Security for any operating system is always a crucial pain point. Although Linux systems have various security measures built-in and optionally available, no operating system (OS) is truly secure. There are several methods required to keep your OS safe, but I don't discuss core security in this article. In this article, I discuss Pluggable Authentication Module (PAM) and how PAM helps provide enhanced security.
PAM provides a centralized authentication mechanism and provides a generic way for applications to implement support for authentication. It enables an application to call the PAM library, libpam, to perform all authentication tasks on its behalf and return a pass or fail response to the application.
[ You might also enjoy: Setting up multi-factor authentication on Linux systems ]
As a sysadmin, you can use PAM for dynamic authentication from the user to the application. It integrates a low-level authentication to a high-level API. PAM is pluggable because there are PAM modules for different types of authentication sources, such as Kerberos, SSSD, NIS, or local file systems. There are several use-cases for PAM, but here I will discuss the advantages and usages of PAM for system admins.
- PAM relies on common authentication schemas that can be used with a wide variety of applications .
- PAM provides significant flexibility and control over authentication for system administration.
- PAM is one of the most popular ways to enable sysadmins to set authentication policies.
In PAM, the /etc/pam.d directory holds all the files related to services. Take one example of a login program. In the /etc/pam.d directory, the name of the file which holds the login program is login. In this way, all files have name configurations. In PAM, every file has a standard format for its rules. You must follow the same format for creating authentication rules. You can refer to the pam.d man page, where all the syntax rules are well explained.
Password management example
The examples in this article are related to user password authentication in PAM. I first set a PAM rule for strong password quality so that if you try to set a weak password for a user, the system won't accept it. You can set a password policy such as password length should be greater than seven, and it must contain lower case, upper case, and special characters. You can also set a requirement for the number of digits in the password. Using these parameters, you can create a strong password for the user to strengthen authentication.
The file that holds the information about password quality is inside the /etc/security directory. In this directory, pwquality.conf is the configuration file for password quality limits.
There are some values that you can use for a quality password, and they are:
- difok: Indicates the number of characters of the new password that must not be present in the old password.
- minlen: Sets the minimum length of your new password.
- dcredit: Sets maximum and minimum digits in the new password. If you set the
-vevalue in this parameter, then it will use that value as a minimum number of digits in the password . - ucredit: Sets the maximum uppercase character in the password. If you use the
-vevalue, then it will use that value as the minimum uppercase character limit. - lcredit: Sets a lowercase character limit in the password. If the value is greater than 0, then it shows maximum values, but if it is used with
-veor less than 0, then it configures the minimum lowercase characters in a new password . - ocredit: Sets requirements for other characters. You can set maximum other characters by assigning values greater than 0. If values are less than 0, then it will be considered as the minimum ocredit value .
- dictcheck: Checks whether words of the password are from the cracklib dictionary. If a value is set to nonzero, then this option is enabled .
- usercheck: Helps to check whether a password contains a username in any form. If the value is not zero, then this option is enabled .
So these are some parameters that you can use to set a strong password. While assigning a password, if the requirement does not match, then it will prompt you with a clear error message.
In my example, I now need to set parameters for the password. Requirements like password length should be seven where minimum digit and uppercase character should be one. Other character values should be a minimum of one in the new password. So values will look like this:
minlen=7
dcredit=-1
ucredit=-1
ocredit=-1Here most of the values are set for the minimum. The minimum one is a requirement, so you have to use these parameters in the new password. There is no limit for maximum value. The minimum length of the password is seven characters, and these seven characters include digits and non-alphanumeric characters. You can set all these values inside the /etc/security/pwquality.conf file. You can directly put these values at the end of the file. For cross-checking whether the rules which you set are working or not, try to set a variety of different passwords for an account.
Here, minlength is seven, so if you put a password less than seven characters, it will prompt you with an error. If you didn't put a minimum of one digit, one uppercase letter, and other characters like @ or #, it will also prompt you with a specific error.
Errors will look like this:
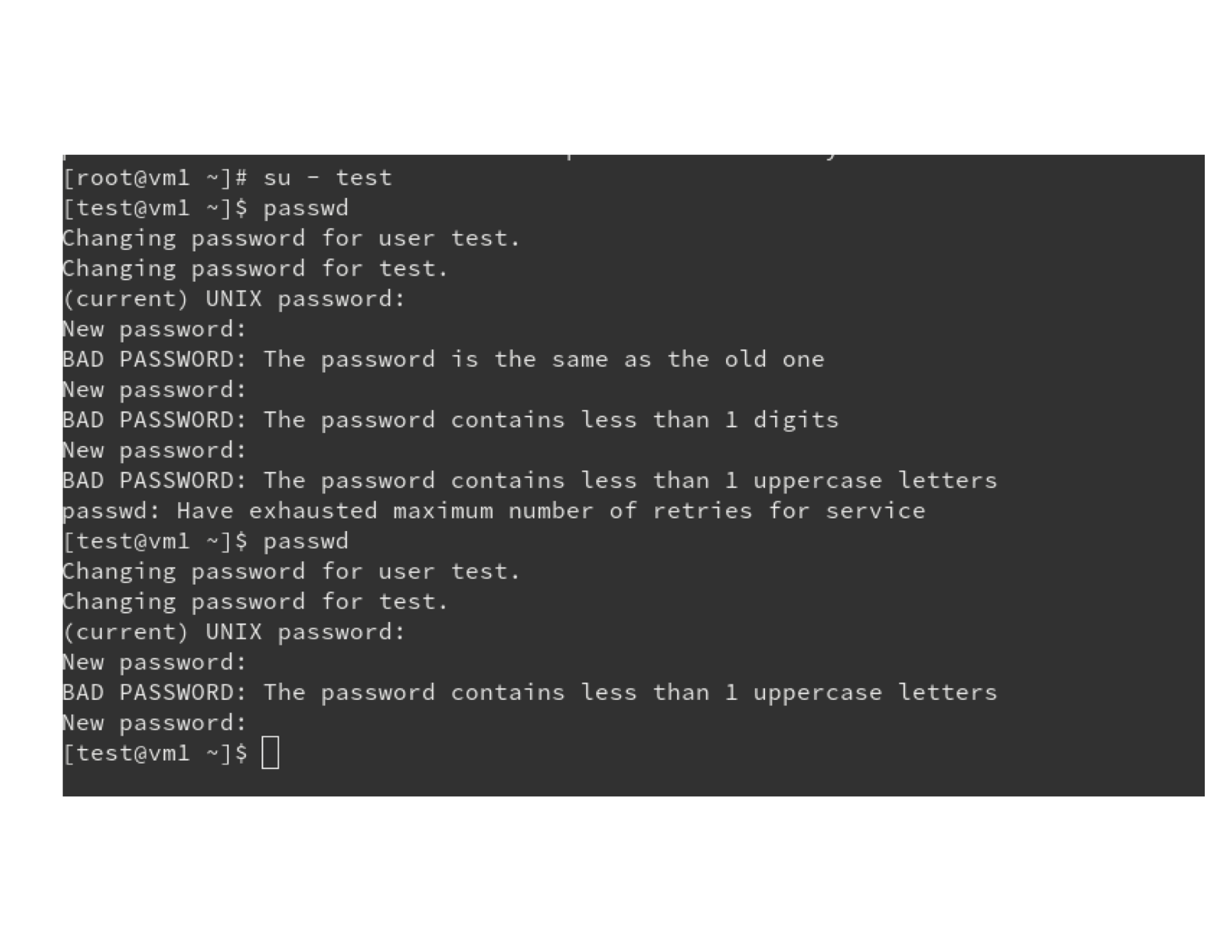
This is an example of how you can create restrictions for the passwords so they will be stronger. Using these PAM modules, you can customize your password quality to make your user accounts more secure. You can also deny access to any user on any machine using PAM. There are many different kinds of operations you can do with PAM.
Authconfig
Administrators can use authconfig for configuring PAM. It provides command-line tools as well as a graphical interface through the authconfig-gtk command. This command works in two modes:
- Update: Updates the PAM configuration files with options that you provide.
- Test: Prints the configurations without actually applying them.
If this command is not installed on your machine, then install it using:
$ dnf install authconfigYou can also take a backup of the PAM configuration file using the authconfig command. Use the following command to create a backup:
$ authconfig --savebackup=/root/pambackupfileThis command generates a backup for PAM. It will create a pambackup directory containing the backup files. You can also restore from the backup by using the --restorebackup option.
[ Want to learn more about security? Check out the IT security and compliance checklist. ]
Wrap up
In this article, you learned about PAM, which helps you secure authentication processes. In the examples, I showed you how you can make your password quality stronger. Sysadmins focus a lot of effort on authentication security because a strong user passwords help make user accounts more secure. In this article you also found out about the authconfig command-line utility for PAM. I hope these will help you while you deal with Linux security.
About the author
Shiwani Biradar is an Associate Technical support Engineer in Red Hat. She loves contributing to open source projects and communities. Shiwani never stops exploring new technologies. If you don't find her exploring technologies then you will find her exploring food. She is familiar with Linux, Cloud, and DevOps tools and enjoys technical writing, watching TV series, and spending time with family.
More like this
Navigating the Mythos-haunted world of platform security
MCP security: Logging and runtime security measures
Collaboration In Product Security | Compiler
Keeping Track Of Vulnerabilities With CVEs | Compiler
Browse by channel
Automation
The latest on IT automation for tech, teams, and environments
Artificial intelligence
Updates on the platforms that free customers to run AI workloads anywhere
Open hybrid cloud
Explore how we build a more flexible future with hybrid cloud
Security
The latest on how we reduce risks across environments and technologies
Edge computing
Updates on the platforms that simplify operations at the edge
Infrastructure
The latest on the world’s leading enterprise Linux platform
Applications
Inside our solutions to the toughest application challenges
Virtualization
The future of enterprise virtualization for your workloads on-premise or across clouds
