With the release of Red Hat Enterprise Linux 9.2 (RHEL), it's possible to run the Technology Preview of RHEL on an Azure confidential virtual machine (CVM). In a previous article, I provided the high-level requirements for a Linux operating system to support a CVM use-case, as well as the changes made to the RHEL 9.2 operating system to support the features provided by Azure CVMs to ensure data confidentiality. In this article, I focus on how to get access to the CVM Preview image, and how to launch an Azure CVM using that image.
Get the CVM Preview image
In May 2023, Microsoft announced the availability of a RHEL 9.2 Preview confidential image tailored for AMD SEV-SNP CVMs on Azure. The support for Azure CVMs is a Technology Preview feature of Red Hat Enterprise Linux 9.2, developed in close collaboration between Red Hat and Microsoft. The "Technology Preview" status of the feature means that at this moment it's not suitable for production environments, but you can use it for non-production workloads. This gives you the opportunity to provide invaluable feedback and suggestions. The main goal of the Technology Preview is to verify that the feature works well for customer use-cases when it becomes fully supported in a future Red Hat Enterprise Linux release.
Running Azure CVM with RHEL 9.2 Preview confidential image
Once you've signed up for access to the RHEL 9.2 Preview confidential image, you can get the image using this direct link.

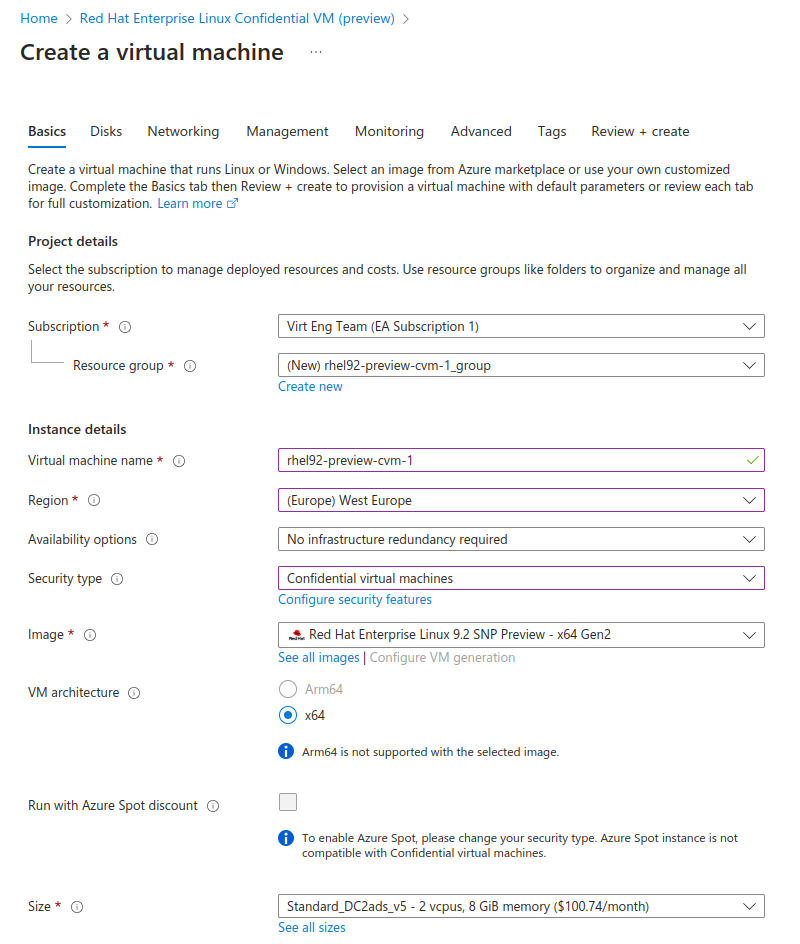
When creating a new Confidential VM using Azure Portal, make sure you set Security type to Confidential virtual machines, using one of the SEV-SNP CVM instance types (DCasv5, ECasv5) for Size setting.
To ensure data protection at rest, full disk encryption at the guest's side must be enabled. To do that, enable Confidential compute encryption in the Disks tab:

CVM instances may not be available in all Azure regions.
VM configuration
As a CVM owner, verify that your guest is running inside a genuine AMD SEV-SNP virtual machine. Microsoft provides documentation on Azure Confidential VM attestation. With RHEL 9.2 CVM Preview image, the basic test can be performed with the following sequence:
- In the guest, install the required packages:
$ sudo yum -y install jq
- Get the VCEK certificate from the metadata endpoint:
$ curl -H Metadata:true http://169.254.169.254/metadata/THIM/amd/certification > vcek $ cat ./vcek | jq -r '.vcekCert ' > ./vcek.pem
- Get get SNP report from the vTPM NVRAM
$ sudo tpm2_nvread -C o 0x01400001 > ./snp_report.bin $ sudo dd skip=32 bs=1 count=1184 if=./snp_report.bin of=./guest_report.bin
- Copy the vcek.pem and guest_report.bin files to a trusted environment, which can be, for instance, an on-premises RHEL 9 installation. In this example, files are placed in the ~/cvm_data directory on the target host.
- Install the snpguest tool:
(trusted)$ sudo yum -y git cargo rust (trusted)$ git clone https://github.com/virtee/snpguest.git (trusted)$ cd snpguest (trusted)$ cargo build
- Validate the VCEK certificate:
(trusted)$ target/debug/snpguest fetch ca Milan ~/cvm_data/ (trusted)$ target/debug/snpguest verify certs ~/cvm_data/ The AMD ARK was self-signed! The AMD ASK was signed by the AMD ARK! The VCEK was signed by the AMD ASK!
- Validate guest report:
(trusted)$ target/debug/snpguest verify signature ~/cvm_data/ \ -a ~/cvm_data/guest_report.bin VCEK signed the Attestation Report! (trusted)$ target/debug/snpguest verify tcb ~/cvm_data/ \ -a ~/cvm_data/guest_report.bin Reported TCB Boot Loader from certificate matches the attestation report. Reported TCB TEE from certificate matches the attestation report. Reported TCB SNP from certificate matches the attestation report. Reported TCB Microcode from certificate matches the attestation report. Chip ID from certificate matches the attestation report.
This is a simplified procedure and may, in some cases, require modification. In particular, there's no verification that the provided guest report was generated for this particular instance and not somewhere else. For the additional information on Azure Attestation, refer to the documentation provided by Microsoft.
Conclusion
The RHEL 9.2 Preview confidential image is currently a Technology Preview in RHEL 9, and not yet meant for production workloads, but it's an important indication of the future of cloud computing. If you're interested in Confidential VM technology, try it out and give us feedback on what you find. Let us know whether the image works for your use cases and what you would like to see in the future RHEL releases!
About the author
More like this
OpenShift Virtualization 4.21: Removing complexity from your virtual machine networking workflow
Red Hat partner ecosystem: A year of expanding choice for virtualized workloads on Red Hat OpenShift Virtualization
SREs on a plane | Technically Speaking
Browse by channel
Automation
The latest on IT automation for tech, teams, and environments
Artificial intelligence
Updates on the platforms that free customers to run AI workloads anywhere
Open hybrid cloud
Explore how we build a more flexible future with hybrid cloud
Security
The latest on how we reduce risks across environments and technologies
Edge computing
Updates on the platforms that simplify operations at the edge
Infrastructure
The latest on the world’s leading enterprise Linux platform
Applications
Inside our solutions to the toughest application challenges
Virtualization
The future of enterprise virtualization for your workloads on-premise or across clouds
