DEPARTMENT OF DEFENSE
Move faster, with less risk
As the Department of Defense (DoD) moves to modernize its widespread resources, getting to mission capability faster is increasingly dependent on IT security. Red Hat has the open source technology and expertise to partner with the DoD to innovate with agility, standardize interoperability across all branches and agencies, and still maintain a high security protocol.
If you want security, you need flexibility
When a mission is critical, agility is everything. See how Red Hat’s open and flexible hybrid approach can help the DoD connect clouds, teams, and processes.
Red Hat solutions support DoD operations
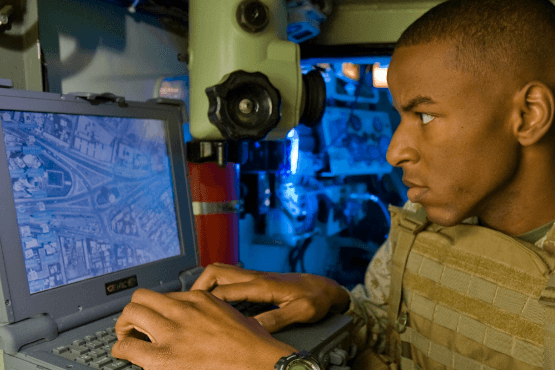
When each military branch brings its own expertise and technology to the battlefield, it’s necessary to integrate all critical data simultaneously across air, land, sea, space, and cyber domains to effectively coordinate and control operations.
Pillars of faster, flexible, secure technology
Mission Edge
Stay flexible with mission edge
Build multidomain operations (MDO) that can distribute and manage high-data volume workloads quickly, resiliently, and dynamically, and simultaneously support the volume and velocity of data, no matter where devices are in the field.
Resources
Dev Sec Ops
Stay secure with DevSecOps
Respond to evolving threats with next-level agility by integrating security throughout the entire IT lifecycle, securing assets and intelligence across all branches and agencies, all while developing and deploying capabilities more rapidly.
Automation
Stay agile with automated solutions
Scale quickly and dynamically to ensure a consistent, rapid, repeatable deployment of underlying infrastructures with an industry-leading automation platform.
Take advantage of a true hybrid experience
Explore Joint Warfighting Cloud Capability
Red Hat provides common foundations and portability for true hybrid cloud and multicloud experiences. You can purchase Red Hat software using your committed spend or bring your own Red Hat software and install it into the Joint Warfighting Cloud Capability (JWCC). Red Hat software can be acquired through Amazon Web Services (AWS), Microsoft Azure, and Google Cloud Marketplaces in public, government, and IC regions.
5 ways government can innovate with Azure
Certifications and contracts
Cloud in Government
AWS
Amazon Web Services (AWS)
Enhance agility, accelerate deployments, and strengthen your security posture with Red Hat solutions on AWS. Explore these resources to learn more about the power of AWS.
Microsoft Azure
Microsoft Azure
No matter where IT organizations are in their digital transformation journey, Red Hat and Microsoft can help them gain control of hybrid cloud complexity, embrace cloud-native application development, and succeed in fast-moving competitive markets.
Google Cloud
Red Hat solutions on Google Cloud work together to speed cloud migration and enhance cloud operations so you can focus on business innovation. Use these resources to help you take advantage of the smoother, faster operations that depend on Google Cloud.
Red Hat and Veterans
Prepare, support, connect
Skills training
With the help of the Training With Industry (TWI) grant, active duty service members gain real-world industry experience and skill development that offer an enhanced understanding of products and processes, to help them create a direct impact within their organizations.
Mentorship
Red Hat is a partner within the America Corporate Partnership (ACP) mentor program to ensure transitioning veterans have a customized pairing with corporate professionals on their path toward fulfilling, long-term careers in the civilian workforce.
Connection
IBM SkillsBuild provides free training to obtain the Red Hat Certified System Administrator certification. To enroll, register with VetJobs/CASY at your local education office.
Keep reading
Explore more Red Hat resources for DoD
Mission Edge
- Use cases and benefits of Red Hat Enterprise Linux
- Automate decisions at the military tactical edge
Automation
- An IT executive's guide to automation
- Download the e-book on Zero Trust automation
Why Red Hat?
Red Hat’s holistic approach to digital transformation can help the DoD jumpstart its modernization efforts and serve as a reliable partner throughout the entire process. As the DoD seeks technology to move faster - and with less risk - our open hybrid cloud approach and comprehensive edge solutions can equip the DoD to reach mission capability faster and effectively conduct military operations across all service branches and agencies.