There is a fundamental tension between using AI and the cloud while adhering to strict privacy mandates like digital sovereignty and sovereign AI. Encryption of data at rest and in transit is increasingly common, but traditional computing leaves data exposed in system memory during processing—known as data in use—which puts it at risk.
To address this challenge, confidential computing has been developed, using hardware-based, attested Trusted Execution Environments (TEEs) protecting data confidentiality, data integrity, and code integrity while data is in use. This enables protected collaboration and the use of regulated datasets for AI.
In this blog post, co-written by Red Hat and Duality, we present an end-to-end confidential computing architecture. We build on a hardened infrastructure Red Hat provides (such as Red Hat OpenShift confidential containers) combined with Duality Technologies. The result is a protected collaboration platform for policy management, governance, and running workloads, enabling mission-critical use cases such as protected on-premise model inference and cross-agency collaboration.
Learn more about confidential computing.
Duality data collaboration platform
Duality Technologies makes use of Red Hat's confidential computing infrastructure to add an additional layer of data privacy, further strengthening the overall security posture for analytics workloads.
Duality platform is a protected platform that can be deployed anywhere, including in the cloud and on-premise. The platform facilitates collaboration between various parties so they can run any workload, using any data, while protecting data and models in use.
This end-to-end control across the data and execution lifecycle is what enables trust-by-design and sovereign AI operations.
The platform is built on 3 layers:
- Collaboration management: Enterprise-grade tools for managing the full collaboration lifecycle, including setup, data management, governance, and policy enforcement.
- Computation: Scalable engines for running a wide range of workloads including model training, inference, fine tuning, and analytics.
- Privacy preserving technologies: A foundational privacy-enhancing technology (PET) layer incorporating fully homomorphic encryption (FHE), differential privacy (DP), federated learning (FL) and TEE.
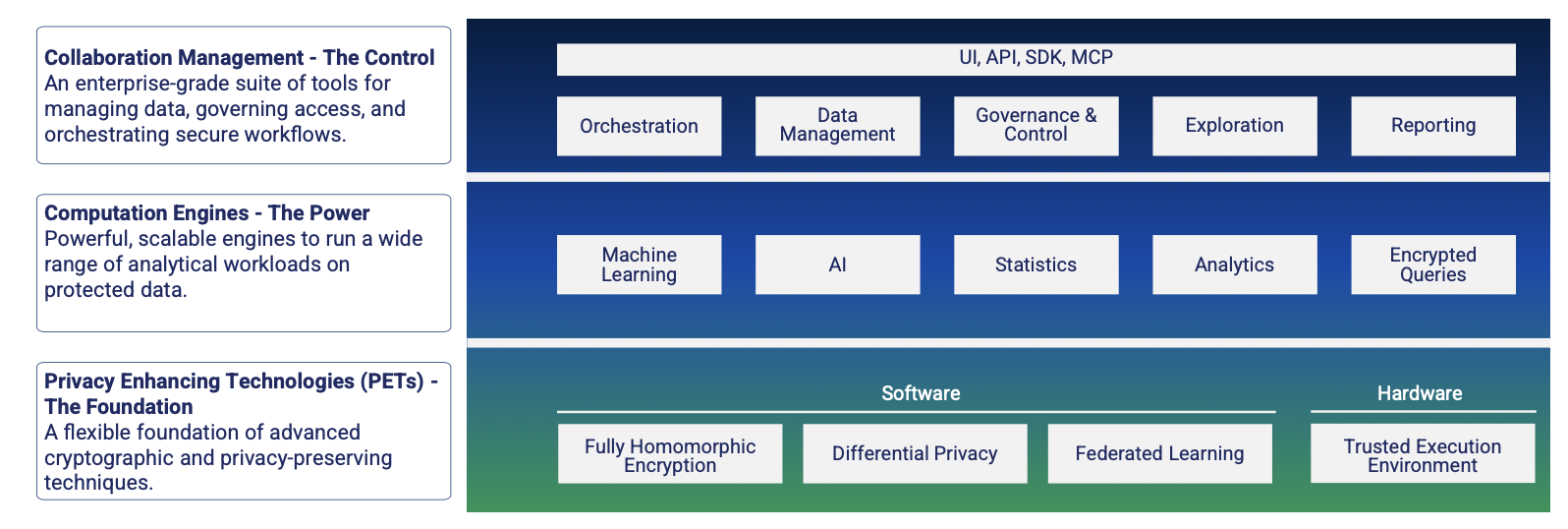
The Duality platform
Unlike many general-purpose tools that add security as an afterthought, the Duality platform was architected from the ground up specifically to enable protected collaboration.
Here are some of the benefits the Duality platform provides:
Abstraction of complex infrastructure
The Duality platform handles the complexity of the underlying infrastructure, allowing users to focus solely on their workload.
- Simplified deployment: Users simply deploy Duality without needing to manage attestation servers, key exchanges, or low-level TEE configuration.
- Data and model protection: The platform helps protect both the data and the models throughout the execution lifecycle.
Robust authentication and authorization
Duality manages user access and integrates with common identity management protocols, so only authorized parties can interact with the platform.
Data owners retain full control over their assets via a robust policy layer. They can define precisely who accesses the data, when and at what frequency access is granted, and the rules and thresholds applied to the output data to help prevent leakage.
Comprehensive monitoring and auditing
The platform also provides tools for compliance and operational troubleshooting right out of the box. This includes detailed auditing and monitoring reports that satisfy regulatory requirements and simplify diagnostics.
Centralized data management and harmonization
In collaborative environments, data harmonization is crucial. Duality prepares data for shared computation, facilitating the alignment of data schemas, so multiple users can run their workloads on a shared and agreed-upon structure. It also provides tools for data management and harmonization before the workload execution begins.
Integration of multiple privacy technologies
Duality also allows users to combine confidential computing with other advanced privacy-preserving technologies for even higher levels of data protection. For example, in a federated learning setup, the Duality platform can combine federated learning with confidential computing so:
- Computation occurs locally near the data source.
- Intermediate weights, which are sent to a global server, are protected and processed inside the secure enclave (TEE), safeguarding them from the server operator.

Augmenting confidential computing
Flexible interfaces: UI, API, SDK, and MCP
Duality meets the user where they are, offering multiple ways to interact with the system:
- Intuitive user interface (UI): For business users and administrators to manage policies, view audits, and collaborate visually.
- Application programming interface (API) and software development kit (SDK): For data scientists and developers to integrate secure computations directly into their existing pipelines (such as Python notebooks).
- Model Context Protocol (MCP): Enabling modern AI agents and large language models (LLMs) to interact with the platform, paving the way for autonomous sovereign AI workflows.
By combining these capabilities, Duality offers an end-to-end solution. Whether the goal is training a machine learning (ML) model, running complex analytics, or executing SQL queries, the platform handles the orchestration of the Red Hat confidential containers in the background, so data remains protected throughout the entire lifecycle of the computation.
Use case: Protected model inference in the cloud
Here we'll show you how the user's prompt (sensitive input) is encrypted at the client-side and only decrypted within the confidential container (TEE) in the cloud. This enables cloud execution of sensitive workloads while protecting the input data from the cloud provider and external threats.
Following are the main steps in the demo:
- Users running on-prem generate a prompt.
- Prompt is encrypted to Advanced Encryption Standard (AES) by Duality on the data owner side while the key is also encrypted, using the public key generated in the confidential computing environment.
- The encrypted prompt and the encrypted key are sent to the Duality node running in the cloud inside the confidential container.
- The prompt is executed within the confidential container.
- The result is encrypted and sent back to the user.
- The result is decrypted by Duality.
The following diagrams show how the Duality solution and confidential containers work together:

Connecting OpenShift confidential containers with the Duality solution
Here are some of the Duality features that compliment OpenShift confidential containers.
Collaboration software
Duality provides a Collaboration Manager used by administrators to set up and oversee collaborations. This manager is responsible for creating projects and efficiently configuring the collaboration network. While the Collaboration Manager handles project setup, configuration, and participant assignment, it has no access to any data or computations.
Each participant gets a role such as:
- Asset Owner who contributes assets to the analysis
- Initiator who initiates a computation
- Analyzing Party who receives the computation result
- Compute to manage the central computation / aggregation
Code verification
In addition to the Red Hat-based attestation process, the Duality platform verifies that the specific code agreed upon by all parties is exactly what executes within the confidential containers.
Key management
The Duality platform manages the protected data flow between the Analyzing Party, Asset Owners, and Compute and Enclave (TEE), verifying all assets, queries, and results are encrypted, and that the results are received and decrypted by the Analyzing Party.
The data flow is as follows:
- Analyzing Party and Asset Owners complete the secret sharing protocol including generation and sharing of the AES key
- Asset Owners encrypt assets with their AES key and share them with the Enclave
- TEE decrypts assets with the Asset Owner’s AES keys
- TEE runs the computation using the decrypted workloads and other assets
- TEE encrypts the results (AES) and sends them to the Analyzing Party
- The Analyzing Party decrypts the results
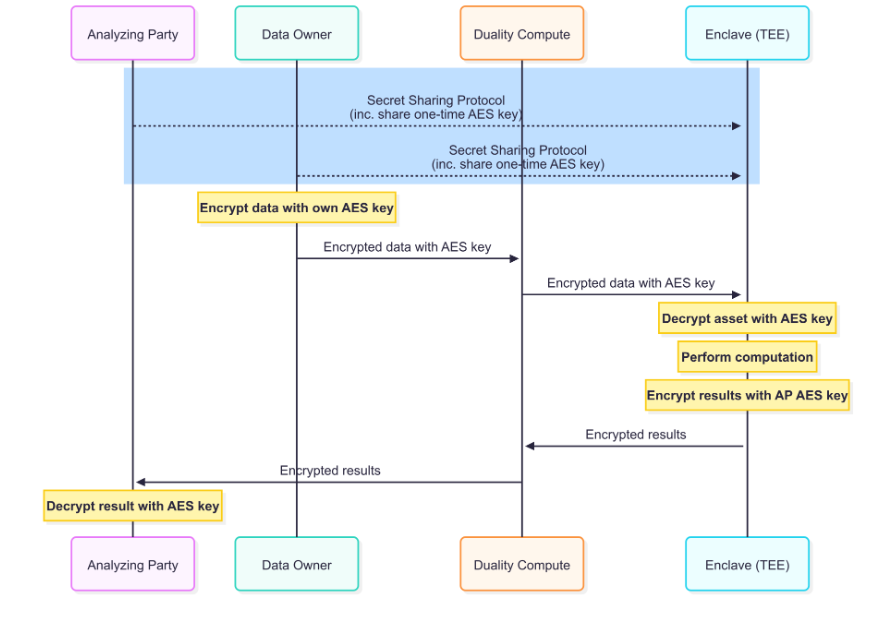
User data flow for protected model inference
Duality uses Red Hat’s existing Key Broker Service (KBS) within the Trustee framework to facilitate secret sharing between the data owner and the confidential VM (CVM).
The process follows a specific security handshake:
- Attestation proof: The CVM presents these secrets to the data owner as verifiable proof of successful attestation.
- PQC negotiation: Once this proof is validated, the data owner consents to participate in a post-quantum cryptography (PQC) key exchange.
- Running the workload: After the PQC exchange is approved, the data owner encrypts the sensitive information and proceeds with the requested workloads.
Note that in the current model, only one party needs to complete the attestation process during a collaboration. Duality is developing future enhancements to support multiparty attestation, allowing each asset owner to run the attestation process as well.
Data and model management
Users with the Asset Owner role can register data and models through the UI and add them to their projects. The platform makes sure all assets remain encrypted during transfer to confidential containers. Additionally, users can use pre-processing tools to prepare data before launching workloads, such as model training.
Governance
Duality Policies enable a full layer of governance for Asset Owners collaborating on AI projects within the Duality platform. It enables Asset Owners to control who can run computations on sensitive data, which workloads are permitted, and under what conditions. By default, all access to assets is denied. An analysis can only be performed when a policy explicitly grants permission.
This provides a secure-by-design environment where Asset Owners maintain full control over their data use at all times. An additional capability introduced with policies is Workload Signing, which verifies the computation executed at session time is the same computation approved by the Asset Owner. This is done by validating the workload's integrity using hashes, preventing unauthorized changes or tampering.
Auditing
The Duality platform comes with a built-in logging system that captures every operation and session for troubleshooting and auditing purposes. This mechanism runs on every node where Duality is deployed, including the Collaboration Manager, Hub, and Participant nodes. By default, each participant can only view their own logs, and the Duality platform stores these logs locally to protect sensitive data.
The Duality platform comes with the built-in ELK stack (Elasticsearch, Logstash and Kibana), which provides a flexible mechanism for storing and analyzing logs. Customers who already manage an in-house Elasticsearch database can point the Duality logs to their Elasticsearch server during installation.
Final thoughts
Here we've presented an architecture combining Red Hat and Duality Technologies to establish a protected environment through end-to-end confidential computing. While organizations typically protect data at rest and in transit, data in use often remains vulnerable. This joint solution addresses that gap.
製品トライアル
Red Hat OpenShift Container Platform | 製品トライアル
執筆者紹介
類似検索
Building a hardened, image-based foundation for AI agents
Using NVIDIA Aerial CUDA-Accelerated RAN on Red Hat OpenShift to accelerate development of AI-native 5G and 6G RAN solutions
Technically Speaking | Build a production-ready AI toolbox
Technically Speaking | Platform engineering for AI agents
チャンネル別に見る
自動化
テクノロジー、チームおよび環境に関する IT 自動化の最新情報
AI (人工知能)
お客様が AI ワークロードをどこでも自由に実行することを可能にするプラットフォームについてのアップデート
オープン・ハイブリッドクラウド
ハイブリッドクラウドで柔軟に未来を築く方法をご確認ください。
セキュリティ
環境やテクノロジー全体に及ぶリスクを軽減する方法に関する最新情報
エッジコンピューティング
エッジでの運用を単純化するプラットフォームのアップデート
インフラストラクチャ
世界有数のエンタープライズ向け Linux プラットフォームの最新情報
アプリケーション
アプリケーションの最も困難な課題に対する Red Hat ソリューションの詳細
仮想化
オンプレミスまたは複数クラウドでのワークロードに対応するエンタープライズ仮想化の将来についてご覧ください

