IDC’s Open Source and Digital Sovereignty Come Together paper2 defines 6 key strategic goals of digital sovereignty:
- Cybersecurity
- Transparent IT operations
- Trusted data management
- Strategic resilience
- Digital economy and skill development
- Interoperability and reversibility
Service providers can achieve these goals by addressing the different dimensions of digital sovereignty. When bringing together digital sovereignty and open source software, service providers will be able to deploy and orchestrate scalable, resilient, trusted, interoperable, and portable (or reversible) infrastructure and services that support open and sovereign requirements.
In this context, reversibility and portability are similar concepts, though not identical. Portability generally refers to the ability to migrate workloads, data, applications, and operations between environments; Reversibility extends beyond environments, and acknowledges the business, legal, and cultural impacts that a migration or vendor change entails. Portability may be considered a subset of reversibility. Note that this is also related to more long-standing concepts of reversibility in thermodynamics, in that they both require the ability to decompose systems into their component parts without losing any pieces.
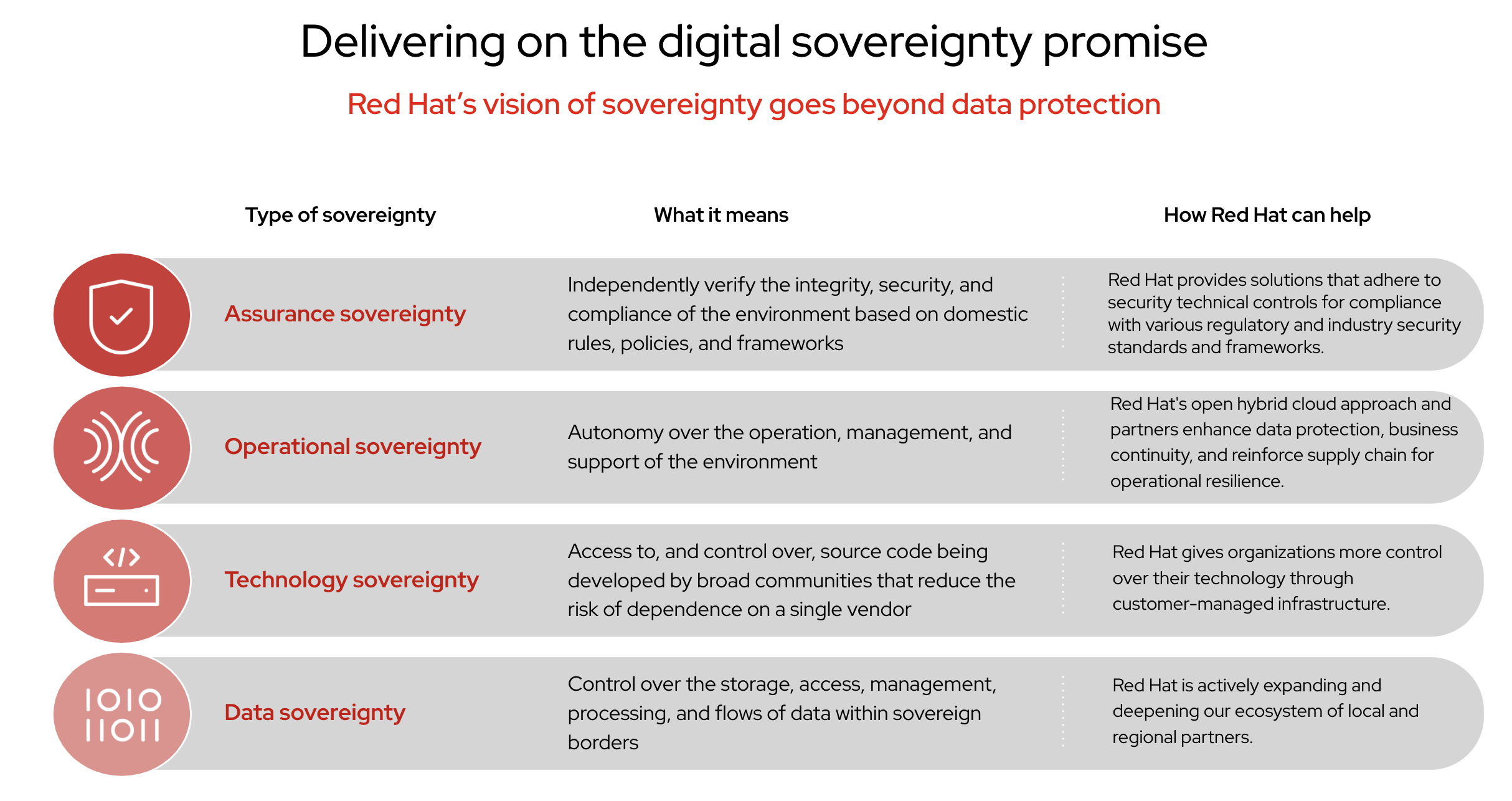
Data sovereignty
Data sovereignty encompasses the legal and ethical governance and management of storage, access, management, processing, and the flow of data within a service provider’s sovereign borders. A digital sovereignty solution must operate in compliance with local regulations, including privacy laws, data residency requirements, and consent frameworks.
Data governance and management must reflect cultural and societal expectations, particularly when biometric data, healthcare data, or financial information are present. To maintain control over sensitive and critical data, service providers invest in trusted data infrastructures and federated data platforms. To maintain trust, compliance, and competitive advantage, service providers must have a robust cybersecurity strategy that defines who is able to govern the access, analysis, and sharing of data in multicloud and cross-border scenarios.
To address data sovereignty, Red Hat’s ecosystem of local and regional partners gives service providers options for storing and processing data locally. These options allow customers to decide where data resides and how it is controlled and handled.
Technology sovereignty
Technology sovereignty includes customer-managed infrastructure, as well as access to—and control over—source code and platforms across the entire technology environment. The ability to independently design, build, and operate systems allows service providers to offer strategic resiliency, a foundational element for public services and competitiveness. Technology sovereignty is often extended towards the supply chain, to mitigate the risk of dominant manufacturers. Adopting a flexible hardware strategy can help reduce vulnerability to risks like geopolitical tensions, export controls, or external platform dependencies.
To address technology sovereignty, Red Hat provides customer-managed infrastructure options that give service providers the flexibility to choose where workloads are deployed, and on what hardware. Additionally, our open source approach provides access to and control over source code, reducing the risk of vendor lock-in and letting service providers adapt technologies to meet their specific needs.
Operational sovereignty
Operational sovereignty brings autonomy over the operation, management, and support of the service provider environment. It includes governance over the authority, skills, and access to operate and maintain sovereign solutions by locally trusted service provider personnel. Many national policies are beginning to mandate that critical digital infrastructure must be supported by staff of specific nationality or within legal jurisdictions, in order to reduce reliance on external managed services and support.
Red Hat’s open hybrid cloud solutions and our partner ecosystem strengthen business continuity capabilities, provide a path to operational resilience and transparent IT operations, and give service providers the autonomy needed to manage their environment effectively.