Having a grasp of common architectural patterns is essential to designing software architecture at scale. Using them saves not only time but also ensures a reliable implementation of your design. There’s no need to reinvent the wheel when there’s an architectural pattern available that applies to an architecture you’re developing.
The following is a brief overview of the Event Sourcing architectural pattern.
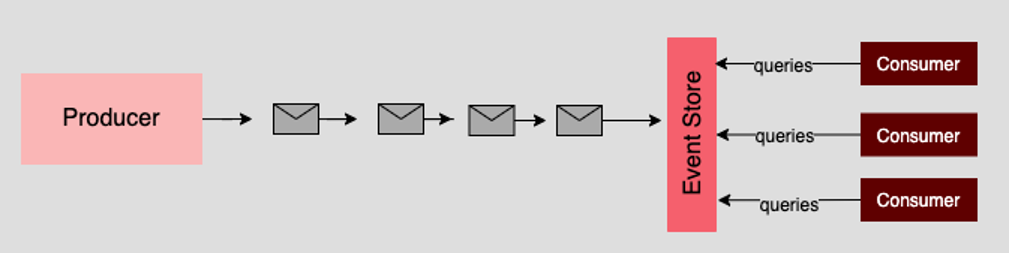
Understanding the Event Sourcing pattern
The Event Sourcing pattern involves sending a continuous stream of messages to an authoritative storage target. Each message describes an event in the system. Examples include: A write to the database, request to a web server, or logging activity from within an application. Services and applications then query the event store for interesting events in a way that is particular to the purpose of the given service or application.
Pros
- Great for fail-safety. If the downstream source fails, its data can be reconstituted from the event store.
- Extremely flexible. Any type of message can be stored. Any consumer can access the event store as long as appropriate access rights are granted.
- Excellent for real-time data reporting, especially when used with an event-driven message broker such as Kafka.
Cons
- Requires an extremely efficient network infrastructure given the inherent time sensitivity of the pattern and the susceptibility to potential latency issues.
- Requires a reliable way to control message formats, for example, using a schema registry.
- Different events will contain different payloads. There needs to be a single source of truth for defining and determining message formats for a particular event.
Putting it all together
Event Sourcing is gaining popularity as more applications need real-time data delivered in an asynchronous yet ordered manner, for example, ride-share applications. Also, Event Sourcing is gaining wide acceptance as a way to consume and manage applications’ log data at web-scale. As mentioned above, an event source can serve as a common point of truth for applications regardless of how the given application intends to process the data.
About the author
Bob Reselman is a nationally known software developer, system architect, industry analyst, and technical writer/journalist. Over a career that spans 30 years, Bob has worked for companies such as Gateway, Cap Gemini, The Los Angeles Weekly, Edmunds.com and the Academy of Recording Arts and Sciences, to name a few. He has held roles with significant responsibility, including but not limited to, Platform Architect (Consumer) at Gateway, Principal Consultant with Cap Gemini and CTO at the international trade finance company, ItFex.
More like this
Red Hat Learning Subscription Course reimagines virtual training
Red Hat Learning Subscription Course: Skills for the future
How Should We Handle Failure? | Compiler
The Legend Of Hadoop | Compiler: Legacies
Browse by channel
Automation
The latest on IT automation for tech, teams, and environments
Artificial intelligence
Updates on the platforms that free customers to run AI workloads anywhere
Open hybrid cloud
Explore how we build a more flexible future with hybrid cloud
Security
The latest on how we reduce risks across environments and technologies
Edge computing
Updates on the platforms that simplify operations at the edge
Infrastructure
The latest on the world’s leading enterprise Linux platform
Applications
Inside our solutions to the toughest application challenges
Virtualization
The future of enterprise virtualization for your workloads on-premise or across clouds
