In this post:
-
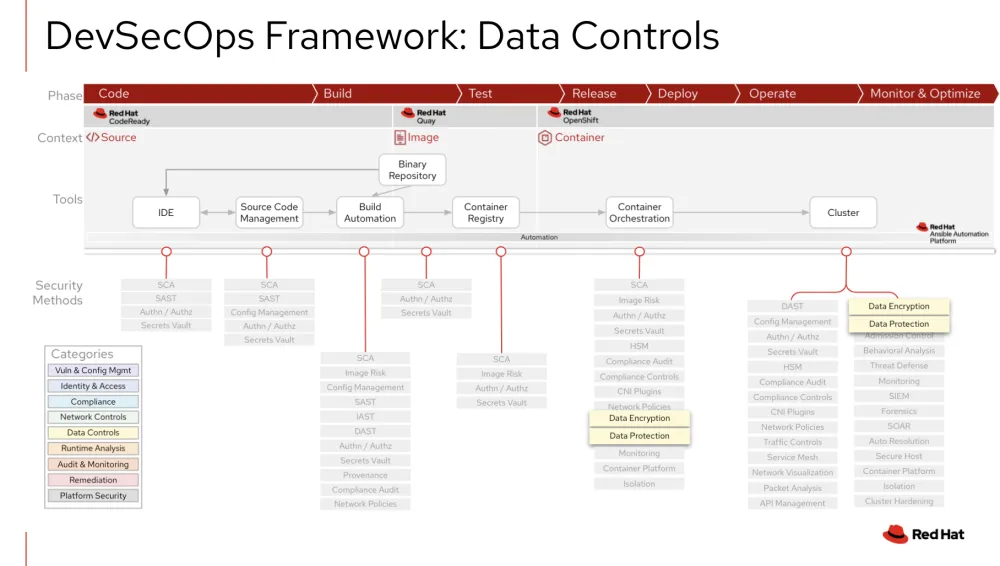
Explains the concept of data controls.
-
Shows how data controls integrate into the framework at the container orchestration and cluster level.
-
Pointers to Red Hat partners that can help with data controls.
Data controls help protect data integrity and prevent unauthorized data disclosure for stored data and data in motion. In this post we'll dive deeper into the concepts of data controls and how they fit into the DevSecOps framework.
July is “Data Controls” month in Red Hat’s monthly Security series! Since March 2021, the Red Hat Security Ecosystem team has published monthly articles and videos on DevOps Security topics to help you learn how Red Hat can help you master the practice called DevSecOps.
By explaining how to assemble Red Hat products and introducing our security ecosystem partners, we aim to aid in your journey to deploying a comprehensive DevSecOps solution.
Data controls defined
Data controls are typically implemented in a running Kubernetes cluster, and the goal is to provide a defense in depth approach to protect sensitive data either at rest or in motion. The following security methods make up the Data Controls category:
-
Data encryption: Provides data cryptography, tokenization, data masking, and key management capabilities to help prevent unauthorized disclosure of data in databases, files, and containers.
-
Data protection: Discovers and classifies data and monitors and audits activity to help protect sensitive data and improve compliance.
Data controls integrated in DevSecOps
As pictured in the DevSecOps framework below, data controls integrations are typically found on the right side of the DevSecOps life cycle in a running cluster. The table that follows details some, but not all, of the common integrations to consider for Data Controls.
|
Integration Point |
Description |
|
Container Orchestration and Cluster |
Data Control integrations in both container orchestration and the running cluster provide the same functionality as described below. Whether you are testing, releasing, deploying, operating or monitoring the cluster, these controls need to be considered. With Red Hat OpenShift Container Platform, you can enable etcd encryption, which provides an additional layer of data security for Secrets, Config maps, Routes, and OAuth tokens. This can help protect data if it's exposed to the wrong parties. Data in-transit encryption is all about certificates and securing the ingress and egress traffic within a cluster. One of the many certificate types to address in the default API server certificate provided by the OpenShift Container Platform. For example, if you need clients outside of the cluster to access any running web applications, you’ll need to replace the certificate with a Certificate Authority that the client's trust. In order to centrally manage, store and further protect OpenShift keys and certificates for data controls, you’ll want to extend and enhance OpenShift Container Platform’s data security capabilities with certified partner software that centralizes data encryption across environments and adds layers of data protection. Red Hat’s partner ecosystem can help add:
Data protection in a running cluster can also include discovering where sensitive data exists in your cluster, as well as analyzing data risks and uncovering suspicious activity against the data in rest. |
Enhance and extend Data Controls with Red Hat partners
Combining Red Hat OpenShift Container Platform Data Control features with Red Hat’s certified ecosystem security partners can help your organization's DevSecOps practice.
If you are looking to enhance and extend Red Hat’s security capabilities in Data Controls, take a look at the following Red Hat Partners:
-
Zettaset’s certified software, product brief and webinar.
-
Thales’ Red Hat solution brief and webinar.
À propos de l'auteur
Dave Meurer currently serves as a Principal Solution Architect on the Red Hat Global Partner Security ISV team, where he owns technical relationships and evangelism with security independent software vendor partners of Red Hat. Before joining Red Hat, he spent nine years in the Application Security industry with Synopsys and Black Duck, where he served in similar roles as the director of technical alliances and sales engineering.
Meurer also worked for Skyway Software, HSN.com, and Accenture in various management and application development roles. When he’s not thinking about Kubernetes, security, and partners, he enjoys being the VP Sales of North Central Tampa for his wife (the CEO) and 5 kids (Inside Sales).
Plus de résultats similaires
When AI finds the bugs: Why defense in depth was always the answer
CVE-2026-31431: How Red Hat Advanced Cluster Security and Red Hat Advanced Cluster Management can help
Collaboration In Product Security | Compiler
Keeping Track Of Vulnerabilities With CVEs | Compiler
Parcourir par canal
Automatisation
Les dernières nouveautés en matière d'automatisation informatique pour les technologies, les équipes et les environnements
Intelligence artificielle
Actualité sur les plateformes qui permettent aux clients d'exécuter des charges de travail d'IA sur tout type d'environnement
Cloud hybride ouvert
Découvrez comment créer un avenir flexible grâce au cloud hybride
Sécurité
Les dernières actualités sur la façon dont nous réduisons les risques dans tous les environnements et technologies
Edge computing
Actualité sur les plateformes qui simplifient les opérations en périphérie
Infrastructure
Les dernières nouveautés sur la plateforme Linux d'entreprise leader au monde
Applications
À l’intérieur de nos solutions aux défis d’application les plus difficiles
Virtualisation
L'avenir de la virtualisation d'entreprise pour vos charges de travail sur site ou sur le cloud
