- The QM partition, represented as the Podman container, operates within its namespace, providing a controlled and isolated environment.
- The namespace customizes the QM partition's view of the system’s file structure and resources, effectively hiding resources like hardware devices, network interfaces, and shared memory segments that are not allocated to the partition.
In Linux, resources such as devices and files are represented as entries in the file system. By restricting the namespace:
- Resources not mapped to the QM partition’s namespace are completely invisible to applications within the partition.
- If a hardware device or file is not explicitly allocated, it does not appear in the QM partition’s directory tree, making it inaccessible to QM applications.
This layered isolation, combined with other kernel isolation features, ensures that applications within the QM partition remain fully segregated, safeguarding the integrity of safety-critical workloads and maintaining compliance with mixed-criticality requirements.
Kernel address space FFI
Ensuring spatial isolation at the kernel level is a critical challenge in achieving FFI in mixed-criticality systems. In Red Hat In-Vehicle OS, kernel code supporting the mixed-criticality architecture and used by ASIL B applications is ASIL B qualified. To support safety claims, the remaining code is analyzed and verified to ensure it does not interfere with ASIL B functionality.
Unlike user-space isolation, achieving spatial isolation within the kernel requires a multifaceted, layered strategy.
Key strategies for kernel spatial isolation
- Scope reduction of remaining kernel code: Unnecessary kernel code is identified and excluded from the Red Hat In-Vehicle OS image, reducing the attack surface and simplifying verification for functional safety.
- Runtime safety mechanisms: Red Hat In-Vehicle OS uses kernel-level protections to detect and mitigate issues such as memory corruption, unsafe access, and reference counter overflows or underflows. These mechanisms are validated through targeted fault injection to confirm their effectiveness under stress conditions.
- Driver certification and risk assessment: Kernel-mode drivers undergo extensive risk assessments to evaluate their safety and compliance.
- In-tree drivers: These are certified by Red Hat, ensuring adherence to stringent safety standards.
- Out-of-tree or loadable modules: Partners are required to certify these drivers to ASIL B or higher, ensuring that only verified modules can operate within the system.
- Binary kernel with controlled access: Red Hat In-Vehicle OS kernel restricts symbol exports, limiting the ability to introduce unvetted modifications. This controlled access prevents developers from inadvertently compromising the kernel’s spatial isolation mechanisms.
- Verification across interference types: Red Hat supports its functional safety claims for Red Hat In-Vehicle OS through a dedicated verification campaign focused on spatial, temporal, and resource interference.
- Spatial interference: A kernel fuzzing campaign targets all system calls exposed to the nonsafety domain using a KASAN-enabled kernel. The tests must meet predefined safety and reliability criteria.
- Temporal interference: Verified through latency testing on safety-critical workloads while stressing the nonsafety domain with the LTP syscall suite.
- Resource interference: Validated by confirming that resources allocated to safety-critical functions remain isolated when the nonsafety domain is under stress.
- External watchdog validation: An external ASIL B hardware watchdog acts as a final safeguard.
By combining these strategies, Red Hat In-Vehicle OS reduces the risks of spatial interference within the kernel, ensuring a stable and security-focused platform for mixed-criticality workloads.
Interprocess protection within a partition
Within Red Hat In-Vehicle OS, Unix-style process protection ensures that individual processes running inside any container, including the QM partition or within the ASIL space, are isolated from one another. For instance, if a QM application spawns multiple processes, kernel-level mechanisms, such as memory access restrictions and process IDs, prevent these processes from interfering with one another.
These protections, while integral to maintaining stability and reliability within a partition, are not the primary focus of this document, as they do not directly contribute to the FFI claims being addressed.
Hardware involvement
The Red Hat In-Vehicle Operating System relies on essential hardware capabilities to enforce isolation mechanisms critical for mixed-criticality workloads. These include:
- Memory management unit (MMU): Enforces spatial isolation by applying virtual memory policies configured by the kernel's memory management system.
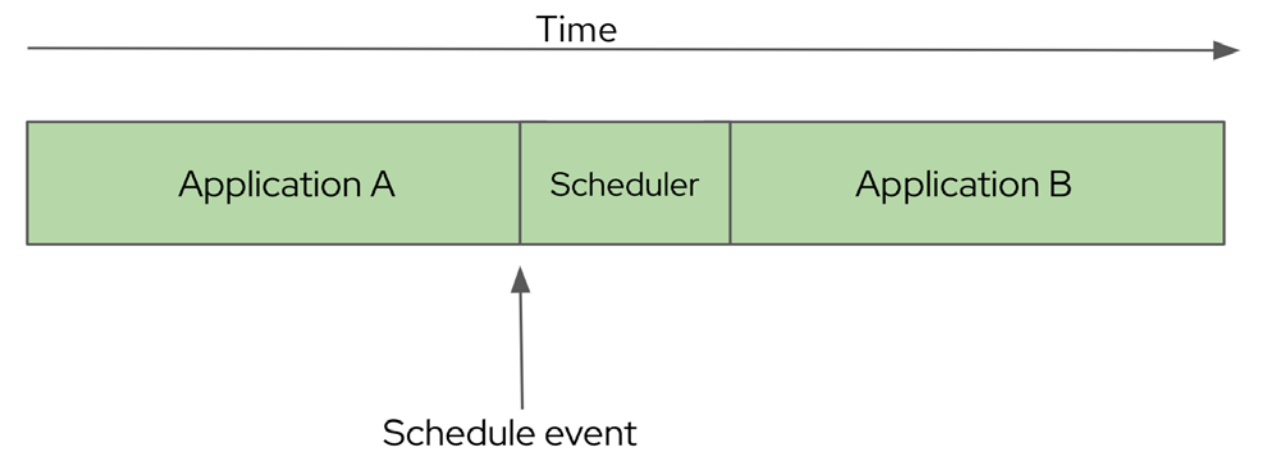
- Clocks and timers: Generate scheduler events required for maintaining temporal isolation.
- CPU privilege levels: Protect isolation mechanisms by preventing user-space applications from altering configurations established by the kernel, scheduler, and Podman.
These hardware capabilities are initialized during startup, ensuring the system is fully equipped to enforce isolation before user applications are instantiated.
Failure modes and risk management for mixed-criticality
Red Hat In-Vehicle OS incorporates robust mechanisms to address failure modes associated with mixed-criticality workloads. Potential failure scenarios are analyzed as part of a comprehensive fault tree analysis.
Specific risks associated with the QM partition, such as interference with safety-critical applications, are identified, and mitigation strategies are implemented. These strategies are managed and monitored through Red Hat’s safety lifecycle, ensuring compliance with functional safety standards.
For more details, please contact Red Hat at automotive-requests@redhat.com