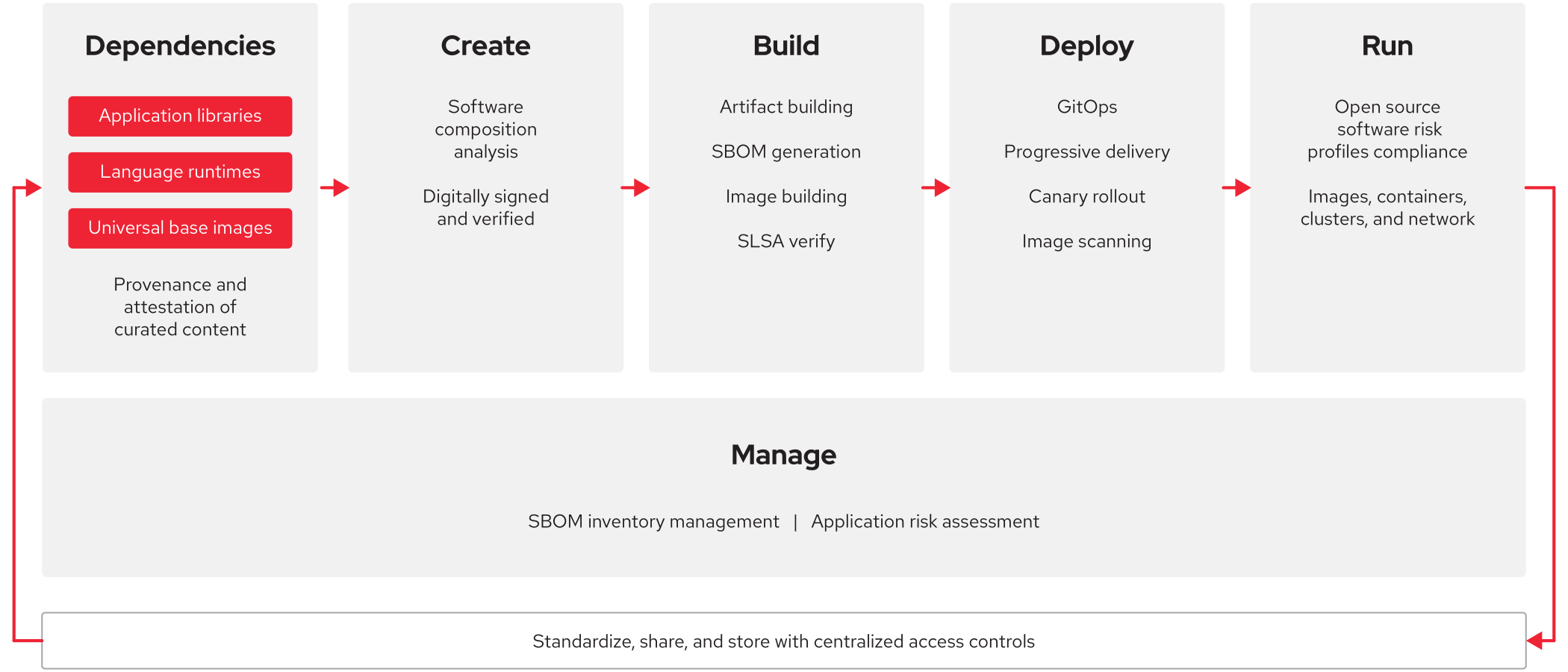
Safeguarding your software supply chain requires a multifaceted approach. There are many things you can do to improve software supply chain security, and each will add another layer of protection for your organization and customers. The following sections discuss key concepts for building security into your software supply chain, along with best practices for implementation.
Software bill of materials
A software bill of materials (SBOM) is a nested inventory of all sources and dependencies—including source code, open source software and libraries, middleware, and development frameworks—that are part of an artifact. There are several industry-wide standards for SBOMs—CycloneDX, Software Package Data Exchange (SPDX), and Software Identification (SWID) tagging, for example—that describe software composition using a uniform language that other tools can understand. Although SBOM contents may vary by company and standard, most contain a manifest, pedigree, and provenance.
- The manifest is a list of the components used to build an artifact. It includes baseline information like the author name, supplier name, version string, component hash, and a unique identifier for each component.
- The pedigree describes how the artifact was produced and descendant, variant, and ancestor relationships. It can also specify modifications made to open source components.
- The provenance describes the chain of custody or path of the software between organizations. It describes where and from whom each component was retrieved.
Industry best practices require SBOMs to be generated as part of the build process, stored in artifact repositories, delivered with associated artifacts, and reviewed regularly by consumers. Creating and maintaining SBOMs can help organizations avoid using and distributing potentially harmful software. Producers can ensure that all components are up to date and respond quickly to new vulnerabilities while consumers can perform vulnerability or license analyses on SBOMs to evaluate the risk of using or deploying an artifact.
Vulnerability Exploitability eXchange
Published by producers, a Vulnerability Exploitability eXchange (VEX) is a machine-readable document that tells consumers if artifacts are impacted by vulnerabilities in upstream components and, if affected, the recommended remediation actions to take. For any combination of artifact and vulnerability, the VEX status can be:
- Not affected. No remediation is required.
- Affected. Actions are recommended to remediate the vulnerability.
- Fixed. The product version contains a fix for the vulnerability.
- Under investigation. It is not yet known whether the artifact version is affected by the vulnerability.
Producers and consumers can integrate SBOM and VEX information for a current view of the status of vulnerabilities in software products. You can take a targeted approach to finding and remediating vulnerabilities and reduce the number of investigations into nonexploitable vulnerabilities.
Attestation
Used by producers to make statements about the artifacts they deliver, software attestations are trust mechanisms based on authenticated, machine-readable metadata. Whether included in an SBOM or delivered separately, attestations allow consumers to independently validate the integrity of these statements from producers. While implementation details vary across organizations, all attestations include a subject, content or statement, and a signature.
- The subject is the list of artifacts to which the attestation applies.
- The content is 1 or more statements about the artifacts that the producer knows to be true.
- The signature is a tamper-resistant mechanism that denotes and authenticates the producer that created the attestation.
Although producers can attest any fact related to an artifact, there are several common types of attestations in a typical software supply chain. Attestations that inventory resources used by the build platform like server operating systems, cloud regions, and security groups, along with their current state, affirm the security of the build environment. Attesting build platform components like compilers and vulnerability scanning tools check that the appropriate tools are used to create and test artifacts. Identifying the provenance and pedigree of sources and dependencies in attestations helps consumers verify that the correct files were used to build artifacts. Since multiple artifacts are often created in a single build process, attesting relationships between artifacts helps producers and consumers track artifacts and ensure consistency.
Secure Software Development Framework
Published by NIST, the Secure Software Development Framework (SSDF) is a set of fundamental, security-focused practices that can be applied to software development life cycle models. Based on established standards, guidance, and documentation, the SSDF includes practices that both directly and indirectly impact software artifacts to help producers increase the security of their software development processes.
The SSDF groups best practices into 4 categories of recommendations:
- Prepare the organization. Ensure that people, processes, and technology are ready for security-focused software development.
- Protect the software. Safeguard software components from tampering and unauthorized access.
- Produce well-secured software. Produce security-focused software with minimal vulnerabilities.
- Respond to vulnerabilities. Identify vulnerabilities in software releases, address them as needed, and act to prevent similar occurrences in the future.
Producers and consumers can use these recommendations to strengthen their existing software development practices, establish requirements for third-party suppliers, and acquire software that meets fundamental best practices.
Supply-chain Levels for Software Artifacts
Supply-chain Levels for Software Artifacts (SLSA) is a set of security guidelines established by industry consensus to help producers protect their software supply chains and build confidence and trust with consumers.
A key component of these guidelines, SLSA provenance is an attestation that is created and signed by build platforms. It describes how artifacts are built, including the building entity, process, and inputs. Producers can follow SLSA build requirements to strengthen their software supply chain security. Consumers can follow SLSA verification recommendations to evaluate the trustworthiness of artifacts.
SLSA defines 4 build process levels that describe the trustworthiness and completeness of an artifact’s SLSA provenance. While higher levels provide greater guarantees against supply chain threats, they incur higher implementation costs. For each artifact, producers can align with the build process level that meets their needs and implement higher levels as requirements change.
Software supply chain security best practices
There is no one best way to secure your software supply chain. Instead, there are many best practices— based on the concepts discussed in the previous sections—that you can use to incrementally improve your software supply chain security.
Best practices that apply to sources
- Educate developers on and enforce secure coding best practices.
- Perform security-focused peer code reviews, analysis, and testing.
- Require and automate source code scanning with software linting and SAST tools continuously throughout all phases of the software supply chain.
- Actively manage dependencies in sources.
- Reuse existing, security-tested sources whenever possible.
- Require signed commits for all source repository submissions.
- Scan source repositories to ensure that secrets are not committed.
Best practices that apply to dependencies from open source organizations
- Thoroughly research and investigate open source artifacts before using them.
- Download and use open source artifacts from trusted sources.
- Verify the provenance of all dependencies before building them.
- Obtain and thoroughly review SBOMs for all open source artifacts.
- Automatically scan all open source dependencies with SAST tools.
- Use SCA tools to detect transitive dependencies in open source artifacts.
- Keep open source artifacts up to date with tools that automatically monitor dependencies in your source repositories for new releases.
Best practices that apply to dependencies from third-party software producers
- Establish security requirements and controls for producers that are at least as rigorous as those used internally.
- Work with producers that follow DevSecOps practices throughout their entire software development life cycle.
- Require and review SBOMs from producers for each release.
- Verify the provenance of all third-party artifacts before integrating or deploying them.
- Choose producers with product vulnerability response programs that identify, disclose, and quickly fix vulnerabilities in both their sources and artifacts.
- Ensure that producers certify their products to industry security standards and submit artifacts for external assessments.
- Require producers to verify that all third-party artifacts incorporated into their code comply with all security controls.
Best practices that apply to container images
- Use container images—including base and parent images—from trusted sources.
- Verify the provenance of all downloaded container images.
- Avoid images that are updated infrequently, especially if they do not contain relevant vulnerability disclosures.
- Opt for minimal base images with only the required operating system packages and frameworks.
- Create containers by installing the exact tools and libraries your application requires rather than removing components from an existing image
- Scan images for vulnerabilities early, often, and in multiple places, including developer workstations, CI/CD platforms, image registries, and actively running containers.
- Keep containers up to date by rebuilding, testing, and redeploying with the latest software patches.
- Monitor containers for newly discovered vulnerabilities throughout their entire life cycle.
- Avoid deploying containers with known vulnerabilities by removing old images from registries.
- Manage any necessary secrets carefully and grant only minimal required permissions.
Best practices that apply to build processes and platforms
- Follow SLSA guidelines for reproducible builds on hosted and isolated platforms.
- Implement build platforms using CI/CD pipelines with automated security and developer guardrails.
- Use only security-focused components—like hardened container images and artifacts and checksum-verified tools—in your build processes.
- Ensure all steps of your build process are properly configured and pay close attention to changes in tools, scripts, and configuration files.
- Scan dependencies’ SBOMs for security risks and generate SBOMs for newly built artifacts as part of automated CI/CD pipelines.
- Automate provenance verification for all dependencies, along with provenance generation and attestation for newly built artifacts.
- Scan dependencies automatically for vulnerabilities using SAST tools.
Best practices that apply to infrastructure used in your software supply chain
- Set and enforce software download and installation policies for developer workstations.
- Follow least privilege principles by restricting direct access to repositories, build platforms, and deployment services, and use multifactor authentication and dedicated nonhuman accounts where possible.
- Use tools to encrypt, store, and manage secrets and credentials and enforce access controls.
- Automate infrastructure deployment using IaC and GitOps techniques.
- Monitor infrastructure for configuration drift and automatically apply updates, based on your latest IaC definitions.
- Use dedicated security tools to scan IaC files and identify vulnerabilities and misconfigurations across your entire IT environment.
- Place CI/CD pipeline infrastructure within your network perimeter and pay attention to changes in pipeline configuration.
Best practices that apply to deployment and run processes in your software supply chain
- Manage application configuration using industry best practices like analyzing the security impacts of requested privileges, allowing only the minimum required services and permissions, and defining configurations as code stored in repositories.
- Test applications and infrastructure in isolated, preproduction environments before deploying to production.
- Scan running workloads automatically for vulnerabilities and misconfigurations and use defined processes for triaging and mitigating suspected issues.
- Monitor deployed applications and container images for security updates.
- Use expected software behavior and analytics—including artificial intelligence and machine learning (AI/ML) techniques—to implement data controls and detect potentially malicious activities.
- Employ deliberate network segmentation to confine vulnerabilities to a portion of your IT environment.