During a computer's boot process, you must transition from a firmware (UEFI or BIOS) process to loading a kernel and then finally to the user environment. When booting a POSIX system, you can choose to interrupt the boot process to adjust settings or even to log in using a chroot environment.
This is a useful troubleshooting and maintenance technique, but it's also the reason it's so important to utilize full disk encryption when installing your operating system. When a drive is encrypted, nothing on the drive is accessible without your passphrase, even from a preboot environment. As long as you have the passphrase to decrypt your drive, you can interrupt a Linux system's boot process and access the drive without booting into a full operating system (OS).
The GRUB screen
The hand-off from firmware to bootloader ends in the grand unified bootloader (GRUB) screen. GRUB is a text menu that allows you to select which OS and kernel version you want to boot into. By default, it assumes you want to boot to the latest version of Linux installed on the machine. However, it also allows you to modify how you want to boot the OS.
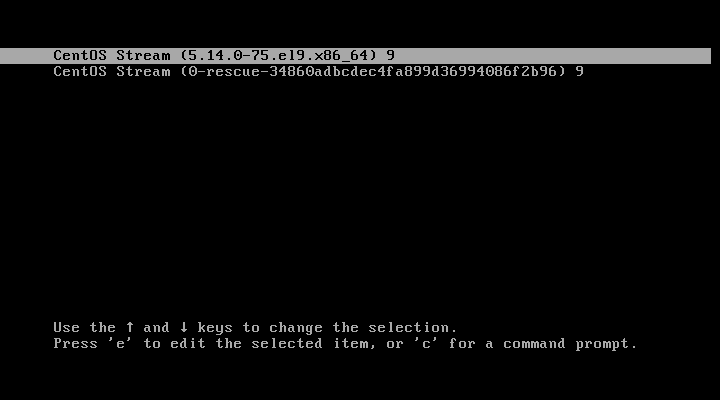
To prepare your computer to have its boot process interrupted, press e on your keyboard when you see the GRUB startup screen. This reveals the boot parameters assigned to the default menu selection.
load_video
set gfx_payload=keep
insmod gzio
linux ($root)/vmlinuz-x.y.z-aa.el9.x86_64 root=/dev/mapper/rhel-root ro resume=\
/dev/mapper/rhel-swap rd.lvm.lv=rhel/boot rd.lvm.lv=rhel/swap rhgb quiet
initrd ($root)/initramfs-x.y.z-aa.el9.x86_64.img $tuned_initrd
After the string quiet, add the parameter rd.break, and then press Ctrl+X to exit the parameters editor and continue booting. The rd.break parameter causes the initial RAM disk containing the parts of the Linux kernel required to boot to "break," in the same sense that a debugger places "breakpoints" in an application to pause its execution. The initial RAM disk (initrd) is likely located within the encrypted portion of your hard drive, so you must enter your passphrase before you can continue to boot.
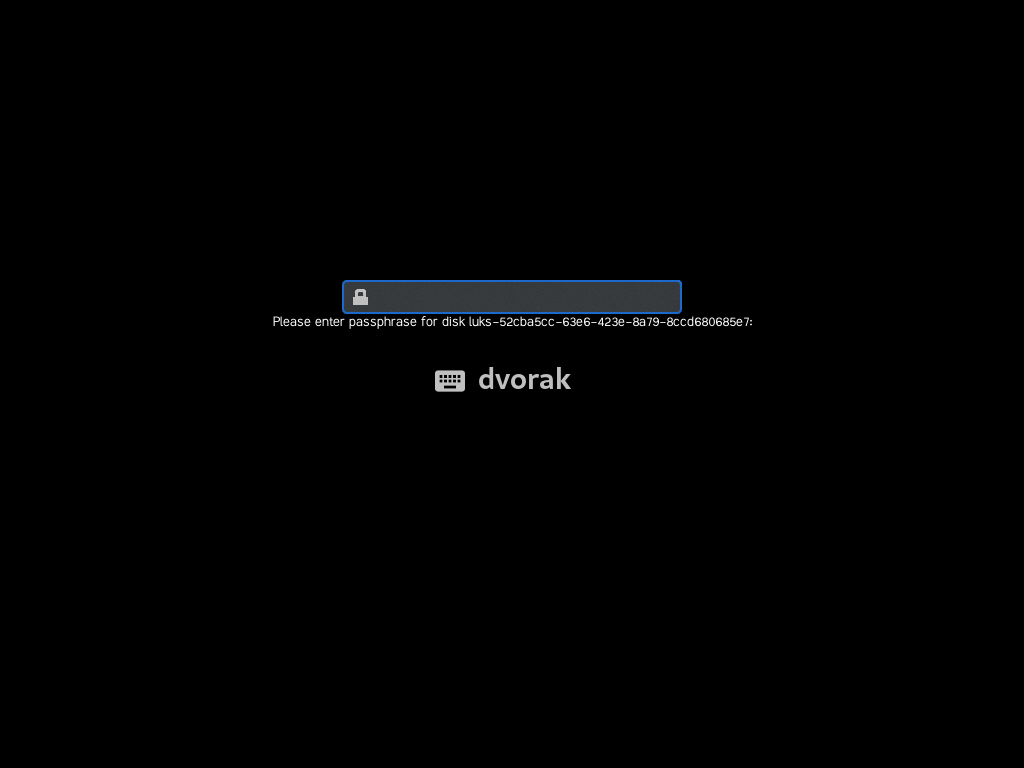
If your computer continues to boot without prompting you for a passphrase, then you have not activated full disk encryption.
[ Free download: Advanced Linux commands cheat sheet. ]
Enter maintenance mode
Because you've instructed the initrd to break, the boot process stops in an emergency maintenance mode. If you have nothing you need to do, you can press Ctrl+D to continue booting as normal. Otherwise, press Enter for a minimal but interactive shell.
Do disk repair
Once you're at a shell prompt, you're the root user of that machine. Your next actions depend entirely on what kind of maintenance you need to perform.
You might run a disk check on your drive using the xfs_repair or fsck command:
sh# xfs_repair /dev/sda1
Change your active environment with chroot
To recover a password, you might need to remount the drive (it's already mounted in read-only mode to /sysroot as part of the boot process). The remount,rw options mount a location on a drive with write permissions. This task can be extremely dangerous: You have full root privileges, no guardrails, and a writable drive. The less time you spend in this mode, the better, and you should use it only in true emergencies.
sh# mount -o remount,rw /sysroot
You must use the chroot command to make the remounted drive your active environment. This replaces your current / partition with /sysroot, which sets all paths to the ones you're used to when you log into a system.
For instance, before a chroot action:
sh# which sh
which: command not found
After a successful chroot:
sh# chroot /sysroot
sh# which sh
/usr/bin/sh
Perform maintenance
From here, you're mostly logged into the system. You can run commands, recover files, passwords, and perform whatever maintenance you may need to do. Some conveniences are lacking. For instance, there's no /proc or /sys mounted unless you mount them yourself (mount -t proc proc /proc, for instance). However, the point isn't to make this session a fully interactive multiuser experience. This is maintenance mode, and it's meant as a temporary environment for emergencies.
Continue booting
When you've finished maintenance, set a flag so that SELinux relabels the system as needed on the next boot. This step isn't always strictly necessary, depending on what kind of maintenance you've done, but it's not a bad idea given that you've likely made changes to the system. Once you've done that, exit the chroot environment and then exit the shell to continue booting:
sh# touch /.autorelabel
sh# exit
sh# exit
As your computer continues to boot, SELinux relabels the system as required.
Interrupting boot
The boot process isn't meant to be interrupted, and it's rarely necessary. In times of trouble, though, this is an important troubleshooting technique. Use it wisely, and use full disk encryption to ensure no interactive shell is available without decryption.
About the author
Seth Kenlon is a Linux geek, open source enthusiast, free culture advocate, and tabletop gamer. Between gigs in the film industry and the tech industry (not necessarily exclusive of one another), he likes to design games and hack on code (also not necessarily exclusive of one another).
More like this
Expiration of Secure Boot signing certificates in 2026
Planning your path forward from Amazon Linux 2: Why consistency is the ultimate upgrade
Operating System Management | Compiler
OS Wars_part 1 | Command Line Heroes
Browse by channel
Automation
The latest on IT automation for tech, teams, and environments
Artificial intelligence
Updates on the platforms that free customers to run AI workloads anywhere
Open hybrid cloud
Explore how we build a more flexible future with hybrid cloud
Security
The latest on how we reduce risks across environments and technologies
Edge computing
Updates on the platforms that simplify operations at the edge
Infrastructure
The latest on the world’s leading enterprise Linux platform
Applications
Inside our solutions to the toughest application challenges
Virtualization
The future of enterprise virtualization for your workloads on-premise or across clouds
