Ansible's dynamic inventory options help keep environments up to date by populating changes into automation controller. Integrating different hypervisors as an inventory source helps provide a dynamic way of managing a virtual infrastructure.
By harnessing the hypervisor's ability to organize virtual machines (VMs) by attributes, virtual hardware, and datacenter structure, an automation controller can benefit by ingesting these properties to be used in groups or as host variables.
[ Ansible vs. Red Hat Ansible Automation Platform: Do you know the difference? ]
Use an existing organizational structure
When using a hypervisor as a source, dynamic inventorying removes the need for administrators to maintain multiple sets of metadata.
Ansible administrators can run playbooks quickly and easily against VMs on specific clusters, VLANs, or datacenters.
The benefits of this configuration include:
- Providing a dynamic inventory of virtual hosts with the chosen hypervisor as a source
- Enabling Ansible inventory host groups to be defined based on VM attributes or properties
- Allowing inventory hosts to define VM attributes as Ansible host variables
For example, you can configure a link between Ansible and vCenter by following the steps below.
[ Learn more about integrations between Ansible and VMware infrastructure. ]
Create a local hypervisor account
It is best to create an individual account for Ansible to pull information from vCenter.
Create an account in the vsphere.local domain and grant it read-only permissions on the virtual infrastructure to be included in an inventory. Permissions may be granted at any point in the hierarchy (datacenter, cluster, or folder levels) and populated downward.
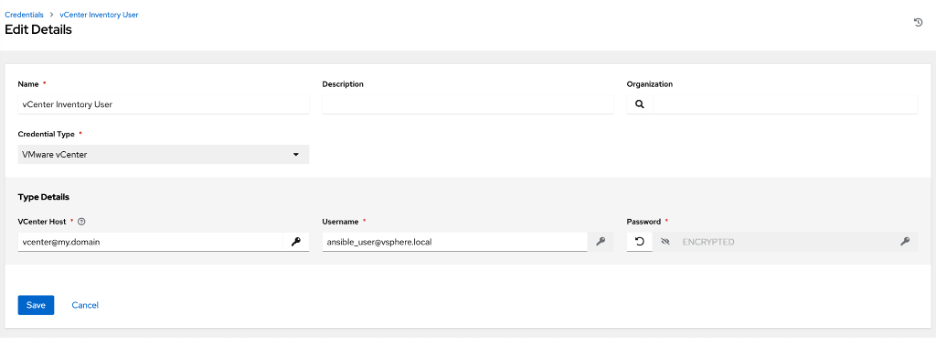
Create an Ansible credential
In automation controller, create a credential for the user you created in the previous step.
For this example, define the Credential Type as "VMware vCenter," and the resulting fields should be populated with the vCenter URL, user account, and password. Note that the username field should include the domain information, for example, username@vsphere.local.
Create an automation execution environment and load it to private automation hub
It is helpful to build an execution environment specifically for this integration. How to build Ansible execution environment images for unconnected environments provides a great walkthrough on creating an execution environment and pushing it into a private automation hub.
When building the execution environment, create the following files with respective contents to allow it to perform the vCenter translations. Define these files in the execution-environment.yml.
For Galaxy requirements.yml:
---
collections:
- name: community.vmware
For Python requirements.txt:
git+https://github.com/vmware/vsphere-automation-sdk-python.git
setuptools
pyVmomi
Once you build the execution environment image, load it into a private automation hub to make it available to any automation controller that needs it.
[ Practice writing Ansible playbooks in this hands-on interactive lab. ]
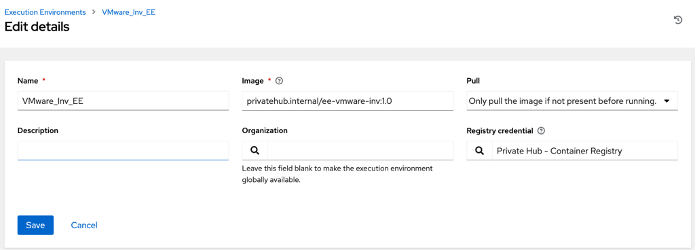
Configure the execution environment in automation controller
- Create a credential that can access the private automation hub.
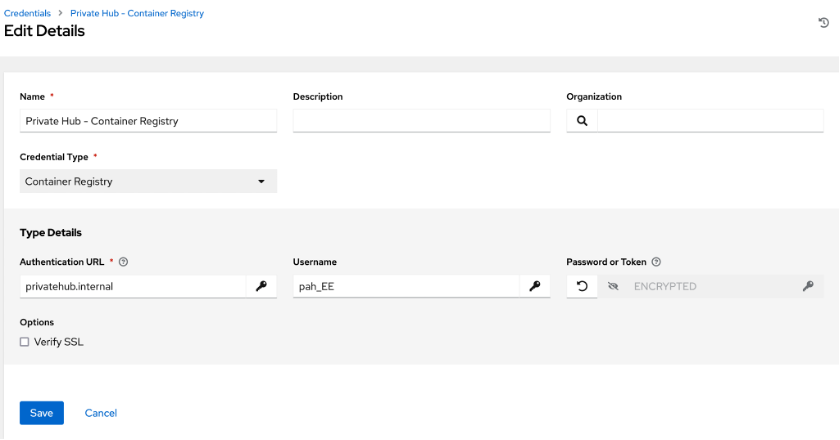
- Navigate to Execution Environments and select Add.
- Define a name, description, and organization.
- Input the full path of the execution environment container image, for example, privatehub.internal/ee-vmware:1.0.
- Select a pull option and the credential from step 1 with access to the private automation hub.
Configure the dynamic inventory
- Create a new inventory under Inventories. Define a name, organization, and any desired labels or variables.
- Save the inventory.
- Navigate to the Sources tab of this newly created inventory and Add a source.
- Define a name and execution environment from the previous section.
- Select VMware vCenter as the Credential Type.
- Populate the Source details to include the Ansible credential you created before.
- Source variables are where most of the configuration happens.
- I recommend copying the section from the documentation and discovering which properties provide the most value as Ansible host vars.
- I recommend using hostnames ["config.name"] to define the virtual machine name as the Ansible inventory host entry.
- The keyed_groups variable will use VM attributes to define Ansible inventory host groups.
- Use the filters and resources to tune the ingestion of sources from vCenter further.
Here's an example:
hostnames: ["config.name"]
filters:
- runtime.powerState == "poweredOn"
resources:
- datacenter:
- Datacenter1
resources:
- folder:
- Redhat_vms
- Application_vms

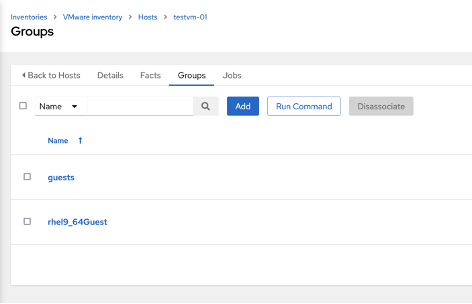
The power of this integration comes with good organization and identification of attributes to group VMs. For example, groups can be matched with attributes such as VM guest type, VLAN, and custom attributes. Below is an example of a VM pulled from vCenter with a simple configuration. Notice the Variables populated in the Host details. The group reflects the Guest OS value in the hypervisor.
Here are the Host details:

And the Groups details:
[ Learn best practices for implementing automation across your organization. Download The automation architect's handbook. ]
Enrich and use
For environments utilizing a virtual infrastructure, using the virtualization source is a great way to include systems in the scope of Ansible. Additions to a virtual environment will be pulled in upon sync, so no system gets forgotten. Utilizing Ansible's Smart Inventory features can allow this metadata to be shared across inventories. Attributes and metadata pulled from the VM level can enrich playbook runs with ease.
About the author
Nick is a Systems Engineer constantly striving to simplify his work life. When work is less stressful, there is more time for the better things in life, like gardening.
More like this
Increasing hardware costs? Get more from your VM estate with Red Hat OpenShift Virtualization
AIOps and Ansible Automation Platform: Where AI intelligence meets trusted execution
Technically Speaking | Taming AI agents with observability
You Can't Automate Buy-In | Code Comments
Browse by channel
Automation
The latest on IT automation for tech, teams, and environments
Artificial intelligence
Updates on the platforms that free customers to run AI workloads anywhere
Open hybrid cloud
Explore how we build a more flexible future with hybrid cloud
Security
The latest on how we reduce risks across environments and technologies
Edge computing
Updates on the platforms that simplify operations at the edge
Infrastructure
The latest on the world’s leading enterprise Linux platform
Applications
Inside our solutions to the toughest application challenges
Virtualization
The future of enterprise virtualization for your workloads on-premise or across clouds
