The beta of Red Hat Insights malware detection service is now available. The malware detection service is a monitoring and assessment tool that scans Red Hat Enterprise Linux (RHEL) systems for the presence of malware, utilizing over 175 signatures of known Linux malware provided in partnership with the IBM X-Force Threat Intelligence team. The Red Hat Insights analysis provides:
-
The list of signatures scanned against your RHEL systems, with links to reference information and analysis reports
-
Results for individual system scans and aggregated results for all of your RHEL systems
To scan your Red Hat Insights systems for potential malware, follow our getting started guide. After your first full scan, you can view the results in the beta version of Insights malware detection.
Please note: Due to the potentially sensitive nature of this information, only Organizational Admins have default access to the results. All other users must first be given access to the service, as detailed in section 2.2. of the Insights malware detection guide.
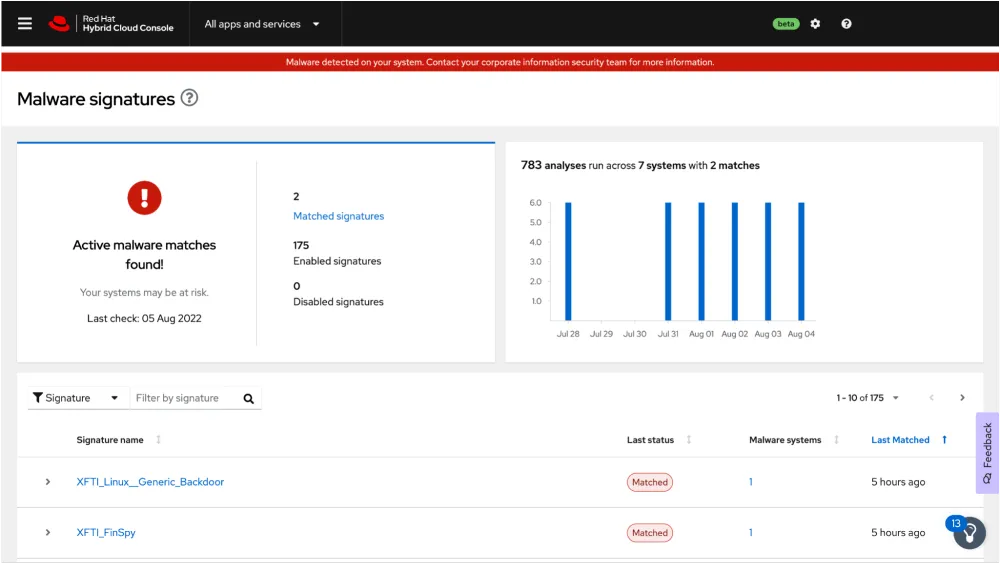
We hope you don’t see a screen like the one below, but if signature matches are found on your systems, you will see details about the signatures, the number of systems that were matched and details about where on the system the matches were found.
 Like the other Insights services, malware detection is included in your RHEL subscription. Malware detection supports RHEL 7 Server / Workstation and RHEL 8 and 9 hosts.
Like the other Insights services, malware detection is included in your RHEL subscription. Malware detection supports RHEL 7 Server / Workstation and RHEL 8 and 9 hosts.
Any feedback about the new malware detection service can be sent to us using the Feedback button inside of Insights — you can see it in the above screenshot on the lower right hand side of the page. Please give the Insights malware detection service a try soon!
執筆者紹介
Shane McDowell is a Principal Product Manager for Red Hat. He is focused on helping customers manage their infrastructure in the hybrid cloud. He brings 20+ years of experience with delivering and supporting technology solutions to users in a variety of industries, including Information Technology, Talent Acquisition and Residential Management.
類似検索
Ansible Automation Platform 2.6 へのアップグレードパスを計画する
サイバーセキュリティにおける AI の 4 つのユースケース
Collaboration In Product Security | Compiler
Keeping Track Of Vulnerabilities With CVEs | Compiler
チャンネル別に見る
自動化
テクノロジー、チームおよび環境に関する IT 自動化の最新情報
AI (人工知能)
お客様が AI ワークロードをどこでも自由に実行することを可能にするプラットフォームについてのアップデート
オープン・ハイブリッドクラウド
ハイブリッドクラウドで柔軟に未来を築く方法をご確認ください。
セキュリティ
環境やテクノロジー全体に及ぶリスクを軽減する方法に関する最新情報
エッジコンピューティング
エッジでの運用を単純化するプラットフォームのアップデート
インフラストラクチャ
世界有数のエンタープライズ向け Linux プラットフォームの最新情報
アプリケーション
アプリケーションの最も困難な課題に対する Red Hat ソリューションの詳細
仮想化
オンプレミスまたは複数クラウドでのワークロードに対応するエンタープライズ仮想化の将来についてご覧ください
