Today we present a new way to use the Red Hat Insights Advisor service by using system tags to enable extended security hardening recommendations.
Not all systems are equal. For example, a web server and a workstation have different security profiles. For systems with extended security hardening recommendations enabled, Advisor identifies additional risks and remediation steps.
What is Red Hat Insights Advisor?
Red Hat Insights is a Software-as-a-Service offering that analyzes applications and platforms to identify risks and recommend detailed remediation steps. The Insights Advisor service proactively identifies issues that may affect system security, performance, availability and stability. Advisor uses the knowledge and findings from Red Hat support and Red Hat Product Security and turns them into actionable recommendations before a risk materializes and causes operating environment downtime.
How does Red Hat Insights improve system security and performance?
Security is a process with many objectives, including assets to protect, threats to protect against, vulnerabilities to remediate and risks to mitigate. These objectives come with a number of costs, such as the cost of security measures, the cost of assets and the cost of breaches, to name a few. This means that security policies are shaped by business needs. Red Hat Insights provides a number of ways it can be tailored to the particular needs of your organization with regard to security, performance, availability and stability.
In previous blog posts, we showed how to fine-tune and apply security standards in Regulatory compliance at scale with Red Hat Insights, how to prioritize vulnerability patching in Defense in depth with Red Hat Insights and enabling extra Advisor recommendations relevant to your organization in Finding and using disabled recommendations in Red Hat Insights Advisor. Opting selected systems into stricter security hardening recommendations is a new option to bolster the security of your sensitive systems while keeping the standard set of Advisor recommendations for the rest of your systems.
Red Hat Insights Advisor extended security hardening
Advisor security recommendations identify aspects of configuration that present security risks, such as opening a system to a Man-in-the-Middle attack, or decreased defense-in-depth measures. We are careful to provide recommendations with a high signal-to-noise ratio that are focused on displaying a limited number of items with high impact.
For example, SELinux is enabled by default in Red Hat Enterprise Linux (RHEL), but Advisor by default displays security recommendations related to disabled SELinux only in specific situations where SELinux provides exceptionally clear value, such as when running containers. With extended security hardening, Advisor displays recommendations related to disabled SELinux in more system configurations, where SELinux provides a defense-in-depth value.
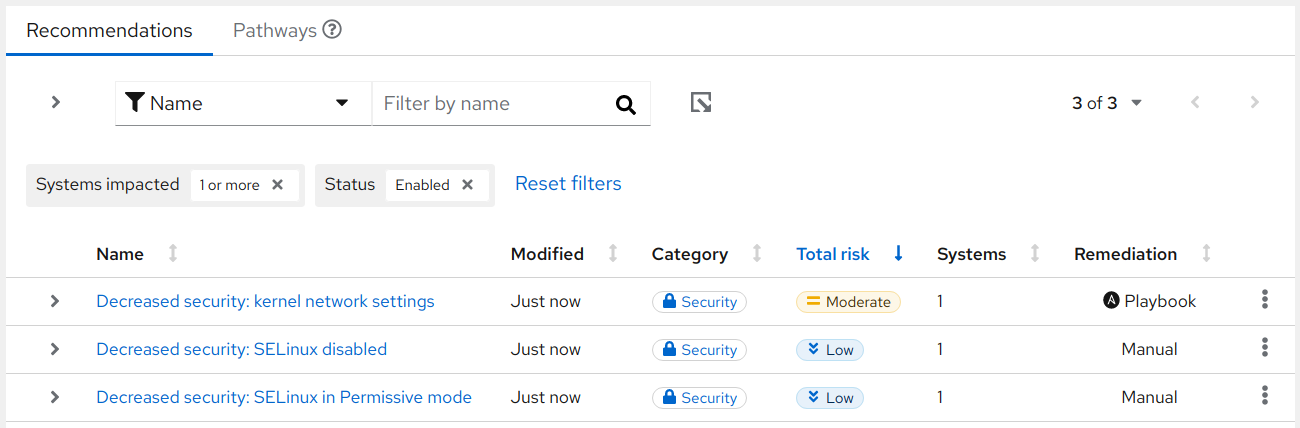
We are introducing this feature with three new recommendations that display additional content for systems that are opted-in to additional hardening.
- Decreased security: kernel network settings
- Decreased security: SELinux disabled
- Decreased security: SELinux in Permissive mode
Selected Advisor recommendations for RHEL will adjust their behavior in one of two ways in response to the security: strict setting in the file /etc/insights-client/tags.yaml. Some recommendations will be exclusive to extended security hardening, while other recommendations will present enhanced detection and remediation capabilities under extended security hardening.
How to use extended security hardening recommendations via system tags
On RHEL systems, edit the file /etc/insights-client/tags.yaml and set the security key to value strict. If the file doesn’t exist, create the file and insert the following line:
security: strict
For more information, refer to How to leverage tags to make Red Hat Insights Advisor recommendations understand your environment better? and Insights Client documentation about tags.yaml.
Run insights-client or wait until the next scheduled Insights upload (within 24 hours).
Once this setting is set on the system, Insights will report new recommendations that apply to the security: strict tag. At the moment these include:
- The recommendation Decreased security: SELinux disabled is exclusive to extended security hardening and shows up when SELinux is disabled.
- The recommendation Decreased security: SELinux in Permissive mode is also exclusive to extended security hardening and shows up when SELinux is enabled but not set to Enforcing.
- The recommendation Decreased security: kernel network settings detects additional
sysctlconfiguration with extended security hardening.
We plan to keep expanding the list of recommendations that offer special content for systems that use extended security hardening.
We are always looking for feedback to improve our products. If you have suggestions or questions about Red Hat Insights, feel free to reach out to us using the feedback form in the Hybrid Cloud Console or the Red Hat Customer Portal feedback form.
Learn more
About the author
Red Hatter since 2016. Focused on engineering automated security risk detection and mitigation for Red Hat Product Security and Red Hat Insights. Jakub Svoboda completed his Master's degree in Informatics in the field of Information Technology Security at Masaryk University and has worked in the field ever since.
More like this
Fragnesia and friends: When page cache vulnerabilities keep coming back
10 essential reads to optimize performance, security, and ROI in the AI era
Collaboration In Product Security | Compiler
Keeping Track Of Vulnerabilities With CVEs | Compiler
Browse by channel
Automation
The latest on IT automation for tech, teams, and environments
Artificial intelligence
Updates on the platforms that free customers to run AI workloads anywhere
Open hybrid cloud
Explore how we build a more flexible future with hybrid cloud
Security
The latest on how we reduce risks across environments and technologies
Edge computing
Updates on the platforms that simplify operations at the edge
Infrastructure
The latest on the world’s leading enterprise Linux platform
Applications
Inside our solutions to the toughest application challenges
Virtualization
The future of enterprise virtualization for your workloads on-premise or across clouds