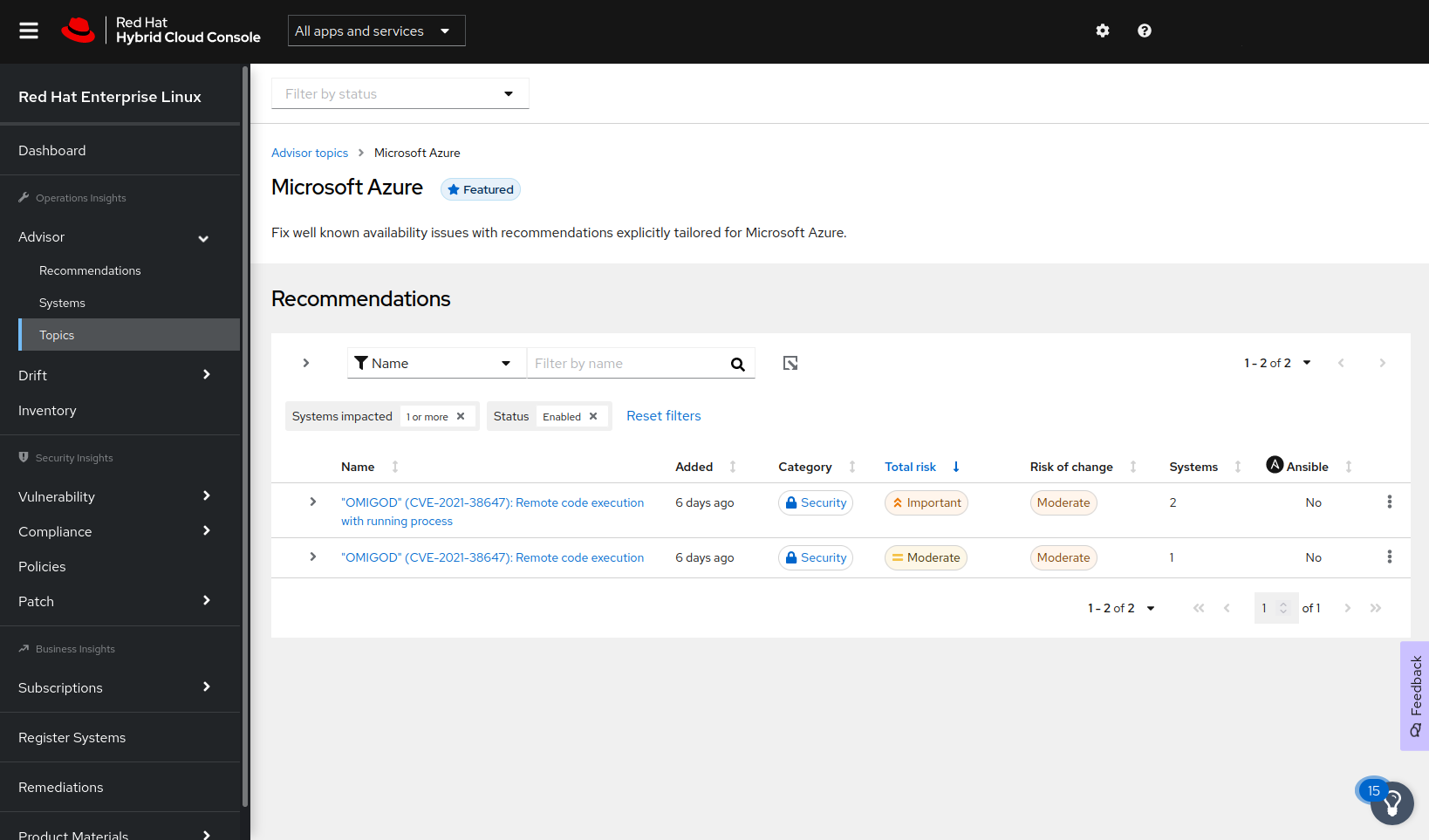
If you are running RHEL in Azure, please check the Insights Microsoft Azure topic as soon as possible. If you are impacted by this issue, you’ll see it listed in the list of recommendations.
If the problem does not affect you, you will need to clear the “Systems impacted 1 or more” filter to see the new recommendations listed.
Microsoft is providing remediation guidance for this issue on the Microsoft Security Response Center. This is an evolving situation and users should check the Microsoft Security Response Center for updates.
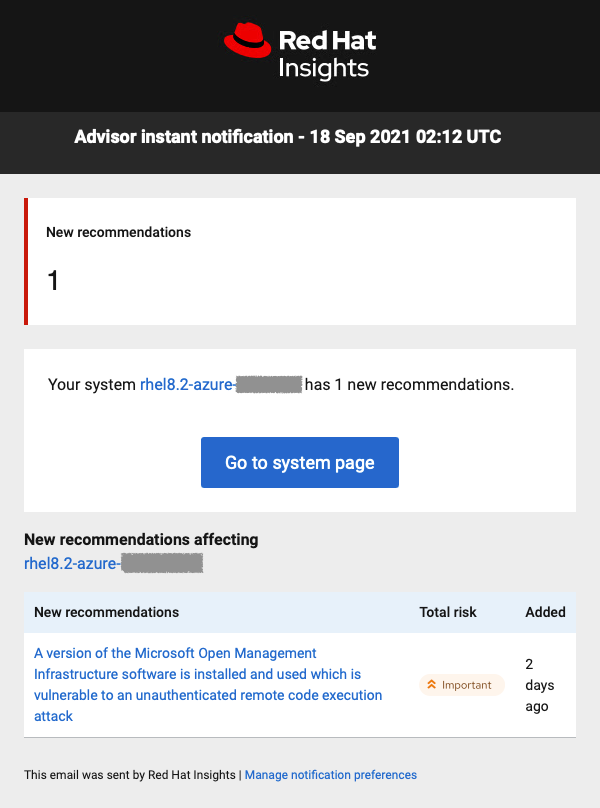
If you are already using Insights and if you have opted in to email notifications, then you would have already received an email notification about any impacted systems. Here is an example one of our team members received:
Not using Insights yet? We hope you will try it!
Registration is fast and easy. More information about how to register to Insights can be found within Insights or on the Red Hat Insights Get Started page.
Do you have questions about security and how Insights handles metadata? All of that information can be found on our Insights Data & Application Security page.
We think this is an excellent example of Red Hat’s focus on the customer: The predictive and proactive analysis of Red Hat Insights and the Hybrid Cloud Console at cloud.redhat.com enables them to better manage unexpected vulnerabilities and potential exploits.
Even if you aren’t impacted by this specific issue, it is a great example of the value that you receive from the Red Hat subscription and included capabilities like Red Hat Insights.
For more information about the OMI Vulnerability, visit the Microsoft Threat Intelligence Center blog, Hunting for OMI Vulnerability Exploitation with Azure Sentinel.
저자 소개
John Spinks is a Senior Principal Technical Marketing Manager for Red Hat. He acts as a subject matter expert for Red Hat Management products including Satellite and Insights. Previous experience includes almost 10 years as a Technical Marketing Engineer for NetApp in RTP, NC.
유사한 검색 결과
사이버 보안에서 AI의 4가지 활용 사례
생명력을 얻은 신경계: 소버린 클라우드가 통신사의 진정한 제2막인 이유
Collaboration In Product Security | Compiler
Keeping Track Of Vulnerabilities With CVEs | Compiler
채널별 검색
오토메이션
기술, 팀, 인프라를 위한 IT 자동화 최신 동향
인공지능
고객이 어디서나 AI 워크로드를 실행할 수 있도록 지원하는 플랫폼 업데이트
오픈 하이브리드 클라우드
하이브리드 클라우드로 더욱 유연한 미래를 구축하는 방법을 알아보세요
보안
환경과 기술 전반에 걸쳐 리스크를 감소하는 방법에 대한 최신 정보
엣지 컴퓨팅
엣지에서의 운영을 단순화하는 플랫폼 업데이트
인프라
세계적으로 인정받은 기업용 Linux 플랫폼에 대한 최신 정보
애플리케이션
복잡한 애플리케이션에 대한 솔루션 더 보기
가상화
온프레미스와 클라우드 환경에서 워크로드를 유연하게 운영하기 위한 엔터프라이즈 가상화의 미래
