In today's rapidly evolving technology landscape, organizations increasingly embrace containerization to achieve greater scalability, portability, and efficiency in their application deployments. While containerization has its benefits, it also can present IT security challenges that must be addressed to improve the safety, confidentiality, and accessibility of containerized applications. As the use of cloud-native apps grows, improving the security posture of containers and Kubernetes becomes vital.
In secure software supply chain practices, a comprehensive understanding of the open source products utilized within an organization is crucial. According to the 2021 Future of Open Source Survey, conducted by Black Duck Software and North Bridge Venture Partners approximately two-thirds of companies rely on open source software, assessing the security practices and potential vulnerabilities associated with these technologies becomes paramount. According to the 2023 State of Open Source Security Report by Snyk, the average application has 49 vulnerabilities and 80 direct dependencies (open source code called by a project). The report also found that only 49% of organizations have a security policy for open source software development.
By actively staying informed about the open source code in use, your organization can better integrate trusted components into your software supply chain. This involves evaluating the features, security measures, and ongoing maintenance of specific solutions. It also entails monitoring software supply chain risks, such as compromised dependencies or vulnerabilities in third-party libraries.
According to the key findings based on IBM Security analysis of research data compiled by Ponemon Institute, the average total cost of a data breach reached an all-time high of USD 4.45 million in 2023. The latest report states that the average cost for this year is USD 4.45 million, reflecting a 2.6% increase compared to last year's average cost of USD 4.24 million. Additionally, this represents a significant 12.7% increase from USD 3.86 million in the 2020 report.
The IBM study found that 83% of organizations have experienced more than one data breach, and only 17% reported a data breach as their first one. Preventing potential data breaches, which could lead to reputational damage, financial loss, legal liability, regulatory fines, and productivity loss, is critical in containerization, hence the need for preemptive security measures to avoid escalating service or product costs.
The study also found that the rise of artificial intelligence (AI) and edge technologies has further contributed to increased security breaches. According to recent reports, AI/edge technologies have witnessed a significant surge in security incidents, with a staggering 300% increase in reported breaches compared to 2021.
The nature of AI/edge systems, with their distributed architecture and interconnected devices, presents unique security challenges. Deploying machine learning (ML) models on edge devices and processing sensitive data at the edge can introduce additional vulnerabilities and potential attack points.
Red Hat OpenShift can help improve your organization's security posture, helping manage image security, secrets, monitoring, and maintenance. You'll delve into image security policies, Red Hat Quay, and code signing with Sigstore, Tekton Chain, and Cosign for added protection. Our comprehensive guidelines provide the tools to strengthen your containerization environment and better secure your apps. By implementing these best practices, you can reduce potential risks and establish a stronger security foundation with Red Hat OpenShift.
Shift left strategy: Implementing security early in the software development lifecycle
Application development and deployment is a top priority for many organizations. Developers use the "shift left" strategy to help improve application security. This strategy involves integrating security practices and testing early in the development process. This is especially important in containerization and when using OpenShift.
To understand shift left, let's first define "developer flow." Developer flow is the process of development in which the developer goes through two "loops" that represent pre-release phases. The developer will enter the creative phase, or "inner loop," where the code is developed. Then the "outer loop" is released to production. This process is illustrated in the diagram below.
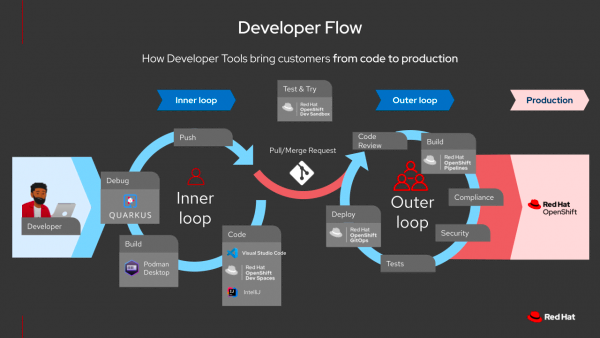
Figure 1: Developer Flow
Inner loop: The inner loop is a frequent iteration cycle involving writing, compiling, running, and debugging code. The focus is on making small changes, testing them, and getting feedback quickly. It's all about rapid development and ongoing validation of code changes.
Outer loop: When it comes to the outer loop, it's essential to have a well-defined approach dedicated to decision-making and progress monitoring. This involves overseeing system integrations, driving compliance, and tackling high-level issues. Regular checkpoints, evaluations, and feedback loops should be established to help ensure everything stays on track.
In addition, it's essential to prioritize open source dependencies for IT security and integrity purposes, especially in light of recent vulnerabilities. Staying informed, applying patches promptly, and utilizing tools like Software Bills of Material (SBOM) to manage components effectively are all keys to achieving your objectives.
The shift left strategy is a fundamental approach that emphasizes integrating security practices early in the development process. Your organization can identify and address discovered vulnerabilities at the earliest stages, reducing the risk of significant security issues arising later.
In the shift left strategy, the inner loop plays a crucial role, focusing on the code and dependencies security aspects of application development. Developers incorporate security practices into their workflows, such as more secure coding practices, code reviews, static and dynamic code analysis, and automated vulnerability scanning. By actively addressing security concerns within the inner loop, developers can catch and rectify vulnerabilities promptly, promoting greater security in coding practices and reducing the likelihood of introducing exploitable weaknesses.
The inner loop also encompasses integrating security testing and quality assurance activities, including unit testing, integration testing, and security-focused testing. By incorporating security testing early, developers can proactively identify and resolve vulnerabilities, ensuring that the application functions securely and as intended.
Moreover, the shift left strategy encourages collaboration and communication between development and security teams. Developers gain insights into security best practices, threat modeling, and secure design principles by involving security experts from the start. This collaborative approach fosters a security-conscious mindset within the development team and facilitates the early detection and mitigation of security risks.
Overall, the shift left strategy brings security considerations to the forefront of the development process. By embedding security practices in the inner loop, your organization can build more secure applications, reduce the potential impact of security breaches, and ultimately deliver higher-quality software that prioritizes protecting sensitive data and user privacy.
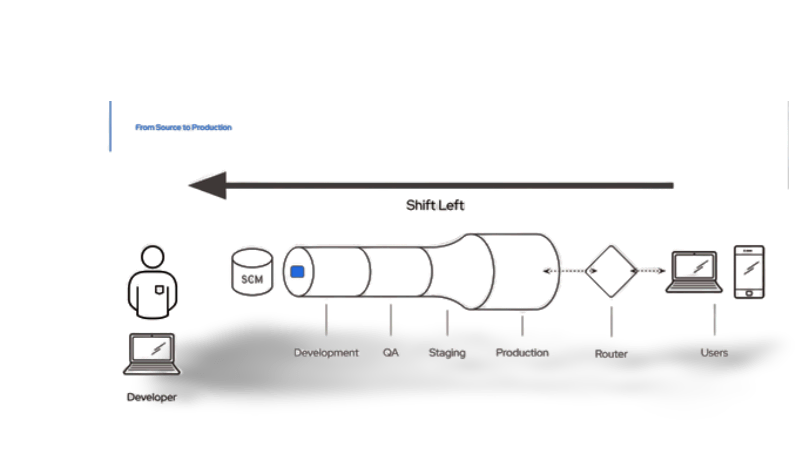
Figure2 : Shift Left Strategy
Implementing a shift left strategy with SBOM: Strengthening security in the early stages of the software development lifecycle
It's no secret that open source software has become more prevalent in recent years, offering a range of benefits to developers. However, open source software is not immune to security risks, and vulnerabilities can arise due to the complex interdependencies within the software ecosystem.
A recent example that highlights the importance of addressing security risks is the log4j vulnerability, commonly referred to as "log4shell." Log4j is a widely used Java-based logging library in various applications, and in December 2021, a critical vulnerability was discovered that allowed attackers to execute arbitrary code remotely. This vulnerability significantly affected numerous organizations and called attention to why it's critical to proactively manage and secure open-source dependencies.
Another notable example is the Heartbleed vulnerability, which exposed a critical security flaw in the OpenSSL cryptographic library. This vulnerability affected many websites and applications, allowing attackers to access sensitive data such as passwords and private keys. The incident served as a wake-up call for organizations to prioritize the security of their open-source dependencies and actively monitor for vulnerabilities.
To tackle these challenges, the Software Bill of Materials (SBOM) has emerged as a crucial tool for enhanced supply chain security. With SBOM, your organization can more easily track all software components and their dependencies, including open source libraries and frameworks, within a containerized application.
This level of visibility enables timely updates and patches, reducing the risk of exploiting known vulnerabilities and providing an application environment with a stronger security profile. If you're using Red Hat OpenShift, you can leverage SBOM to enhance your supply chain security further. OpenShift provides a powerful container orchestration and management platform, making it an ideal environment to integrate SBOM practices.
Integrating a shift left strategy with SBOM prioritizes security measures early in the software development lifecycle, helping enable proactive vulnerability management and enhanced supply chain security for containerized applications. By incorporating SBOM into your vulnerability management processes, you can identify, prioritize, and address security risks more effectively, collaborate with upstream open source communities for patches and updates, and establish a robust supply chain security framework. With this approach, you can maintain a more secure containerized environment in OpenShift while enjoying open source projects' flexibility and innovation.
Code signing with Sigstore: Validating software authenticity and integrity
Code signing is essential for maintaining a secure software supply chain in today's interconnected world. Sigstore is an open source project that offers a security-focused and decentralized approach to code signing within Red Hat OpenShift.
It simplifies the code signing process and enhances overall security by providing a verifiable trail of trust. Integrating Sigstore into the development and deployment workflow is easy, thus enforcing that container images and software artifacts undergo the signing process as part of the CI/CD pipeline.
By embracing code signing with Sigstore, your organization can more confidently deploy containerized applications, knowing that your software has not been tampered with.
Implementing image security policies and image signing with OpenShift Pipelines Tekton Chains (Tech Preview) and Cosign
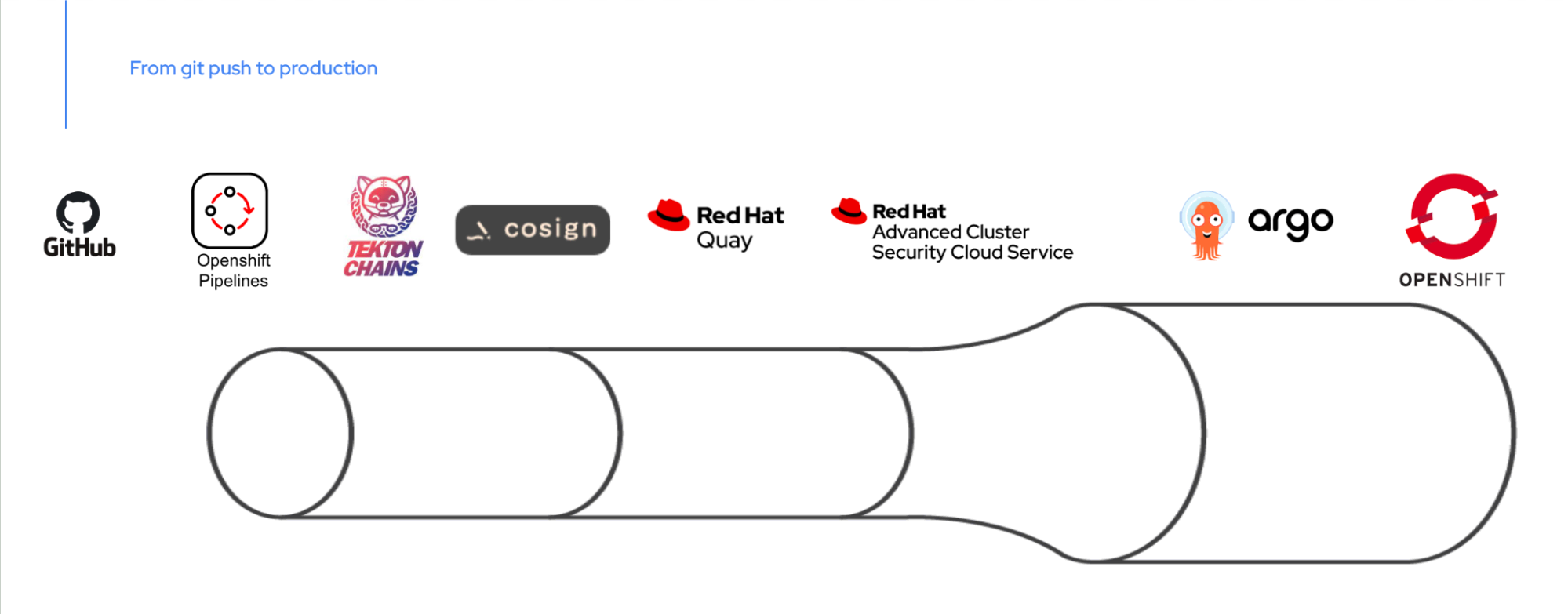
Figure 3: Red Hat OpenShift Platform Plus
In Red Hat OpenShift, your organization can enhance the security of your containerized applications by implementing image security policies and leveraging tools like Tekton Chain and Cosign for image signing. These measures help build confidence in the authenticity and integrity of container images before deployment.
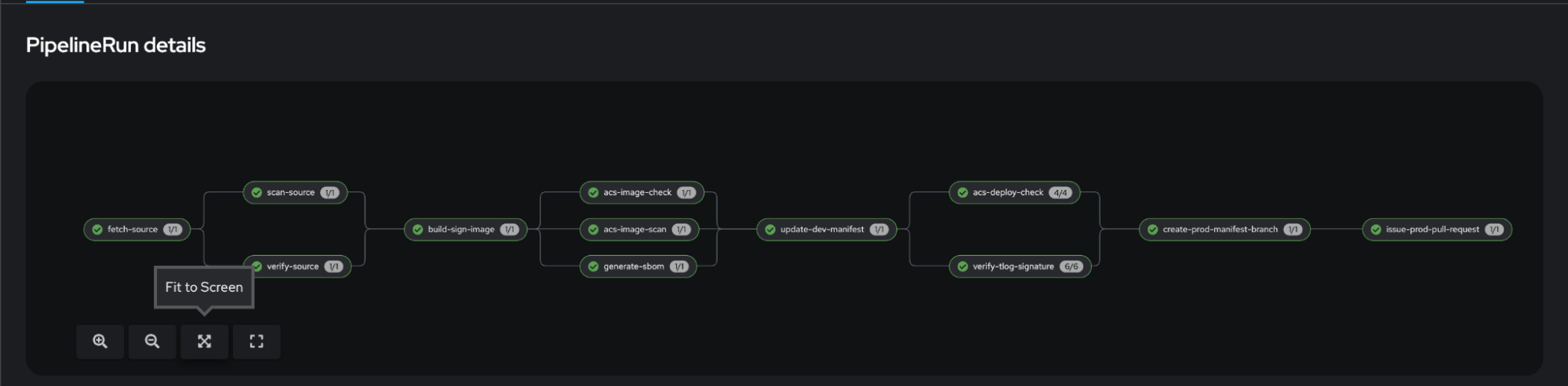
Figure 4: Sample Pipelinerun
Image security policies allow your organizations to define guidelines for image sources, access controls, and vulnerability scanning. Only trusted and verified images can be deployed, reducing the risk of compromised or vulnerable images.
Tekton Chain, integrated with Red Hat OpenShift Pipelines, enables your organization to establish a more secure supply chain for container images. It allows developers to sign images using Cosign, to help prove authenticity and integrity. This cryptographic signing process verifies that the images have not been tampered with.
Red Hat Advanced Cluster Security
Red Hat Advanced Cluster Security for Kubernetes policy can further enhance security. This policy verifies the signatures of container images before deployment, allowing only images with valid and trusted signatures.
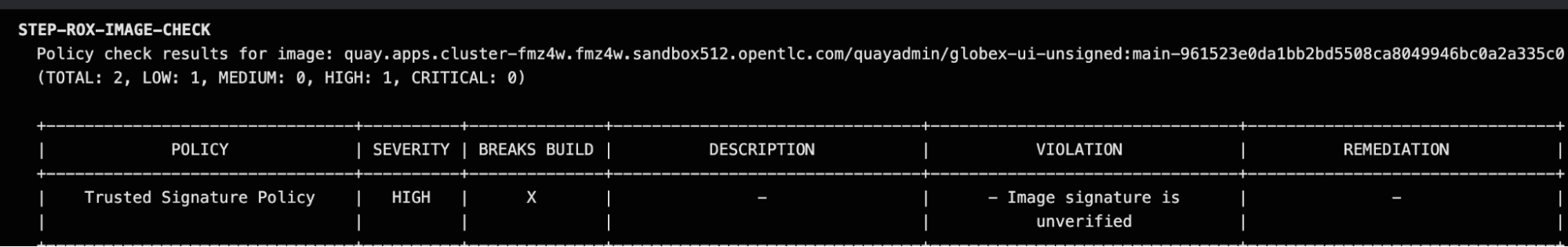
Figure 5: Red Hat Advanced Cluster Security Policy preventing unsigned image
By implementing image security policies, leveraging Tekton Chain with Cosign, and incorporating Red Hat Advanced Cluster Security, your organization can establish a robust and security-focused image deployment process in Red Hat OpenShift. These measures help protect against tampered or unauthorized images, providing confidence in the integrity and authenticity of containerized applications.
Continuous security scanning and remediation
Red Hat Advanced Cluster Security is an exceptional tool that can significantly benefit organizations with containerized environments in Red Hat OpenShift. Its continuous monitoring and automated remediation features make it an indispensable addition to the CI/CD process. The solution can easily integrate into the workflow, prioritizing security throughout the software development lifecycle.
With Red Hat Advanced Cluster Security integrated into the CI/CD pipeline, your organization can perform security scans and checks at every stage of the deployment process. This means that vulnerabilities, misconfigurations, and policy violations can be detected early, and developers can fix these issues before they reach production environments.
The solution can be easily integrated into CI/CD workflows by leveraging its APIs and CLI tools. Security scans and assessments can be triggered as part of the build process so that only security-enhanced and compliant artifacts progress through the pipeline. Any identified security issues can be automatically flagged, and the CI/CD pipeline can be halted or modified to address these issues promptly.
Red Hat Advanced Cluster Security also provides security insights and reports that help development teams assess the overall security posture of their applications. These insights can be used to improve the security practices within the CI/CD process, incorporating security considerations from the early stages of development.
By incorporating Red Hat Advanced Cluster Security into the CI/CD process, your organization can better enforce security policies, perform security scans, and automate remediation steps. This creates a more robust security culture and helps make security an integral part of the software development lifecycle in Red Hat OpenShift.
Conclusion
Implementing code and image security policies, image signing, and continuous security scanning with Red Hat OpenShift is essential to verify the authenticity and integrity of container images. By integrating these practices into your CI/CD process, you can identify and resolve vulnerabilities early in development, promoting trust throughout the software supply chain. With Red Hat OpenShift, you can more confidently adopt containerization while prioritizing the security and integrity of your software supply chain, safeguarding your applications, and protecting your data.
The Secure Supply Chain blog series aims to equip you with the knowledge and practical insights needed to better secure your containerized applications using Red Hat solutions. Stay tuned for our upcoming articles, where we will dive deeper into each aspect, providing comprehensive guidance and actionable steps to enhance your supply chain security.
References
執筆者紹介
As a seasoned technology professional and Team Lead for the APAC content development team, my role is dedicated to optimizing sales and marketing efforts for Red Hat products. I excel in crafting detailed, comprehensive demos that illuminate the unique selling propositions of our product range, addressing both technical and non-technical audiences. In addition, I work hand-in-hand with our sales and marketing teams to produce engaging marketing materials that align with current market trends and customer needs, ensuring our messaging strikes a chord with our target demographic. With a strong foundation in Red Hat technologies and a knack for translating complex technical features into relatable benefits, my work plays a pivotal role in supporting the sales process, boosting brand affinity, and ultimately driving the market presence of Red Hat products.
I started at Red Hat in 2021 as a Senior Architect and currently responsible for delivering sales demos using the Red Hat product set on our demo platform demo.redhat.com
Mitesh is a dedicated professional who began his career at Red Hat as an Instructor, laying the foundation for his journey with the company. Since joining in 2018, he has continually demonstrated his passion for technology and his commitment to excellence. Mitesh's primary focus has been enabling partners to effectively utilize Red Hat's Ansible Automation Platform and OpenShift products, showcasing his deep expertise in these technologies.
Currently serving as a content developer, Mitesh plays a pivotal role in creating demos for the Sales team, specifically focusing on Ansible Automation Platform and OpenShift. With his extensive knowledge and experience, he crafts engaging and impactful demonstrations that effectively highlight the value and capabilities of these products. Recently, Mitesh made significant contributions by developing a demo that emphasizes the importance of a Secure Supply Chain, improving the integrity and security of software throughout its lifecycle. Additionally, he actively works on Red Hat's latest offerings, including Event-Driven Ansible and Ansible Lightspeed, which aim to revolutionize automation and enhance operational efficiency.
Ritesh Shah is a Principal Architect with the Red Hat Portfolio Technology Platform team and focuses on creating and using next-generation platforms, including artificial intelligence/machine learning (AI/ML) workloads, application modernization and deployment, Disaster Recovery and Business Continuity as well as software-defined data storage.
Ritesh is an advocate for open source technologies and products, focusing on modern platform architecture and design for critical business needs. He is passionate about next-generation platforms and how application teams, including data scientists, can use open source technologies to their advantage. Ritesh has vast experience working with and helping enterprises succeed with open source technologies.
類似検索
さらに強化され、すぐに使用でき、コストがかからない:コンテナセキュリティの進化
Red Hat Universal Base Image の (再) 紹介
Collaboration In Product Security | Compiler
Keeping Track Of Vulnerabilities With CVEs | Compiler
チャンネル別に見る
自動化
テクノロジー、チームおよび環境に関する IT 自動化の最新情報
AI (人工知能)
お客様が AI ワークロードをどこでも自由に実行することを可能にするプラットフォームについてのアップデート
オープン・ハイブリッドクラウド
ハイブリッドクラウドで柔軟に未来を築く方法をご確認ください。
セキュリティ
環境やテクノロジー全体に及ぶリスクを軽減する方法に関する最新情報
エッジコンピューティング
エッジでの運用を単純化するプラットフォームのアップデート
インフラストラクチャ
世界有数のエンタープライズ向け Linux プラットフォームの最新情報
アプリケーション
アプリケーションの最も困難な課題に対する Red Hat ソリューションの詳細
仮想化
オンプレミスまたは複数クラウドでのワークロードに対応するエンタープライズ仮想化の将来についてご覧ください



