A substantial Red Hat Virtualization (RHV) deployment in your data centers makes manual virtual machine (VM) creation inefficient. The bigger the RHV deployment is, the more essential an automation method to create VMs becomes.
In this series, I show you how to design and automate VM deployments by using Ansible. In addition, I provide two sample Ansible playbooks to help you get going. It's a lot of information, but I separated the article into three parts that are all available here on Enable Sysadmin. Part one (this article) covers the basic goals, design, and assumptions. Part two covers the automation process. Part three provides you with the two Ansible playbooks, as well as some troubleshooting tips.
Here in part one, I cover some fundamental design concepts and the goals for the automation project. These concepts include assumptions about available tools, software versions, etc. I also examine the environment within which you will execute your automation tasks.
Design
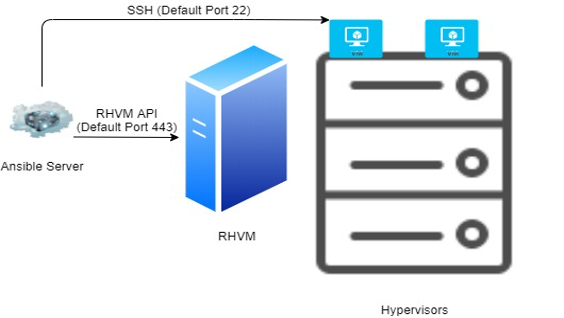
A single management point to automate VM creation simplifies the automation process. This design makes use of one Ansible server to automate two aspects of the deployment:
- VM creation using the RHVM API
- VM post configuration using SSH
This design achieves the following results:
- A secured automation chain using encrypted protocols, a different RHVM administrator username from the default admin username, and Ansible Vault to secure the passwords used in the automation process.
- A simple and manageable automation chain.
Assumptions
For simplicity, this article uses the following assumptions:
- Red Hat Virtualization (RHV) version 4.3.
- Ansible version 2.9 and the required packages are downloaded from the open-source upstream. Ansible Tower makes the automation process easier.
- CentOS 7.x hosts the Ansible server.
- A version control system, such as Git, is in place.
- The automation chain uses templates with the
cloud-initpackage pre-installed. - The VMs to be deployed are RHEL-based.
Note: the configuration of RHV, Ansible, Ansible Tower, CentOS, and Git are outside the scope of this article.
The post configuration tasks are examples. The specific tasks needed depend on the intended use of the VM itself. Modify the playbooks provided in part three to suit your needs.
Environment preparations
There are several aspects of Ansible-based deployments to configure before actually beginning the process. These aspects include preparing both RHV and Ansible for automated VM deployments.
Red Hat Virtualization
Few configurations are needed to set up the automation chain. It is a good practice to create a specific RHV administrator account rather than using the default local admin user.
The method for creating a new user with VM creation privileges depends on whether the Red Hat Virtualization Manager (RHVM) uses a central identity management system (i.e., IDM, Free IPA, or Active Directory) or local users.
Create a new local user (userame=ansible-user) with administrator privileges in RHVM by following the steps below.
Create the user account
First, connect to RHVM OS as a privileged user.
Next, use ovirt to create an ansible-user user account.
# ovirt-aaa-jdbc-tool user add ansible-user \
--attribute=firstName=Ansible\
--attribute=lastName=UserFinally, reset the password (in this example the password is redhat).
# ovirt-aaa-jdbc-tool user password-reset ansible-user --password=pass:redhatConfigure the account privileges
Now connect to RHVM and configure the new account's privileges.
First, log in to the RHVM GUI as a user with administrative privileges, and then move to Administration → Users.
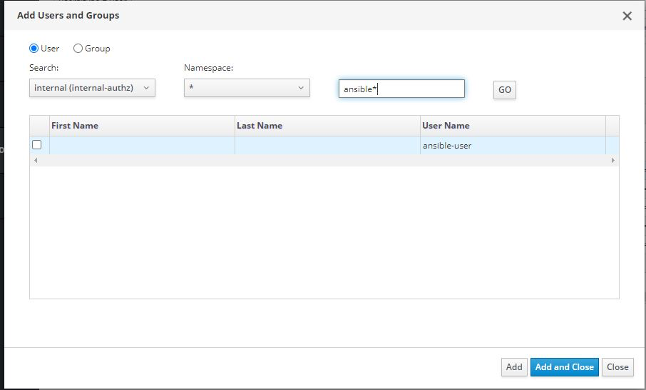
Select Add from the menu on the right.

Next, in the search box, type ansible*. The newly-created user ansible* is displayed. Select Add and Close. The user is listed with the other user accounts.
To configure user privileges, double-click on the ansible-user user account.
Finally, in the new window, select the Permissions tab, and then choose Add System Permissions.

Select the proper permission, which in this case, is VMCreator.
Note: Check this link for the full built-in roles in RHV.
Ansible server
The Ansible server is a Centos 7.x-based server, with Python and pip installed.
Note: Python 2.7 and python2-pip are used in this article. However, Python 3.6 and python36-pip can be used. Upgrading Python is out of the scope of this article.
Use the following process to set up the Ansible server:
Install Ansible, Jinja2, and ovirt-engine-sdk-python by using pip.
# pip install ansible Jinja2 ovirt-engine-sdk-pythonIf you are using pip behind a proxy server, you may need to use the settings below.
# pip --proxy [user:passwd]proxy.server:port install ansible Jinja2 ovirt-engine-sdk-pythonThis list displays the minimum versions required.
ansible==2.9.9
Jinja2==2.11.2
ovirt-engine-sdk-python==4.4.3Wrap up
At this point, the automated deployment environment is set up. You have the appropriate versions of CentOS, Ansible, Python, pip, and other software. You also have an administrator account in RHV specific to this project. Most important, you have a list of goals and expectations for what your new deployment process provides.
In the next article, I build on this configuration to provide flexible and efficient automation. Remember that part three includes two sample Ansible playbooks, too.
Continue with this series
Automate VM deployment with Ansible: Automation (Part 2)
Automate VM deployment with Ansible: The playbooks (Part 3)
References
Documentation for Red Hat Virtualization 4.3
[ A free course for you: Virtualization and Infrastructure Migration Technical Overview. ]
About the author
I am Ashraf Hassan, originally from Egypt, but currently, I am living in the Netherlands
I started my career in 1998 in the telecom industry, specifically the value-added services.
Although my official studies were in the area of telecommunications, I was always attracted to system administration and scripting. I started to sharpen these skills in 2008, during my free time, I like to test new tips and tricks using my home lab.
Working as a senior designer enriched my skills further.
In 2016 I decided to start the journey to be an “RHCA” which I accomplished in 2019, but as IT is a fast-changing domain, I need to keep studying, testing and learning.
In 2019 I joined Red Hat Accelerators once they expanded the program to include Europe; being a member of highly skilled technical experts helped me further.
Please feel free to contact me (info@free-snippets.com) regarding my posts or questions that can pop up related to any of Red Hat Products.
More like this
Streamlining Red Hat OpenShift multicluster management with Red Hat Ansible Automation Platform
Red Hat partner ecosystem: A year of expanding choice for virtualized workloads on Red Hat OpenShift Virtualization
Technically Speaking | Taming AI agents with observability
You Can't Automate Buy-In | Code Comments
Browse by channel
Automation
The latest on IT automation for tech, teams, and environments
Artificial intelligence
Updates on the platforms that free customers to run AI workloads anywhere
Open hybrid cloud
Explore how we build a more flexible future with hybrid cloud
Security
The latest on how we reduce risks across environments and technologies
Edge computing
Updates on the platforms that simplify operations at the edge
Infrastructure
The latest on the world’s leading enterprise Linux platform
Applications
Inside our solutions to the toughest application challenges
Virtualization
The future of enterprise virtualization for your workloads on-premise or across clouds
