Chapter 1: An introduction to the principles of zero trust
Zero trust principles start with making security a foundational component of all projects, whether developing new products or implementing new infrastructure.
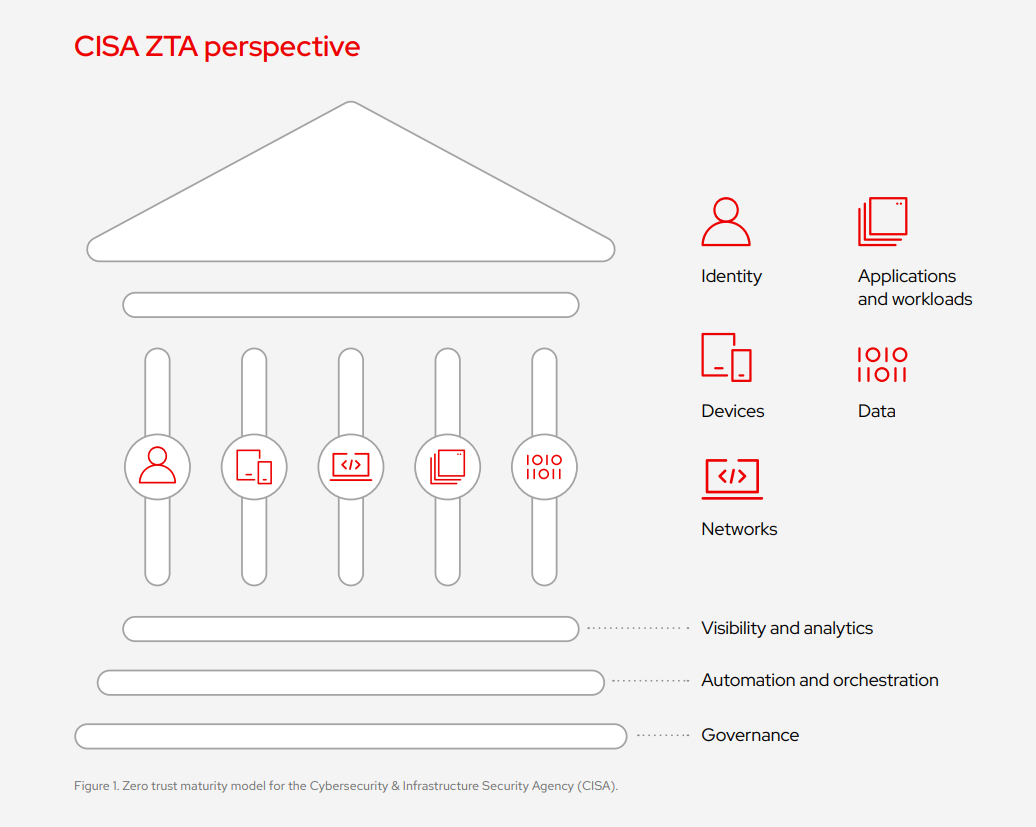
Instead of building security around network access alone, a zero trust architecture, as described by the National Institute of Security in Technology (NIST), is built into every digital interaction as a practice across the organization.
While there are different approaches to zero trust, the following 6 principles can help organizations prepare for and adopt zero trust security.
1. Protect surfaces versus attack surfaces
A government agency can have any number of areas in their IT infrastructure that need to be protected, such as data and critical systems. These areas, known as protect surfaces, will be a catalog of all assets requiring protection and is why inventorying is so critical for any size agency or organization.
Rather than trying to address the entire attack surface of a system, which will likely include vulnerabilities and attack vectors which are of low risk in the context of a particular system, the process of defining a protect surface focuses efforts on defining microperimeters that directly reduce risk.
This can be much more manageable for an enterprise than addressing entire attack surfaces, which may include thousands of common vulnerabilities and exposures (CVEs) spread over many different software or hardware deployment targets and physical locations. The protect surface of a system can be defined by an exploration of the risk and sensitivity levels of each component.
2. Assume breach
This principle assumes that an attacker is already within your defensive security perimeter and that any or all traditional perimeter based security controls are no longer effective. This means that you cannot rely on these controls to mitigate further malicious actions or reconnaissance by that attacker within the overall system or enterprise.
Hostile actors are everywhere and constantly attacking systems, with varying levels of success. Even if an enterprise is not involved in an active security breach, insiders are by definition already operating within a defensive security perimeter and can go rogue in very damaging ways because of that advantage. Most enterprises are also subject to open vulnerabilities and unpatched systems due to the time it takes to patch and update systems, which provides a target rich environment for insiders.
The goal of “assume breach” is not to keep you up all night worrying about your IT systems, but to encourage you to structure your security posture in a way that inherently reduces the impact of any new or ongoing attacks from the perspective of assuming the enterprise always has bad actors actively operating within it.