A new series of vulnerabilities in Intel processors, known as Microarchitectural Data Sampling, or more simply MDS, was recently made public and Red Hat released information about how the vulnerabilities affect our software and how to protect your organization.
In the simplest terms, MDS is a vulnerability in Intel processors similar to Spectre and Meltdown; it allows a guest to read protected memory from anywhere on the host or guest. To mitigate the risks exposed by MDS, a combination of updated microcode, updated kernel(s), patches, and administrator action will need to be taken for both the hypervisors and virtual machines in your Red Hat Virtualization deployment. Unlike some similar vulnerabilities, simply disabling SMT and/or hyper-threading is not enough to protect your applications.
Protecting your applications
The Red Hat Virtualization team released updates for both 4.2 and 4.3, implementing code-based mitigations. For addressing MDS vulnerabilities when using versions 4.1 or earlier, disabling multithreading (SMT) using the server BIOS is the recommended method.
If you are using Red Hat Virtualization 4.2, please be aware it is considered part of the extended update services (EUS) channel since Red Hat Virtualization 4.3 became generally available (GA) on May 10, 2019. This means you will need to update the repositories to enable the EUS channel on the hosts before the newest updates are visible.
In addition to updating Red Hat Virtualization Manager to the latest version, there are several additional steps which may be taken for hosts and guests:
For hypervisor hosts:
Updated microcode and BIOS should be utilized. Red Hat Virtualization and RHEL include updates from Intel for microcode; you should also work with your hardware vendor to determine if you’re running the recommended microcode and BIOS.
Update the kernel to the latest available for your version of RHEL.
Apply the most recent Red Hat Virtualization Host and/or RHEL updates.
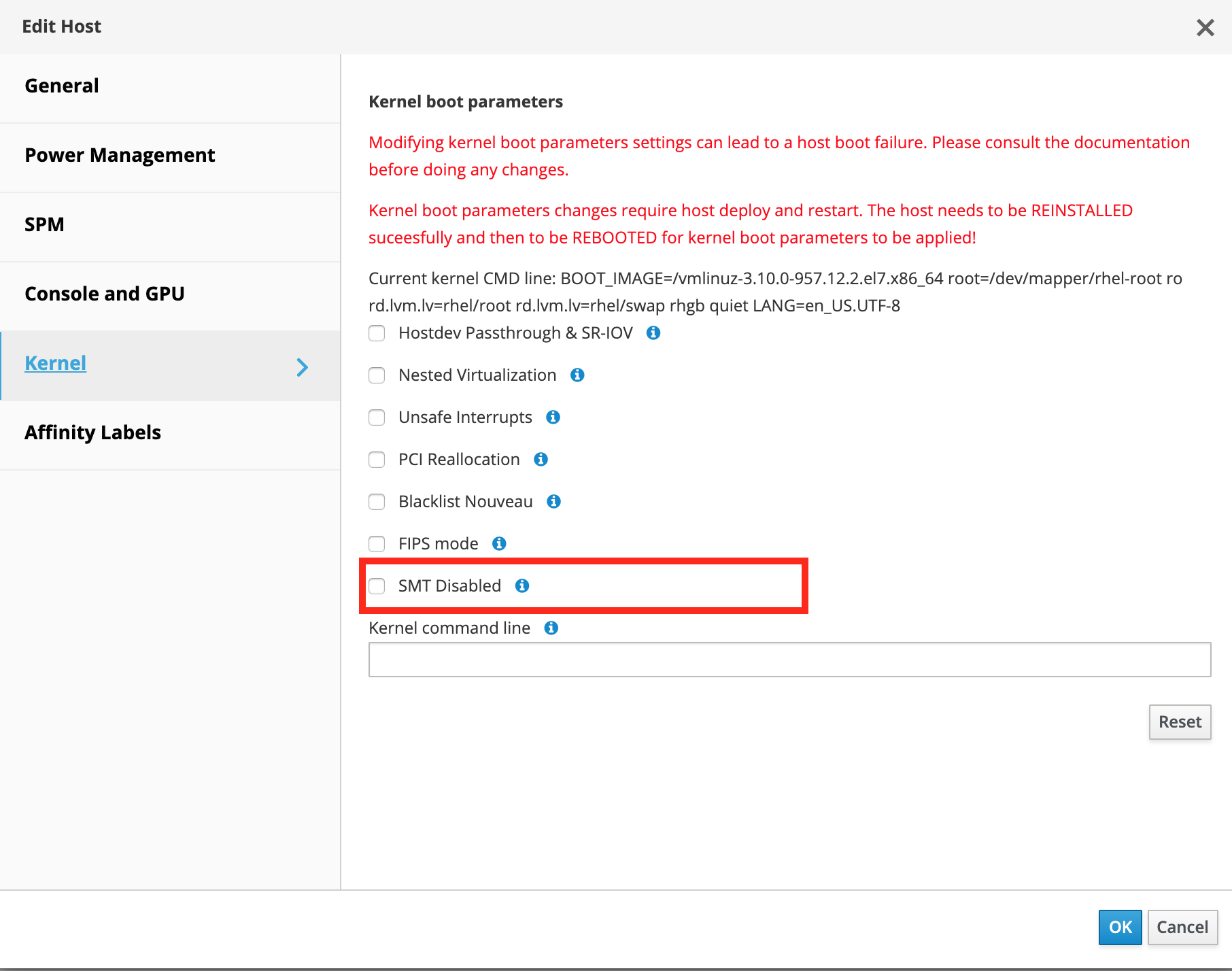
Disable multithreading using kernel boot parameters from the Red Hat Virtualization Manager interface.
For virtual machines:
Use the “MDS” CPU type. After updating your Red Hat Virtualization deployment, apply the MDS mitigations, and update the cluster CPU type to “Intel XXX IBRS SSBD MDS Family” CPU type for your cluster. This will apply mitigations for Spectre, Meltdown, and MDS.
Update the kernel and other packages to the latest available and follow the recommendations from Red Hat and/or Microsoft for your guest operating system.
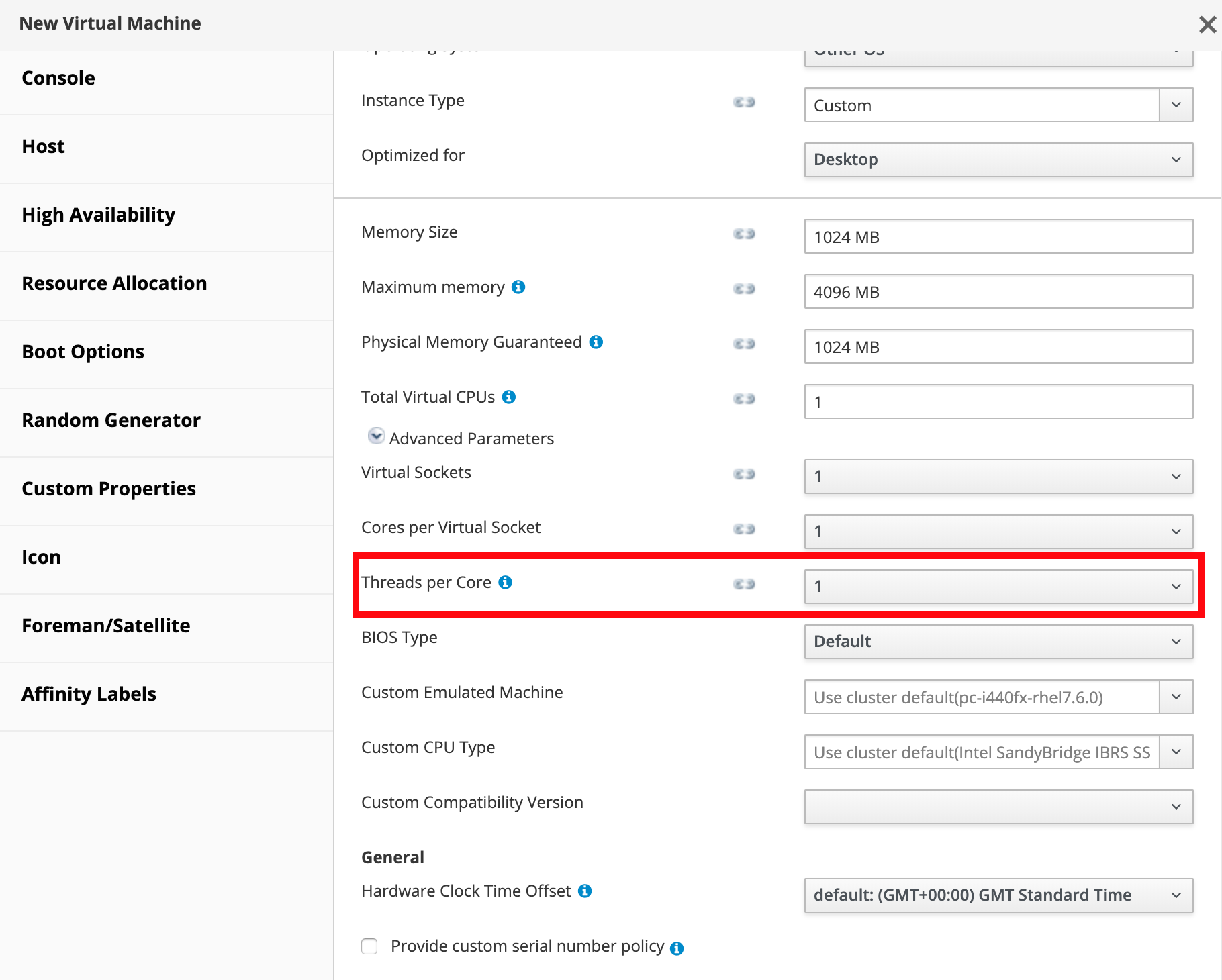
Disable guest hyperthreading. This can be done by setting the number of threads per core to one for the virtual machines. This is the default value.
The standard update and upgrade procedures should be used when applying the MDS mitigation updates. If you’re using the self-hosted Red Hat Virtualization manager, be sure to run engine-setup again afterward so that the cluster CPU options are updated.
Knowledge is power
MDS is only one of the latest major vulnerabilities which broadly affects many IT systems. Be sure to read Red Hat’s Vulnerability Response article documenting the issues. Also a very helpful explanation from Jon Masters about what MDS is, and how it is exploited to get data from hosts with a technical deep dive in this 17 minute video that provides a detailed look into MDS and similar vulnerabilities.
Sull'autore
Altri risultati simili a questo
Confidential clusters for Red Hat OpenShift: Developer Preview now available on Microsoft Azure with AMD SEV-SNP
Redefining security data: Red Hat’s new VEX experience heading to Red Hat Summit 2026
Collaboration In Product Security | Compiler
Keeping Track Of Vulnerabilities With CVEs | Compiler
Ricerca per canale
Automazione
Novità sull'automazione IT di tecnologie, team e ambienti
Intelligenza artificiale
Aggiornamenti sulle piattaforme che consentono alle aziende di eseguire carichi di lavoro IA ovunque
Hybrid cloud open source
Scopri come affrontare il futuro in modo più agile grazie al cloud ibrido
Sicurezza
Le ultime novità sulle nostre soluzioni per ridurre i rischi nelle tecnologie e negli ambienti
Edge computing
Aggiornamenti sulle piattaforme che semplificano l'operatività edge
Infrastruttura
Le ultime novità sulla piattaforma Linux aziendale leader a livello mondiale
Applicazioni
Approfondimenti sulle nostre soluzioni alle sfide applicative più difficili
Virtualizzazione
Il futuro della virtualizzazione negli ambienti aziendali per i carichi di lavoro on premise o nel cloud
