At Red Hat, we believe in building our products to enable our customers to meet their security and compliance requirements. When choosing a technology partner, security is a fundamental aspect which can be the differentiator. Red Hat instills confidence in our customers by having a strong commitment to security.
Red Hat works with a vast customer base, which includes businesses, government organizations, and individuals. These customers trust Red Hat with valuable information such as personal data, financial details, and proprietary business information.
Security measures are essential to safeguard the integrity of Red Hat's software products. By ensuring that the software is not tampered with or compromised during distribution or deployment, Red Hat can guarantee that customers are using authentic, reliable, and secure software.
Our customers are caught between increasing pressures to follow increasingly complex regulations and accelerating their digital transformation while facing cost reduction pressure (“do more with less”) for their cloud, infrastructure, development, security and compliance costs.
Securing OpenStack—with its many components—can be complex. Add compliance efforts and security control groups, and things get tricky. In 2017, the Red Hat team had a dream that one day we can hand a government official 70% of their security requirements in a ready-to-deploy OpenStack. Six years later, where do we stand?
Security overview of Red Hat OpenStack Platform
Red Hat OpenStack Platform is a highly secure cloud computing platform that provides a range of security features to ensure the protection of your infrastructure and data. Features include:
- Identity and Access Management (IAM): Red Hat OpenStack Platform integrates with the Keystone identity service, which provides centralized authentication and authorization mechanisms. Keystone supports various authentication methods, including username/password, token-based authentication, and integration with external authentication providers such as LDAP and Active Directory.
- Role-Based Access Control (RBAC): RBAC allows administrators to define granular access control policies based on user roles. This ensures that each user has appropriate privileges and access rights within the OpenStack environment.
- Network Isolation: Red Hat OpenStack Platform uses Neutron, the networking component, to provide network isolation and segmentation. It enables the creation of virtual networks and supports VLANs, VXLANs, and Software-Defined Networking (SDN) technologies, ensuring that tenant networks remain isolated from each other.
- Secure Hypervisor: Red Hat OpenStack Platform supports the libvirt driver (using KVM as the hypervisor on Compute nodes). This hypervisor is built with strong security measures to prevent unauthorized access, virtual machine escape attacks, and secure tenant isolation.
- Secure Images: Red Hat OpenStack Platform includes Glance, the image service, which provides a secure image repository for virtual machine templates. Images can be digitally signed and verified, ensuring that only trusted and tamper-free images are used to create instances.
- Encrypted Storage: Cinder, the block storage component of Red Hat OpenStack Platform, supports encryption of Cinder volumes. This ensures that data stored on volumes is protected and can only be accessed by authorized users.
- Secure Object Storage: Red Hat OpenStack Platform integrates with Swift, the object storage service, which supports data encryption at rest. Data stored in Swift can be encrypted using server-side encryption, ensuring the confidentiality and integrity of the stored objects.
- Observability: The Service Telemetry Framework (STF) is a feature of Red Hat OpenStack Platform that provides an automated collection data from remote clients - Red Hat OpenStack Platform or third-party nodes - and transmits that information to a centralized source, receiving Red Hat OpenShift Container Platform deployment for storage, retrieval, and monitoring . The data collected by STF can either be, Metric, which is a numeric measurement of an application or system; and Event, which are irregular and discrete occurrences that happen in a system. The collection components that are required on the clients are lightweight. The multicast message bus that is shared by all clients and the deployment provides fast and reliable data transport. Other modular components for receiving and storing data are deployed in containers on Red Hat OpenShift.
- Red Hat OpenStack Platform comes with SELinux (Security-Enhanced Linux) integration by default. SELinux offers an additional layer of security by enforcing mandatory access controls and preventing unauthorized access to system resources.
Red Hat OpenStack Platform can be integrated with third-party Intrusion Detection and Prevention System (IDPS) solutions to monitor the cloud environment for potential security threats. IDPS systems can detect and prevent unauthorized access attempts, network attacks, and other security breaches.
It's important to note that the security features in Red Hat OpenStack Platform can be further enhanced and customized based on specific deployment requirements and organizational security policies. Additionally, regular security assessments and monitoring, along with continuous security updates, are crucial to maintaining the overall security of an OpenStack deployment.
Why Red Hat OpenStack Platform
Value of Red Hat
In this context the selection of the right on-premise private-cloud platform is critical. Red Hat OpenStack Platform provides the key elements you need regarding infrastructure security with built-in service hardening and key management; data integrity with data encryption at rest and on the fly.
Red Hat supports the entire stack: Host Linux, KVM, OpenStack, and supported CEPH storage (in conjunction with IBM), and offers 10 years of RHEL lifecycle support, and up to 5 years of Red Hat OpenStack Platform lifecycle support.
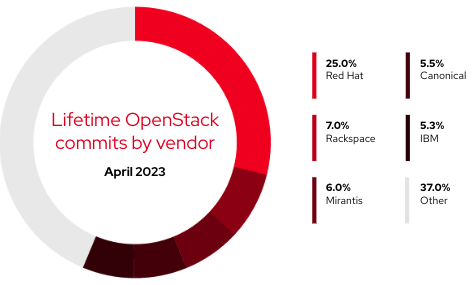
Red Hat’s upstream first philosophy means we do not build forks or one-off snowflakes at customer sites, and Red Hat is a leader in contributions to the upstream OpenStack community which enables Red Hat to support the customer through their deployment.
Red Hat certifies RHEL, Windows and SUSE Linux guest operating systems which enables us to support the customer end-end: host linux, KVM, OpenStack, guest OS.
At last, Red Hat provides a Security and Hardening Guide that provides good practice advice and conceptual information about hardening the security of a Red Hat OpenStack Platform environment.
Secure Supply Chain
Red Hat has a dedicated product security team that monitors, identifies, and addresses risks quickly. With Red Hat, you receive security patches (that Red Hat has created, tested, and delivered) for all versions of Red Hat’s entire portfolio in their supported life cycles (including backported fixes). Red Hat also invests in the engineering required to certify products to meet stringent government and commercial security standards (such as FIPS 140-3).
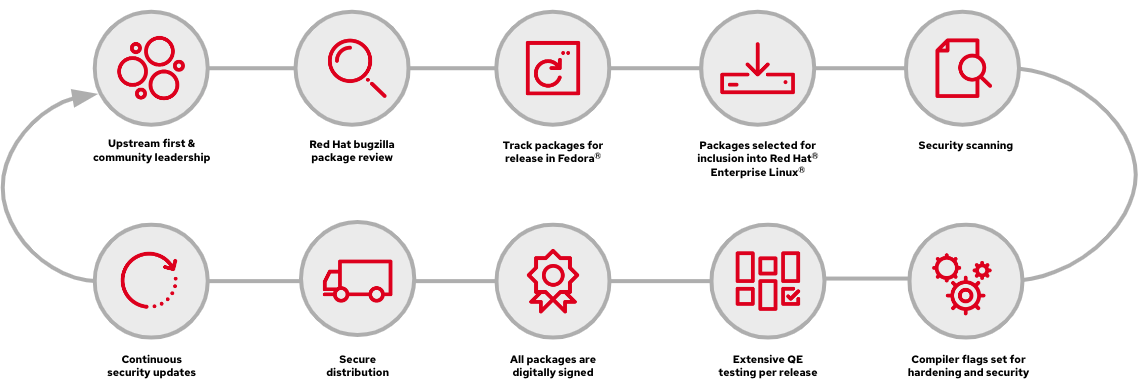
As part of the Secure Software Supply Chain (SSSC), Red Hat is responsible for maintaining upstream relationships and community involvement to help focus on security from the start by:
- Selecting and configuring packages based on their security and performance track records.
- Building binaries from associated source code (instead of simply accepting upstream builds compiler options at build matter).
- Applying a suite of inspection and quality assurance tools to prevent an array of potential security issues and regressions.
- Digitally signing all released packages and distributing them through cryptographically authenticated distribution channels.
- Providing a single, unified mechanism for distributing patches and updates.
You can get more information about SSSC here.
OpenStack Key Security Capabilities
At the heart of Openstack security there are two key components in charge of secret management (Barbican), and identity management (Keystone).
Barbican is the OpenStack Key Manager service that provides secure storage, provisioning, and management of secret data. Some of the services that depend on Barbican include Nova (Compute), Glance (Image), Cinder (Block Storage), and many others.
Keystone is the OpenStack Identity service that provides API client authentication, service discovery, and distributed multi-tenant authorization. It is a core component of OpenStack and is used by almost all other OpenStack services for authentication and authorization. Some of the services that depend on Keystone include Nova (Compute), Glance (Image), Neutron (Networking), Cinder (Block Storage), Swift (Object Storage), and many others.
BARBICAN
OpenStack Barbican is a project within the OpenStack ecosystem that focuses on providing secure key management services. It offers several security features to ensure the protection and confidentiality of sensitive information. Encryption and key manaWhy Red Hat OpenStack Platform
Value of Red Hatgement features can largely be split into two main groups; Service encryption management and Secrets management for infrastructure and tenant services such as Cinder Volume Encryption, Cinder Backup Encryption, Swift Object Encryption, Octavia Integration with Barbican.
Key security features provided by OpenStack Barbican:
- Key Storage and Management provides a secure, centralized key management system, allowing users to store, retrieve, and manage cryptographic keys securely within the OpenStack environment. Keys are stored in a dedicated key storage repository which can be backed by a secure database or an external key management system.
- Key Lifecycle Management supports key lifecycle management, including key generation, rotation, and revocation. This feature ensures that keys are properly managed throughout their lifespan and that outdated or compromised keys can be easily revoked or rotated.
- Access Control offers fine-grained access control mechanisms to restrict key access and operations. It supports role-based access control (RBAC), allowing administrators to define access policies based on user roles and permissions. This ensures that only authorized users or services can access and manage keys.
- Secure Key Storage employs various security measures to protect keys at rest. Keys are encrypted before storage, and access to the key storage repository is tightly controlled. Encryption helps prevent unauthorized access to the keys, even if the underlying storage is compromised.
- Auditing and Logging provides logging and auditing capabilities to track key management operations. This helps monitoring and detecting any unauthorized access attempts or suspicious activities related to key operations. Audit logs can be used for compliance purposes and forensic analysis.
- Secure Communication ensures communication is protected between the client applications and the key management service through the use of secure protocols such as Transport Layer Security (TLS). This helps protect sensitive data during transit and prevents eavesdropping or tampering.
- Keystone is the OpenStack identity service used to leverage its authentication and authorization mechanisms. This integration ensures that only authenticated and authorized users or services can access Barbican's key management services.
These security features collectively enhance the security of key management operations in OpenStack environments and help protect sensitive information by implementing robust security controls and best practices.
Hardware Security Modules integration with Barbican
Barbican supports hardware-based key protection mechanisms, such as integration with Hardware Security Modules (HSMs). This enables the secure storage and management of keys within dedicated hardware devices that provide tamper-resistant environments and perform cryptographic operations. It provides a high level of protection for sensitive information, such as encryption keys, digital certificates, and other cryptographic assets.
When integrating an HSM with OpenStack, it enables OpenStack to leverage the HSM’s capabilities for key management and cryptographic operations. Here are a few key aspects of OpenStack HSM integration:
- Key Management integration allows OpenStack to offload the management of cryptographic keys to the HSM device. The HSM securely generates, stores, and protects keys, ensuring they are safeguarded against unauthorized access.
- Cryptographic Operations enables OpenStack to utilize the HSM for performing cryptographic operations such as encryption, decryption, signing, and verification. The HSM's hardware-based cryptographic functions offer high-performance and increased security for these operations.
- Secure Key Storage to provide tamper-resistant environments for key storage, protecting them from physical and logical attacks. By integrating HSMs with OpenStack, the keys used within the cloud infrastructure can be stored securely within the HSM, reducing the risk of key compromise.
- Compliance and Auditing assist with meeting regulatory compliance requirements by providing a trusted platform for cryptographic operations. The HSM can facilitate compliance with standards such as PCI DSS (Payment Card Industry Data Security Standard) or FIPS (Federal Information Processing Standards) by ensuring proper key management and protection.
KEYSTONE
OpenStack Keystone, the identity service within the OpenStack ecosystem, incorporates several security features to ensure secure authentication, authorization, and access control. Key features provided by OpenStack Keystone include:
- Authentication to supports various methods, including username/password, token-based authentication, and external identity providers (such as LDAP or Active Directory).
- Role-Based Access Control manages user permissions and access to resources within the OpenStack environment. RBAC allows administrators to define fine-grained access policies based on user roles, projects, and domains, ensuring that only authorized users have appropriate access privileges.
- Token-based Authorization issues tokens upon successful authentication and contain information about the user's identity and permissions. Keystone validates these tokens to authorize access to OpenStack services and resources.
- Federation enables integration with external identity providers. This feature allows users to authenticate against external systems and access OpenStack resources using their existing credentials. Federation simplifies user management and extends authentication options while maintaining security.
- Endpoint Protection provides secure endpoint protection by employing Transport Layer Security (TLS) encryption for communication between clients and the Keystone service. This ensures the confidentiality and integrity of sensitive information transmitted over the network.
- Auditing and Logging: Keystone offers auditing and logging capabilities to track user authentication, authorization, and policy enforcement activities. Audit logs provide visibility into security-related events, aiding in monitoring and detecting potential security threats or unauthorized access attempts.
- Secure Storage of user credentials and passwords by utilizing appropriate encryption mechanisms. This helps protect sensitive information from unauthorized access, even if the underlying storage is compromised.
- Multi-Factor Authentication supports multi-factor authentication to allow users to enhance the security of their accounts by requiring additional authentication factors, such as one-time passwords (OTP) or biometric verification.
By implementing these security features, OpenStack Keystone ensures the secure management of user identities, authentication, and access control within the OpenStack environment. It helps protect resources, maintain data confidentiality, and mitigate potential security risks.
Transport Layer Security Everywhere
One critical security piece is Transport Layer Security Everywhere (TLS-e). It is a security initiative within OpenStack to encrypt network traffic between OpenStack services by default and a key requirement to meet several governing security entities.
In Red Hat OpenStack Platform it enables SSL/TLS on overcloud endpoints. It is designed to provide secure communication between all components of an OpenStack deployment, including internal traffic between services and external traffic from users to the OpenStack APIs.
This feature was implemented for external communications as part of Red Hat OpenStack Platform 12 and for all traffic it was enabled on Red Hat OpenStack Platform 13. What makes it unique on Red Hat OpenStack Platform is the ease of deployment for the functionality with Director. Due to the number of certificates required to configure TLS everywhere, director integrates with a Red Hat Identity Management (IdM) server to act as a certificate authority and manage the overcloud certificates for secure communication.
Strong SSL Certificates
As of Red Hat OpenStack Platform 16.1 we supported the creation of SSL certificates using private keys stronger than 2048 bits. Users can improve security by increasing the size of private keys used to create certificates for encrypted service traffic. The default Red Hat OpenStack Platform private key size of 2048 bits matches the National Institute of Standards and Technology (NIST) recommended minimum.
Sobre o autor
Mais como este
Navigating the Mythos-haunted world of platform security
MCP security: Logging and runtime security measures
Collaboration In Product Security | Compiler
Keeping Track Of Vulnerabilities With CVEs | Compiler
Navegue por canal
Automação
Últimas novidades em automação de TI para empresas de tecnologia, equipes e ambientes
Inteligência artificial
Descubra as atualizações nas plataformas que proporcionam aos clientes executar suas cargas de trabalho de IA em qualquer ambiente
Nuvem híbrida aberta
Veja como construímos um futuro mais flexível com a nuvem híbrida
Segurança
Veja as últimas novidades sobre como reduzimos riscos em ambientes e tecnologias
Edge computing
Saiba quais são as atualizações nas plataformas que simplificam as operações na borda
Infraestrutura
Saiba o que há de mais recente na plataforma Linux empresarial líder mundial
Aplicações
Conheça nossas soluções desenvolvidas para ajudar você a superar os desafios mais complexos de aplicações
Virtualização
O futuro da virtualização empresarial para suas cargas de trabalho on-premise ou na nuvem