Automation can help increase efficiency, save time and improve consistency, which is why Red Hat Enterprise Linux (RHEL) includes features that help automate many tasks. RHEL system roles are a collection of Ansible content that helps provide more consistent workflows and streamline the execution of many manual tasks.
Fapolicyd is a security-focused feature that can control which applications may be executed in a RHEL environment, as well as verify the integrity of applications prior to execution. This functionality helps prevent untrusted applications from being executed on a RHEL system. For more information on fapolicyd, refer to the Blocking and allowing applications by using fapolicyd documentation.
The recently introduced fapolicyd system role can help automate the process of installing and configuring fapolicyd, as well as manage the list of files that fapolicyd trusts.
Environment overview
In my lab environment, I have a control node system named rhel9-controlnode.example.com and two managed nodes: rhel9-server1.example.com and rhel9-server2.example.com.
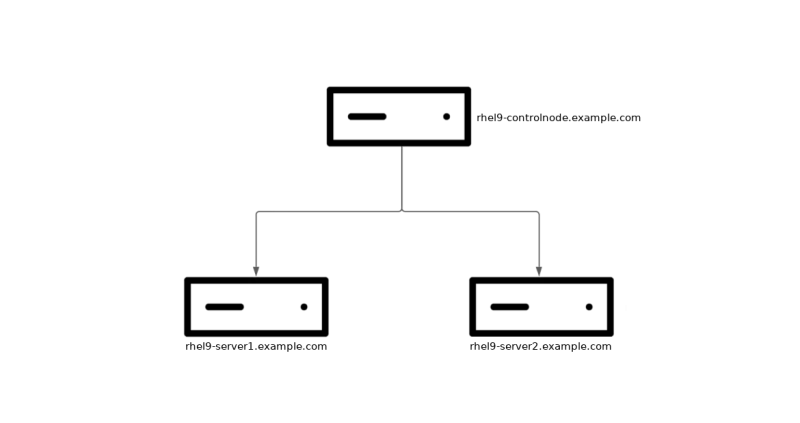
The rhel9-controlenode.example.com system, as my control node, has the ansible-core and rhel-system-roles packages installed, and has SSH key authentication setup with the rhel9-server1.example.com and rhel9-server2.example.com managed nodes. For more information on getting started with RHEL system roles, refer to the Introduction to RHEL system roles article.
I’d like to use the fapolicyd system role to install and start fapolicyd on the two managed nodes. In addition, I’d like to have fapolicyd configured with the sha256 integrity option, which will perform an integrity check prior to allowing applications to execute.
Create the inventory file
I’ll create an inventory file named inventory.yml on the rhel9-controlnode.example.com host. This file lists the two managed nodes, and sets the fapolicyd_setup_integrity variable to sha256 to instruct the fapolicyd role to configure the SHA-256 integrity option.
all:
hosts:
rhel9-server1.example.com:
rhel9-server2.example.com:
vars:
fapolicyd_setup_integrity: sha256
If you're using Ansible automation controller as your control node, this Inventory can be imported into Red Hat Ansible Automation Platform using an SCM project or using the awx-manage Utility, as specified in the documentation.
Create the playbook
Next, I’ll create a simple Ansible Playbook on the rhel9-controlnode.example.com host, named fapolicyd.yml, to call the fapolicyd system role:
- name: Run the fapolicyd system role
hosts: all
roles:
- redhat.rhel_system_roles.fapolicyd
If you're using Ansible automation controller as your control node, you can import this Ansible playbook into Red Hat Ansible Automation Platform. It's common to use Git repos to store Ansible Playbooks. Ansible Automation Platform stores automation in units called job templates, which contain the playbook, credentials and inventory.
Run the playbook
At this point, everything is in place. I’ll use the ansible-playbook command to run the fapolicyd.yml playbook from the rhel9-controlnode.example.com host (which already has rhel-system-roles and ansible-core packages installed). The -b flag prompts Ansible to escalate privileges, and the -i option provides inventory.yml as the Ansible inventory.
$ ansible-playbook -i inventory.yml -b fapolicyd.yml
If you're using Ansible automation controller as your control node, you can launch the job from the automation controller web interface.
I validated that the playbook completed successfully:

Validating the configuration
Next, I’ll validate that fapolicyd is working. I’ll login to each of the managed nodes, both of which have a Python script located at /usr/local/bin/python_script.py. When I attempt to run this script, fapolicyd prevents it from being executed, as it has not been marked as a trusted file:
[brian@rhel9-server1 ~]$ /usr/local/bin/python_script.py -bash: /usr/local/bin/python_script.py: Operation not permitted
If I would like fapolicyd to allow this script to be run, I can update the inventory.yml on the control node, and specify that this a trusted file by listing it under the fapolciyd_add_trusted_file variable:
all:
hosts:
rhel9-server1.example.com:
rhel9-server2.example.com:
vars:
fapolicyd_setup_integrity: sha256
fapolicyd_add_trusted_file:
- /usr/local/bin/python_script.py After running the fapolicyd.yml playbook again with the updated inventory.yml, I’ll again try to execute the script from one of the managed nodes, and fapolicyd now allows the script to be executed:
[brian@rhel9-server1 ~]$ /usr/local/bin/python_script.py Hello world
However, if the script is modified, the fapolicyd SHA-256 integrity checking will cause fapolicyd to detect that the file was modified and prevent it from being executed.
[brian@rhel9-server1 ~]$ sudo sed -i 's/Hello world/Hello World!/'
/usr/local/bin/python_script.py
[brian@rhel9-server1 ~]$ /usr/local/bin/python_script.py
-bash: /usr/local/bin/python_script.py: Operation not permitted
In this example, I modified the script to output slightly different text. When attempting to run the script, fapolicyd detects that the SHA-256 checksum of the file doesn’t match the file that was previously trusted, which results in fapolicyd preventing the Python script from being run. If I’d like to allow this updated script to run, I could run the system role again, which would add the updated scripts SHA-256 checksum to the list of trusted files, allowing the updated script to be executed.
Wrap up
The fapolicyd system role helps you automate the configuration of fapolicyd across your RHEL environment, more consistently and at scale. To explore additional system roles, review the list of available RHEL system roles and start managing your RHEL servers in a more efficient, consistent and automated manner today.
Want to learn more about the Red Hat Ansible Automation Platform? Check out our e-book the automation architect's handbook.
Sull'autore
Brian Smith is a product manager at Red Hat focused on RHEL automation and management. He has been at Red Hat since 2018, previously working with public sector customers as a technical account manager (TAM).
Altri risultati simili a questo
Data-driven automation with Red Hat Ansible Automation Platform
More than meets the eye: Behind the scenes of Red Hat Enterprise Linux 10 (Part 4)
Technically Speaking | Taming AI agents with observability
Transforming Your Identity Management | Code Comments
Ricerca per canale
Automazione
Novità sull'automazione IT di tecnologie, team e ambienti
Intelligenza artificiale
Aggiornamenti sulle piattaforme che consentono alle aziende di eseguire carichi di lavoro IA ovunque
Hybrid cloud open source
Scopri come affrontare il futuro in modo più agile grazie al cloud ibrido
Sicurezza
Le ultime novità sulle nostre soluzioni per ridurre i rischi nelle tecnologie e negli ambienti
Edge computing
Aggiornamenti sulle piattaforme che semplificano l'operatività edge
Infrastruttura
Le ultime novità sulla piattaforma Linux aziendale leader a livello mondiale
Applicazioni
Approfondimenti sulle nostre soluzioni alle sfide applicative più difficili
Virtualizzazione
Il futuro della virtualizzazione negli ambienti aziendali per i carichi di lavoro on premise o nel cloud
