Common, high-level use cases for security automation
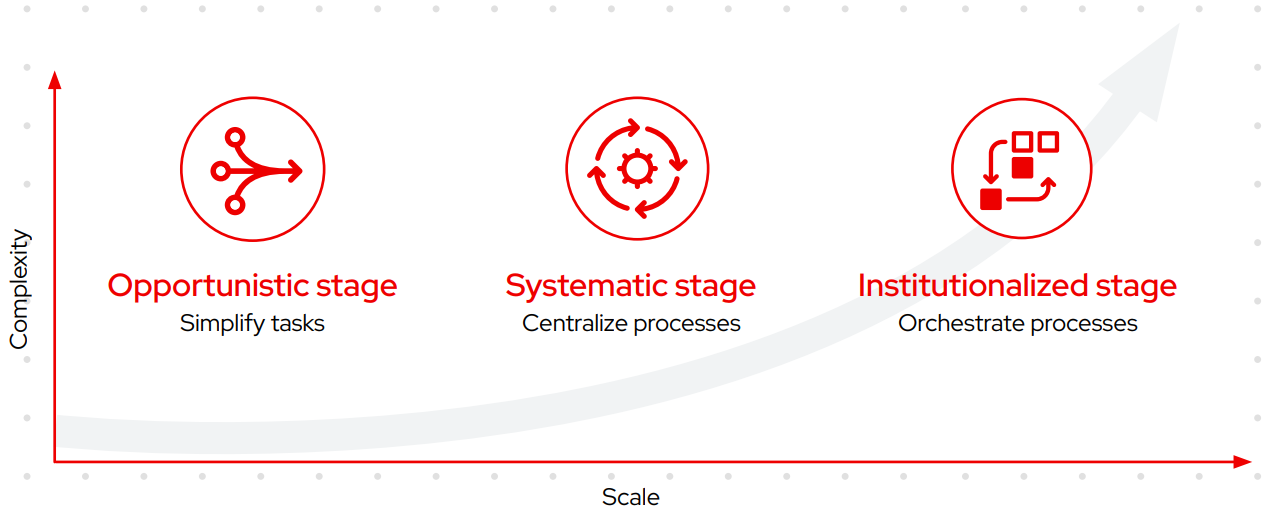
Each of these use cases can serve as a starting point for your security automation journey. The key is to start small and simple, and build over time.
Investigation enrichment
Investigating security alerts and incidents involves collecting information from a variety of security systems to assess whether a legitimate event has occurred. Information is typically gathered through a series of user interfaces, emails, and phone calls. This inefficient process can delay action against threats, leaving your business vulnerable and increasing the potential costs associated with a breach. Automation allows you to programmatically assemble information across your security systems, supporting on-demand enrichment of triage activities performed through security information and event management (SIEM) systems. As a result, you can assess—and respond to—alerts and incidents more efficiently.
Threat hunting
Threat hunting involves identifying and investigating potential threats to security in a proactive fashion. As with incident investigation, staff manually gather and send information between many systems. Using automation, you can customize and streamline alerts, correlation searches, and signature manipulation to swiftly examine potential threats. You can also automatically create and update SIEM correlation queries and intrusion detection system (IDS) rules to improve detection. Consequently, you can update your organization’s security defenses more frequently and efficiently to better protect your business.
Incident response
Incident response involves taking action to stop a breach from continuing. Once a breach is discovered, security staff must respond quickly and at scale to contain it. However, response actions often include multiple manual tasks, slowing remediation time and leaving your organization vulnerable for longer. Automation helps you react faster by codifying actions into repeatable, preapproved playbooks. You can speed tasks like blocking attacking IP addresses or domains, allowing non-threatening traffic, freezing compromised credentials, and isolating suspicious workloads for further investigation to minimize the damage associated with the incident.
Integration is essential
Unified automation approaches require integration between your automation platform and your security technologies. Essential integrations include:
Firewalls control traffic flow between networks, protecting internet-exposed applications. Automation can speed policy and log configuration changes.
Intrusion detection and prevention systems (IDPS) monitor network traffic for suspicious activity, issue threat alerts, and block attacks. Automation can simplify rule and log management.
Security information and event management systems collect and analyze security events to help detect and respond to threats. Automation can provide programmatic access to data sources.
Privileged access management (PAM) tools monitor and manage privileged accounts and access. Automation streamlines credential management.
Endpoint protection systems monitor and manage devices to improve their security. Automation can simplify common endpoint management tasks.
Learn more