Microsoft's Active Directory (AD) is the go-to directory service for many organizations. If you and your team are responsible for a mixed Windows and Linux environment, then you probably would like to centralize authentication for both platforms. I'll cover how to add Linux computers to an Active Directory domain.
Active Directory and the need for centralized access management
Microsoft's Active Directory, more popularly known as AD, has held the lion's share of the market for enterprise access management for many years now. It is used by institutions and individuals the world over to centrally control access to resources belonging to the organization. It gives you the ability to manage users, passwords, resources such as computers, and dictate who has access to what. For some of you reading this write-up, especially those who work in large institutions, you have interacted with AD before. Usually, the interaction is using one set of login credentials to log in to any workstation in the organization. That is just the tip of a large iceberg.
Imagine a collection of 40 computer systems and 70 users in a firm. Some employees run shifts while others work regular hours. Some have access to printing; others don't. The traditional way of working is to create local user accounts on each computer a user needs to access. Imagine the workload on the end-user support team. When a user changes his password for any reason, that user has to change the password on all computers he previously had access to, to keep things in sync. In no time, there will be mayhem. Now, imagine two members of the staff resign. I do not need to tell you the monotonous work that has to be repeated any time there's a change to the staffing or any workstations. For IT teams, this is a nightmare. Time that could be used for innovative tasks is now spent reinventing the wheel. I have not even spoken about managing access to the printers.
This is where a directory service such as Active Directory thrives. It can literally be a lifesaver. With Active Directory, each user is uniquely created as an object in a central database, with a single set of credentials. Each computer system is also created as an object. Automatically, every user can access every workstation with that same set of credentials. Any account changes that need to be made are made once at the central database. Members of staff can access the printers using the same set of credentials. The printers' authentication mechanism can be coupled with AD to achieve that. Happy users, happy IT team.
[ Related reading: How to integrate Active Directory Federation Services (ADFS) authentication with Red Hat SSO using SAML. ]
Using groups and organizational units, access to various resources can be tailored and maintained. It gets even better. This directory can store staff phone numbers, email addresses, and can be extended to store other information. What if someone resigns? No problem. Just disable the user's account. That person's access to all resources is nullified on the spot. The bigger the organization, the greater the need for centralized management. It saves time; it saves emotions.
At its heart, a directory service is just an organized way of itemizing all the resources in an organization while facilitating easy access to those resources. Basically, AD is a kind of distributed database, which is accessed remotely via the Lightweight Directory Access Protocol (LDAP). LDAP is an open protocol for remotely accessing directory services over a connection-oriented medium such as TCP/IP.
AD is not the only directory service based on the x.500 standard, or that can be accessed using LDAP. Other directory services include OpenLDAP and FreeIPA. However, AD is a mature Windows-based service that comes incorporated with Windows Server systems. In other words, it's going to be the automatic winner when your organization has many Windows systems. This is one of the reasons for its ubiquity. Directory services such as FreeIPA are Linux-based and provide an excellent service for a Linux stable. When the rubber hits the road, the choice boils down to which of the two you can set up quickly, given your current environment and your team's skill set.
[ Learn how to manage your Linux environment for success by downloading this free eBook. ]
But what happens when you choose AD, and you have a few CentOS servers, and you do not want to maintain a separate set of credentials for your Linux users? That overhead is entirely avoidable. What you need to do is join the Linux servers to the AD domain, like you would a Windows server.
If that is what you need to do, then read on to find out just how to do it. It is possible to join a Windows system to a FreeIPA domain, but that is outside the scope of this article.
Prerequisites
This article presupposes that you have at least some introductory-level experience with Active Directory, especially around user and computer account management. Aside from that, the following obvious requirements need to be met:
- An account in AD that has the privileges necessary to join a system to the domain.
- A Linux server (a CentOS 7 server was used for this demonstration).
- A Domain Controller.
- Ensure your Linux server knows how to find the domain controller via DNS.
To make this article easier on everyone, here's a list of key details. This is how the lab I used for this write up is set up, so you should modify accordingly.
- AD Domain Name: Hope.net
- User account for joining the domain: fkorea (Fullname - Fiifi Korea)
- Linux server hostname: centy2
Packages to install
For this configuration, the essential package to install is realmd. Aside from realmd, there are a host of packages that need to be installed to make this work.
# yum install sssd realmd oddjob oddjob-mkhomedir adcli samba-common samba-common-tools krb5-workstation openldap-clients policycoreutils-pythonRealmd provides a simplified way to discover and interact with Active Directory domains. It employs sssd to do the actual lookups required for remote authentication and other heavy work of interacting with the domain. In the interest of brevity, I won't dwell on the other packages in the list.
However, for those interested in the details, a quick Google search should be of great help.
[ Learn about setting up multi-factor authentication on Linux systems. ]
Realmd (interacting with the domain)
Now that all packages have been installed, the first thing to do is to join the CentOS system to the Active Directory domain. We use the realm application for that. The realm client is installed at the same time as realmd. It is used to join, remove, control access, and accomplish many other tasks. Here is the expected syntax for a simple domain join:
realm join --user=[domain user account] [domain name]The space between the user account and the domain account is not a typo. By inserting the corresponding details, we get the following command:
# realm join --user=fkorea hope.netSupply the password when the prompt appears and wait for the process to end.

Don't let the short absence of output deceive you. There are a number of operations that go on as part of the process. You can tack on the -v switch for more verbose output. However, the best way to check if the computer is now a member of the domain is by running the realm list command. The command attempts to display the current state of the server with regard to the domain. It is a quick and dirty way to know which groups or users can access the server.
Have a look at its output:

It is also quite trivial to place the newly-created AD computer object in a specific Organizational Unit (OU) from the onset. I'll leave that for further reading, but, as a tip, you can consult the man page. Using the realm client, you can grant or revoke access to domain users and groups. A deep dive on using realmd in a more fine-grained way is enough to make another article. However, I will not be out of order to pick out a few parameters for your attention, namely client-software and the server-software. By now, you should understand why we had to install so many packages.
To leave the domain altogether, you need two words: realm leave
Further configuration
So now that the Linux server is part of the AD domain, domain users can access the server with their usual credentials. We are done, right? Wrong. "What's the problem?" I hear you say.
[ Free cheat sheet: Get a list of Linux utilities and commands for managing servers and networks. ]
Well, for starters, this is the barebones configuration to get you up and running. But the experience is clunky, to say the least. We need to configure the service further to give it a true AD feel. It should be just like logging on to a domain-joined Windows 10 workstation.
Secondly, there is the big elephant in the room for sysadmins called Dynamic DNS Updates (DynDNS). If it is not set up correctly, we create extra overhead by having to maintain DNS records manually. For an environment that relies heavily on DNS, that could be a problem. For Windows systems, joining a system to the domain means two entries are automatically managed and maintained on the DNS server. When IP addresses change, the change is automatically reflected in DNS. This means you can change the IPs of systems without incurring the cost of manual maintenance. This will only make sense to people who already take advantage of DNS in their environments. Aside from the noticeable productivity gains of automation, it helps to have both Windows and Linux environments working the same way.
The third issue is DNS Scavenging. In an Active Directory domain, DNS is usually provided by the Domain Controllers. Every system joined to the domain has an automatic DNS entry with a corresponding IP address. This is super convenient. Automatically, at a specified interval, stale DNS records are deleted to prevent misdirected packets and also take care of deleted computer objects. This is known as scavenging, and it is not turned on by default in AD. However, if it is turned on, we need to configure it. Typically, the scavenging interval is seven days. If, after that period, there has been no update to the record, it is deleted, unless it is a static record. For Windows systems, the Dynamic Updates feature is automatically set up. However, with Linux servers, a few modifications need to be made. Without doing that, we will have services going down after a while because their records are deleted from DNS, and no one knows how to reach their component parts.
Now that we know some of the potential issues we need to address, let's take a look at some of the things we can tweak to deliver a more seamless experience to the end-user and the sysadmin.
SSSD (easier logins and dynamic updates)
sssd on a Linux system is responsible for enabling the system to access authentication services from a remote source such as Active Directory. In other words, it is the primary interface between the directory service and the module requesting authentication services, realmd. Its main configuration file is located at /etc/sssd/sssd.conf. As a matter of fact, this is the main configuration file we will modify.
[ Discover 3 ways SSSD logging improvements make sysadmins' lives easier. ]
Let's have a look at its contents before configuration. Once you join the domain, it is immediately modified to contain the minimum information required for a successful logon. My file looked like this:

In order to solve all three of the problems I mentioned earlier, edit your file to look like the one below:
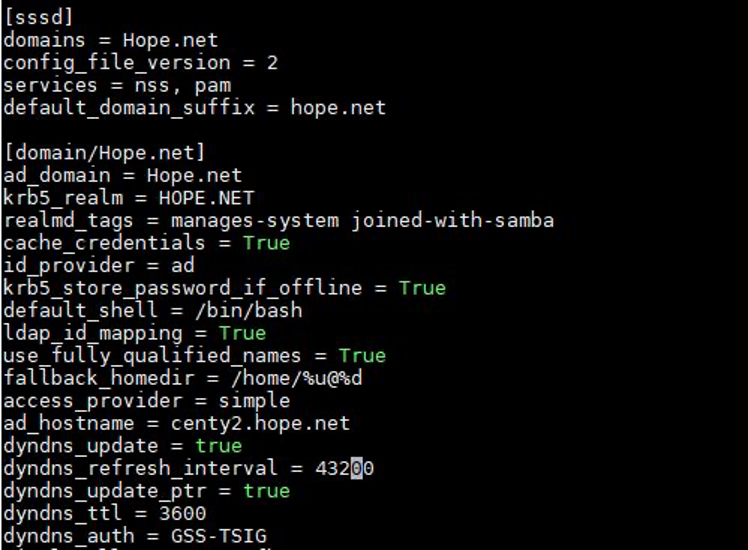
Most of the options are self-explanatory, and you can modify yours accordingly while we step through what some of the key options represent. More information on all the options can be obtained by checking the man page. I think it is well written. Just type man 5 sssd.conf at the command line. You can also view the man page for sssd_ad for further information.
First and foremost, the configuration file is separated into two sections. The global section, under [sssd] and the domain-specific options section, [domain/[domain name]].
The global section contains options that affect the general behavior of sssd, such as the version information and related services. One key parameter under this section is shown below:
- default_domain_suffix - Set this to the domain name if you do not want to have to type the full user account name when logging in. Instead of having to type
fkorea@hope.netalways, you can just typefkoreaand the password. This helps a lot when you have a long domain name.
The domain-specific section contains parameters that are specific to the domain you have joined. Key parameters are:
- access_provider - Allows you to select a provider optimized and used for interacting with AD servers for authentication purposes. It should be set to
ad. Other values that can be used here areldapandipa, assuming you use those directory services. - id_provider - Allows you to select a provider optimized and used for interacting with AD servers for identification purposes. It should be set to
ad. - ad_hostname - This should be the fully qualified hostname of the server. It should be set if the system's hostname is anything other than the fully qualified domain name. If this is not set and the
sssddoes not have access to the fully qualified hostname, dynamic updates will fail. - ad_domain - This should be the full domain name (
hope.netin this case). - cache_credentials - This enables AD users to log in when the domain controller is offline. When this is set to true, credentials are cached for a period such that authentication does not fail when the back end is offline. The period of storage is also configurable.
- fallback_homedir - This helps you set a home directory for AD users who do not have a home directory attribute in AD. This is different from the override_home parameter that works when a home directory is set in AD for users.
- dyndns_update - This enables dynamic DNS updates and accepts either true or false as a value. When dynamic updates are enabled, updates occur primarily under three conditions:
- When the Linux server restarts.
- When the provider comes online.
- When the refresh interval is due.
- dyndns_refresh_interval - This value is in seconds with a practical minimum of 60 seconds. It accepts integer values and has a default of 24 hours (86400s). In this example, we set it to 12 hours. If nothing else triggers an update, an update is regularly done between.
- dyndns_update_ptr - A boolean value that specifies whether the associated PTR record is to be updated in every update cycle. PTR records are used for reverse lookups, and unless there is a good reason, this should be set to true.
- dyndns_auth - Specifies whether the dynamic updates should be done securely or not. The setting depends on the mode accepted by AD. If AD is set to Accept Secure Updates Only, this value should be set to GSS-TSIG. If not, and you do not care for the security benefits of secure dynamic updates (despite the strong warning in AD), this value can be set to none.
Once the configuration is complete, restart sssd to apply settings immediately.
# systemctl restart sssdAt this point, we are set. We can now login like we would at a Windows workstation or server.


Visudo (granting admin privileges)
Users that are granted access have unprivileged access to the Linux server. For all intents and purposes, all Active Directory accounts are now accessible to the Linux system, in the same way natively-created local accounts are accessible to the system. You can now do the regular sysadmin tasks of adding them to groups, making them owners of resources, and configure other needed settings. If the user tries any activity that requires sudo access, the familiar error is presented. As can be seen in the inset, our user is not in the sudoers file.
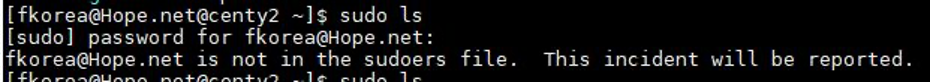
In that light, we can edit the sudoers file directly to grant them superuser privileges. This is not an article on granting superuser privileges, but we can use the visudo tool to interact safely with the sudoers file.
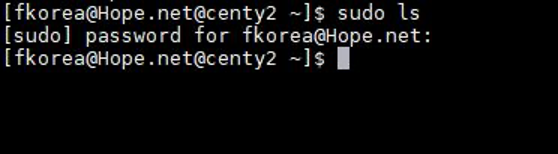
Alternatively, we could have just added the user to the wheel group. The point is the user account is now available to be used by the system.
[ Network getting out of control? Check out Network automation for everyone, a free book from Red Hat. ]
Wrap up
Try this out in your organization or lab environment. It is obvious I just scratched the surface on this topic but this will get you pretty far into the process. Check out the respective documentation if you want to explore options not covered in this article.
Joining a Linux system to an Active Directory domain allows you to get the best of both worlds. The process is very simple and can be scripted using Bash or automated using Ansible, especially during the system's initial setup. If you are still managing a group of more than five systems without a directory service and a good reason, please do yourself a favor and get one set up. You can thank me later.
About the author
Edem is currently a sysadmin with a financial services institution where he works primarily with Windows and Linux systems. He also administers VMware Virtualization environments daily. With interests in Automation, IP Telephony, Open Source Alternatives and Information Security, Edem dabbles with technology on any level. He likes to break systems to understand them.
More like this
Red Hat Enterprise Linux now supported for Microsoft SQL Server on Azure VMs with SQL IaaS Agent extension
Announcing Red Hat Advanced Cluster Security for Kubernetes 4.10
Collaboration In Product Security | Compiler
Keeping Track Of Vulnerabilities With CVEs | Compiler
Keep exploring
- Managing infrastructure at cloud scale
E-book - Build an efficient IT foundation for modern business successE-book
- Start your trial: Red Hat Enterprise Linux
Trial
Browse by channel
Automation
The latest on IT automation for tech, teams, and environments
Artificial intelligence
Updates on the platforms that free customers to run AI workloads anywhere
Open hybrid cloud
Explore how we build a more flexible future with hybrid cloud
Security
The latest on how we reduce risks across environments and technologies
Edge computing
Updates on the platforms that simplify operations at the edge
Infrastructure
The latest on the world’s leading enterprise Linux platform
Applications
Inside our solutions to the toughest application challenges
Virtualization
The future of enterprise virtualization for your workloads on-premise or across clouds
