The beta of Red Hat Insights malware detection service is now available. The malware detection service is a monitoring and assessment tool that scans Red Hat Enterprise Linux (RHEL) systems for the presence of malware, utilizing over 175 signatures of known Linux malware provided in partnership with the IBM X-Force Threat Intelligence team. The Red Hat Insights analysis provides:
-
The list of signatures scanned against your RHEL systems, with links to reference information and analysis reports
-
Results for individual system scans and aggregated results for all of your RHEL systems
To scan your Red Hat Insights systems for potential malware, follow our getting started guide. After your first full scan, you can view the results in the beta version of Insights malware detection.
Please note: Due to the potentially sensitive nature of this information, only Organizational Admins have default access to the results. All other users must first be given access to the service, as detailed in section 2.2. of the Insights malware detection guide.
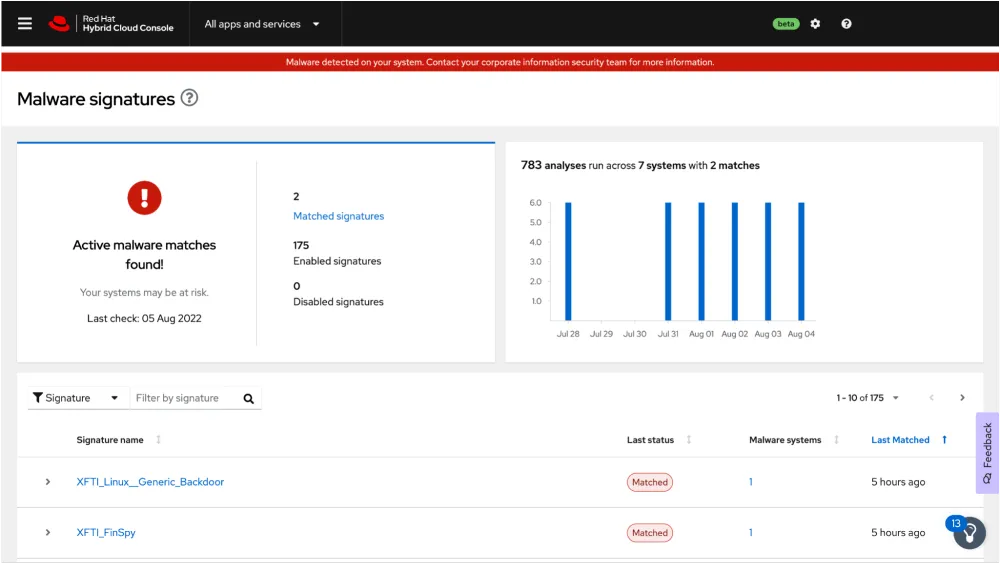
We hope you don’t see a screen like the one below, but if signature matches are found on your systems, you will see details about the signatures, the number of systems that were matched and details about where on the system the matches were found.
 Like the other Insights services, malware detection is included in your RHEL subscription. Malware detection supports RHEL 7 Server / Workstation and RHEL 8 and 9 hosts.
Like the other Insights services, malware detection is included in your RHEL subscription. Malware detection supports RHEL 7 Server / Workstation and RHEL 8 and 9 hosts.
Any feedback about the new malware detection service can be sent to us using the Feedback button inside of Insights — you can see it in the above screenshot on the lower right hand side of the page. Please give the Insights malware detection service a try soon!
저자 소개
Shane McDowell is a Principal Product Manager for Red Hat. He is focused on helping customers manage their infrastructure in the hybrid cloud. He brings 20+ years of experience with delivering and supporting technology solutions to users in a variety of industries, including Information Technology, Talent Acquisition and Residential Management.
유사한 검색 결과
Ansible Automation Platform 2.6 업그레이드 경로 계획
사이버 보안에서 AI의 4가지 활용 사례
Operating System Management | Compiler
Collaboration In Product Security | Compiler
채널별 검색
오토메이션
기술, 팀, 인프라를 위한 IT 자동화 최신 동향
인공지능
고객이 어디서나 AI 워크로드를 실행할 수 있도록 지원하는 플랫폼 업데이트
오픈 하이브리드 클라우드
하이브리드 클라우드로 더욱 유연한 미래를 구축하는 방법을 알아보세요
보안
환경과 기술 전반에 걸쳐 리스크를 감소하는 방법에 대한 최신 정보
엣지 컴퓨팅
엣지에서의 운영을 단순화하는 플랫폼 업데이트
인프라
세계적으로 인정받은 기업용 Linux 플랫폼에 대한 최신 정보
애플리케이션
복잡한 애플리케이션에 대한 솔루션 더 보기
가상화
온프레미스와 클라우드 환경에서 워크로드를 유연하게 운영하기 위한 엔터프라이즈 가상화의 미래
