In this post:
Get an overview of how the Portfolio Architecture team delivers the most relevant and powerful architectures for customers and contributes back to the community.
Get a breakdown of how an example portfolio architecture helped one customer address three main infrastructure initiatives.
See what the subscription requirements are for you to replicate the architecture in your environment.
In our last article, we discussed a theoretical framework for inspiring and designing a self-healing infrastructure, using Red Hat Insights alongside Ansible Automation Platform. Today’s article will dive a little deeper into what we’ve designed as an easily consumable and efficiently replicable Red Hat Portfolio Architecture. Using an example of how one of our customers is architecting similar solutions to bring this proposed architecture to life, we hope to help you hit the ground running with this concept, so you can take full advantage of the entire Red Hat Portfolio.
What is a Portfolio Architecture?
Before digging in, let’s briefly chat about what a Red Hat Portfolio Architecture is, and why we’re here. To start, the Portfolio Architecture team is focused on researching and replicating full portfolio solutions, built around our customers’ real-life deployments to help contribute these ideas back to the community.
As we begin with theoretical or conceptual examples similar to our previous blog post, we find these actual implementations in the field so we can showcase just how our customers are using them to achieve direct and relevant business goals. As our portfolio stack continues to grow, we continue to build upon these solutions to deliver the most relevant and powerful architectures we can.
Self-healing architecture
Now, about that real-world example I promised you. We find that one of the biggest driving forces for customers in IT automation and management is reducing the manual overhead and personnel costs that come with scaling an environment in any direction, as well as across multiple focuses like security and compliance, update and life-cycle management.
Customer experience
We recently helped a customer that was trying to reduce the manual effort and human error that occurs across more than 15 siloed teams, all without adequate methods of keeping their environments up to date. Intermittent setbacks and workflow interruptions made prioritizing security maintenance challenging, which lead to major risks within their organization and, furthermore, the customers they are servicing.
We see this all too often—we hire multiple people, or even multiple teams to handle the workloads across different management areas. On our first attempt, we get the headcount spot on, and everyone has just enough work to get done every day and business moves on at a perfect pace, right?
Well, even in a perfect scenario like that, what happens when we need to scale our environment to meet peak season demand, or when the industry changes and we need to quickly pivot and quickly need to hire more people to handle these increased workloads across each of these teams? How do we avoid hiring for peaks of traffic and being overstaffed when there's a lull. These days, elasticity is one of the most important characteristics of a solution such as this.
So, to get this into its simplest form, we’ve decided to hone in on three main business objectives:
Implement a future-ready IT infrastructure
Provide a programmable on-demand infrastructure
Deliver an automated IT infrastructure
Let’s look into each of these in a bit more detail.
Implement future-ready IT infrastructure
Preparing an infrastructure for the future security, content, and update management beyond just the initial deployment is a hefty task. We help achieve this in two main technical objectives: system consistency across hybrid cloud estates (where we focus on automating system drift that naturally occurs as they live across a hybrid cloud infrastructure) and full life-cycle, content and compliance management (which delivers combined functionality to provide exhaustive management of Red Hat products across your entire hybrid cloud estate).
Provide a programmable on-demand infrastructure
Programmatically delivering safe, secure software management solutions requires the customizability of setting routines when and how they best fit an ecosystem. To deliver this, we have overlapped focus on the life-cycle, content and compliance management objective mentioned above, and built upon it with automated detection and remediation to allow users to remotely access an automated environment that’s set to detect and subsequently remediate any found, known issues.
Deliver an automated IT infrastructure
Our final business objective is to reduce the costs associated with performing often repetitive and redundant tasks, and work to achieve consistency across workstreams. All three of our previously mentioned technical objectives — system consistency, full management, and automated detection and remediation — revolve around this last objective to help deliver a multi-dimensional solution that can be used in just about any industry.
Architectural diagrams
We have a number of customers who have successfully implemented the following solution while leveraging their current workforce to achieve more than ever before. Below is a simplified diagram to explain the environmental makeup.
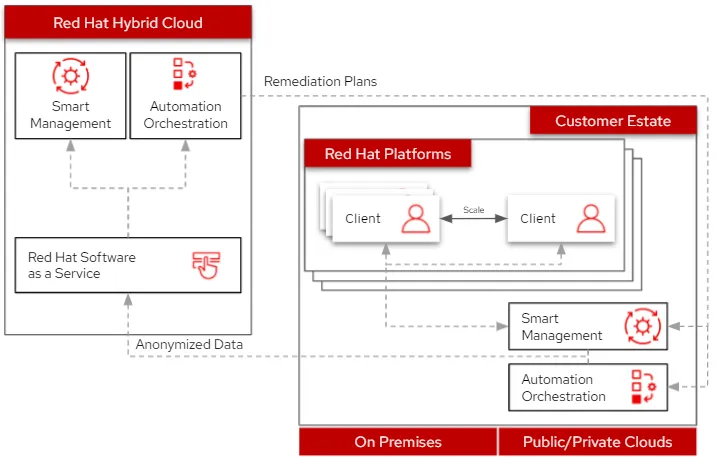
Similar to the theoretical architecture discussed in our first article, here we can see a simplified landscape to accomodate a scaling RHEL footprint while maintaining an elastic, yet stable architecture. As this ecosystem scales in either direction, the content, life-cycle, and security management will be handled by Red Hat Satellite. Additionally, Red Hat Insights has been expanded to include Red Hat Ansible Automation Platform, and can now help analyze and remediate your Ansible environment directly. In the next diagram we’ll dig a little deeper into the data flow together.
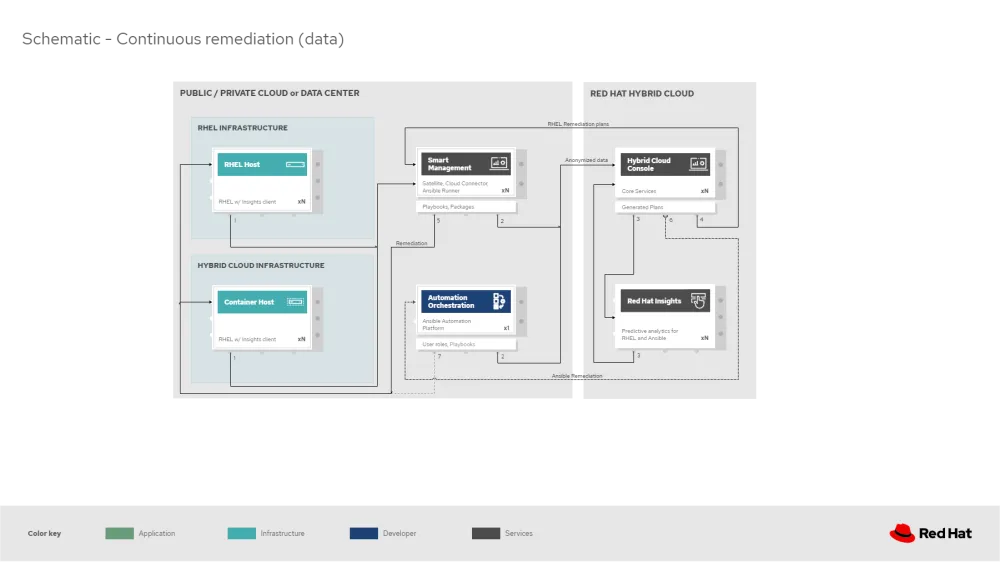
At the first stage, RHEL clients register to Red Hat Satellite, which initially collects the system data for Red Hat Insights. Here, Satellite and Ansible Automation Platform help secure connections to Red Hat Hybrid Cloud, anonymize the data, and deliver this anonymized data to Red Hat.
Once RHEL data is received, it is analyzed by Red Hat Insights for RHEL against known issues as well as customer defined baselines/parameters. Remediation plans are then generated and available, playbooks are configured and prepared for return to Red Hat Smart Management. Furthermore, within Insights for Ansible, data is received from the Ansible Automation Platform, similarly analyzed, and remediation plans are created.
Editor’s note - As of April 1, 2023, Red Hat Smart Management is now called Red Hat Satellite. Product pricing, content and services have not changed. For more information, visit the Red Hat Satellite product page or contact satellite@redhat.com.
Let’s hone in on the return and execution of the RHEL remediation plans. These can be downloaded to the Satellite from Red Hat hosted Insights, on-demand — and once available, the remediations are delivered to the client systems. Satellite’s built-in Ansible services automate running the remediation playbooks on multiple systems in a single run, and anything requiring manual configuration would be outlined in the remediation plan in the Satellite. Any subsequent package updates will also be pulled from the Satellite. Finally, the remediation status is outlined in the Satellite dashboard.
Next, Ansible syncs with Red Hat to download its remediations, and delivers them to Ansible Automation Platform. As an optional note, if desired RHEL remediation plans can also be manually synced to the automation controller, which can be used to deliver the additional remediations that have been synced, in tandem with the normal automation workloads it’s performing to the RHEL estate.
Subscription requirements
Finally, maybe all of these products aren’t yet actively deployed in your environment, but you might be wondering if you already have the subscriptions needed to take advantage of this architecture, or what might be required to adopt it.
From the subscription standpoint, all that is required for this solution is Red Hat Enterprise Linux with Smart Management, and Red Hat Ansible Automation Platform. To elaborate (as these two subscriptions technically cover all four products included in this solution), the RHEL subscription includes Red Hat Insights and the Smart Management add-on delivers Red Hat Satellite (including any Capsules required to build the full ecosystem).
Finally, Ansible is required for a number of the automation pieces, but is not codependent on the rest of the solution. Should you have any concerns with adding automation to your workstreams, you can still take advantage of a good portion of this solution, forfeiting the automation aspects laid out earlier.
Summary
As you continue to consider this solution for your business, I hope giving a real-world illustration of how our customers are using this solution helps in visualizing how this can fit into your environment so you can take advantage of everything the Red Hat portfolio has to offer.
For additional information on each of the products included in this solution, head over to Red Hat Insights, Hybrid Cloud Console, Smart Management, and Ansible Automation Platform.
If you’d further like to get some guidance in implementing this solution in your organization, please reach out to us. And for other similar multi-product solutions such as this, head over to the Portfolio Architecture Center to review our entire catalog of documented architectures. We’d love the opportunity to help you in this journey.
Sull'autore
Camry Fedei joined Red Hat in 2015, starting in Red Hat's support organization as a Support Engineer before transitioning to the Customer Success team as a Technical Account Manager. He then joined the Management Business Unit in Technical Marketing to help deliver a number of direct solutions most relevant to Red Hat's customers.
Altri risultati simili a questo
AI in telco – the catalyst for scaling digital business
Introducing OpenShift Service Mesh 3.2 with Istio’s ambient mode
Edge computing covered and diced | Technically Speaking
A vested interest in 5G | Technically Speaking
Ricerca per canale
Automazione
Novità sull'automazione IT di tecnologie, team e ambienti
Intelligenza artificiale
Aggiornamenti sulle piattaforme che consentono alle aziende di eseguire carichi di lavoro IA ovunque
Hybrid cloud open source
Scopri come affrontare il futuro in modo più agile grazie al cloud ibrido
Sicurezza
Le ultime novità sulle nostre soluzioni per ridurre i rischi nelle tecnologie e negli ambienti
Edge computing
Aggiornamenti sulle piattaforme che semplificano l'operatività edge
Infrastruttura
Le ultime novità sulla piattaforma Linux aziendale leader a livello mondiale
Applicazioni
Approfondimenti sulle nostre soluzioni alle sfide applicative più difficili
Virtualizzazione
Il futuro della virtualizzazione negli ambienti aziendali per i carichi di lavoro on premise o nel cloud
