Before 1990, the notion of carrying a phone around in your pocket and being able to talk to other people that had a phone in their pocket was the stuff of science fiction. Today, if you don't have a cellphone, you're considered a bit of a relic.
The proliferation of cellphones has fundamentally changed the telecommunications industry. It's no longer a matter of just connecting two devices using a piece of wire. It's become much more complex. Today, cellphones—and mobile computing in general—affect a broad spectrum of technologies, from global networking to voice translation. As a result, there's a good argument to be made that if you want to stay viable in the world of modern enterprise architecture, you need to understand the fundamentals of mobile computing architecture. There's just too much happening on the mobile landscape to think otherwise.
But mobile computing is extremely complex technology. Understanding the basics requires deciphering the dozens of acronyms that have become part of the technical language—NEF, AMF, BTS, NR, UPF, EPC, BBU—to name just a few. Getting a handle on it all can be a daunting task.
Still, if you're an enterprise architect and you want a basic understanding of the essentials of mobile computing architecture, you've got to start somewhere. This article is that somewhere.
In this article, I'll cover the essentials of mobile computing architecture. I'll go over the basics of mobile networking and infrastructure. In a follow-up article, I'll talk about how mobile architecture aligns to the most essential of business requirements—providing service to customers on the move and keeping track of the services they use. And then I will briefly discuss how the next generation of cellular technology will affect things in the world to come.
Understanding wireless networking
The key principle of communication over a wireless network, as the name implies, is wireless—a mobile device (such as a cellphone or tablet) exchanges radio signals with a receiving point, typically an antenna or cell tower. In mobile networking parlance, the antenna or cell tower is called a base station. From there, internal mechanisms in the mobile network connect the caller to a callee who is also exchanging radio signals with another base station. Also, these internal mechanisms do the authentication work necessary to allow a caller access to the network and monitor call activity for billing purposes. These internal mechanisms are part of what is called the core network.
Last but not least, a critical feature of mobile networking is the ability to provide uninterrupted service even when a mobile device's connection is passed among cell towers as a device moves in and out of a tower's range. And, to add even greater complexity to the task, the cell towers supporting a call might belong to a different carrier company from the one to which the caller is subscribed. Supporting roaming among carrier networks is an essential aspect of mobile telephony, especially for callers who travel internationally.
How the handoff happens has evolved over the years to increase efficiency and speed of communication. Nonetheless, being able to maintain a connection between callers on the move without any interruption in service is, and has been, the central feature of mobile computing. This was true from the beginning, even back when cellphones were big, clunking devices we carried around in briefcases or hard-wired into automobiles. Without the ability to hand off calls, mobile computing would be impossible.
[ You might also be interested in An overview of 7 tech trends reshaping Enterprise Architecture. ]
This figure illustrates the basic architectural pattern that is essential to all mobile computing.

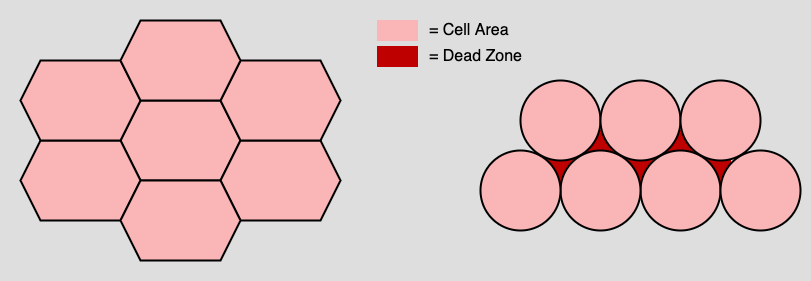
In terms of physical geography, base stations are grouped into an organizational unit called a cell, hence the terms cellphone and cellular network. A cell region is hexagonal. The reason is that hexagons can be assembled with contiguous borders, thus avoiding the hazard of dead zones. Notice in Figure 2 below that the assembled hexagons on the left side of the illustration are contiguous and have no openings between them, thereby creating no dead zones. However, the assembled circles on the right side have many dead zones, shown in red.
The typical distance between a base station and a mobile device can be five to 40 miles depending on the topography of the physical terrain. In urban areas where there are many high-rise buildings and tunnels, the range can be even less. As mentioned, once a cellphone or tablet goes out of range from a particular base station, intelligence within the wireless network transfers the connection to another base station without any interruption in communication. Let's take a look at how this happens.
It's all about the (radio) waves
In the scheme of things, the world of wired networking is a simple place. You connect two devices using a metal or fiber optic cable and then send data through it. It's surprisingly similar to the childhood activity of making a rudimentary telephone by connecting two empty tin cans with a long, taut piece of string. You connect the cans, give one can to a friend who walks away until the string connecting the cans is pulled tight. Then you talk into one of the cans while your friend has their ear in the can at the other end of the string. Voila! You have a phone call. The vibrating string is the carrier of the sound of your voice.
Wireless networking is a lot more complex. It's as if you're shouting into thin air. There's no string available to capture the vibrations of your voice. Some other medium is needed to conduct the conversation. That medium is the radio wave, which is essentially an electromagnetic signal traveling at a specific frequency through space.
Radio communication works because your voice is mapped onto a radio wave according to a particular frequency. The person on the other end of the call has a device listening for the radio wave at that frequency and extracting your voice from the electromagnetic signal as it arrives.
Using radio waves in a cellular network has four fundamental implications for commercial telecommunications:
The first implication is commercial. The frequencies that mobile carriers can use are sold and regulated by government agencies. A carrier cannot use any frequency it wants. The range of frequencies, called a spectrum, is purchased from a government authority. Unlike the wired world in which any company can use any type of wire it wants to connect its devices, in the wireless world, carriers can use only the frequencies they're assigned. Thus, a good deal of business negotiation is thrown into the mix when creating a wireless network for public consumption.
The second implication has to do with the transmission distance. Radio signals traveling at a higher frequency can't go as far as those traveling a lower frequency—they drop off. So, the lower you go in the frequency spectrum, the further a wave can travel.
The third implication is that radio waves traveling at higher frequencies translate into faster throughput. Higher frequencies give you faster download and upload times. The tradeoff is that devices downloading data at higher frequencies need to be closer to base stations than devices using lower frequencies. This means having a cellular network with lots of base station towers grouped in closer proximity.
The fourth and final implication is that radio waves can have a more challenging time penetrating natural barriers such as caves, mountain ranges and manufactured obstacles such as walls and ceilings. So, while you do want your signals to go as far as possible, you don't want to risk losing service because the radio waves can't get through an obstacle. In 5G technology, high-frequency waves can even be subject to distortion due to conditions in the atmosphere such as moisture.
Figure 3 illustrates the distribution and use of radio-wave frequencies in terms of wavelength and energy consumption. The figure also shows the names associated with the ranges of frequencies on the spectrum.
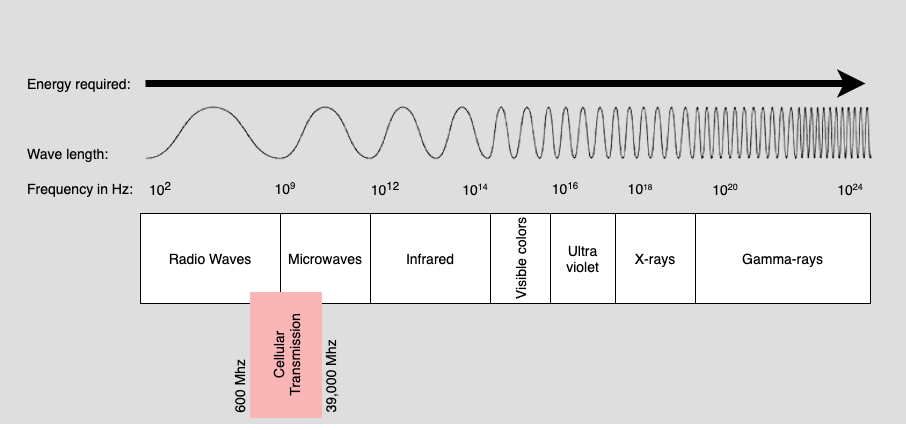
Cellular networks use the range between 600MHz and 39GHz (39,000MHz). In the early days of wireless communication, commercial providers operated at the lower end of the spectrum, around 300–700MHz. But, as 4G and Long Term Evolution (LTE) technology became commonplace around 2010, carriers used frequency ranges in the 2GHz (2,000MHz) range along with the ranges down around 600MHz. Today as 5G, the next generation of mobile networking, takes hold, some wireless network companies are moving into the 28–39GHz part of the spectrum while repurposing frequencies on the lower end of the spectrum, when available, within regulatory constraints.
[ A free guide from Red Hat: The automation architect's handbook. ]
The critical thing to understand from an architectural perspective is that essential communication among any device on the wireless network depends on radio waves and their transmission behavior. Everything—from the quality of a call on a cellphone to download speeds to an IoT device —is affected by the behavior of these radio waves. While there are many situations where private WiFi networks are the conduits through which information flows, there's still a lot of data exchanged between mobile devices that use carrier-based telecommunication networks. But, regardless of whether you're using WiFi and a commercial carrier, it's still all about the radio waves. They're foundational to mobile communication.
Now that I've covered radio waves, in my next article, I'll move to the mechanics of connecting calls and having customers pay for their mobile service.
About the author
Bob Reselman is a nationally known software developer, system architect, industry analyst, and technical writer/journalist. Over a career that spans 30 years, Bob has worked for companies such as Gateway, Cap Gemini, The Los Angeles Weekly, Edmunds.com and the Academy of Recording Arts and Sciences, to name a few. He has held roles with significant responsibility, including but not limited to, Platform Architect (Consumer) at Gateway, Principal Consultant with Cap Gemini and CTO at the international trade finance company, ItFex.
More like this
Red Hat Learning Subscription Course reimagines virtual training
Red Hat Learning Subscription Course: Skills for the future
What’s The Recipe For Burnout? | Compiler
In Defense Of Legacy | Compiler: Legacies
Browse by channel
Automation
The latest on IT automation for tech, teams, and environments
Artificial intelligence
Updates on the platforms that free customers to run AI workloads anywhere
Open hybrid cloud
Explore how we build a more flexible future with hybrid cloud
Security
The latest on how we reduce risks across environments and technologies
Edge computing
Updates on the platforms that simplify operations at the edge
Infrastructure
The latest on the world’s leading enterprise Linux platform
Applications
Inside our solutions to the toughest application challenges
Virtualization
The future of enterprise virtualization for your workloads on-premise or across clouds
