Automation Platform
-
Overview Get started
Features
- Automation coding assistant
- Automation intelligent assistant
- Ansible plug-ins for Red Hat Developer Hub
- Event-Driven Ansible
- Self-service automation portal
- Automation execution environments
- Automation controller
- Automation mesh
- Ansible Content Collections
- Ansible automation hub
- Automation dashboard and automation analytics
- Ansible development tools
-
All features
-
Use cases -
Integrations Extend your use of Ansible Automation Platform with partner offerings, including certified collections and resources.
-
Deployment options - Documentation
Use case
Automated Policy as Code with Red Hat Ansible Automation Platform
Build compliance into automation for more reliable IT infrastructure and AIOps.
Overview
For IT teams keeping up with innovation and heightened security and compliance pressures, Policy as Code (PaC) can build confidence in operations. Manual policy enforcement isn’t fast or efficient enough for enterprises to meet these needs, especially as AI becomes a priority. To minimize risks such as downtime, human error, security threats, and non-compliance, IT teams need consistent ways to keep operations aligned. Policy enforcement at automation runtime helps teams ensure that the right actions are being taken by the right people—at the right times.
Red Hat’s vision for automated Policy as Code complements and extends automation with compliance and control. Once fully delivered in Red Hat® Ansible® Automation Platform, these capabilities will allow you to build internal and external requirements, security needs, and granular mandates into automation processes—so that you can consistently enforce policies and improve reliability across your operations.
Enforce policies to keep AI in check
If you're adopting AIOps, this means infusing AI inferences into automated IT actions. In enterprise environments, you need to ensure that your AI-driven automation will function within the boundaries of internal and external policies. With Ansible Automation Platform, you can enforce policies at automation runtime to ensure every AIOps action aligns with intended outcomes.
Our vision for automated Policy as Code
Once fully delivered, Ansible Automation Platform’s PaC capabilities will automate compliance and governance from a single platform so you can:
Create
Enforce policies during the creation of automation code
Apply Governance, Risk and Compliance (GRC) policies without slowing down development productivity or the creation of new automation content. Ensure consistent enforcement of policies from the start.
Manage
Integrate policy enforcement before or during automation runs
Apply policies across the operational life cycle—including Day 0, Day 1, and Day 2 processes. Check automation against policies before executing. Control costly infrastructure actions, like limiting cloud instance sizes.
Scale
Simplify reporting and easily identify out-of-policy areas
Efficiently complete audit and reporting to improve team productivity. Automatically identify out-of-policy technologies and align them quickly.
What’s new: Policy enforcement manages automation at runtime
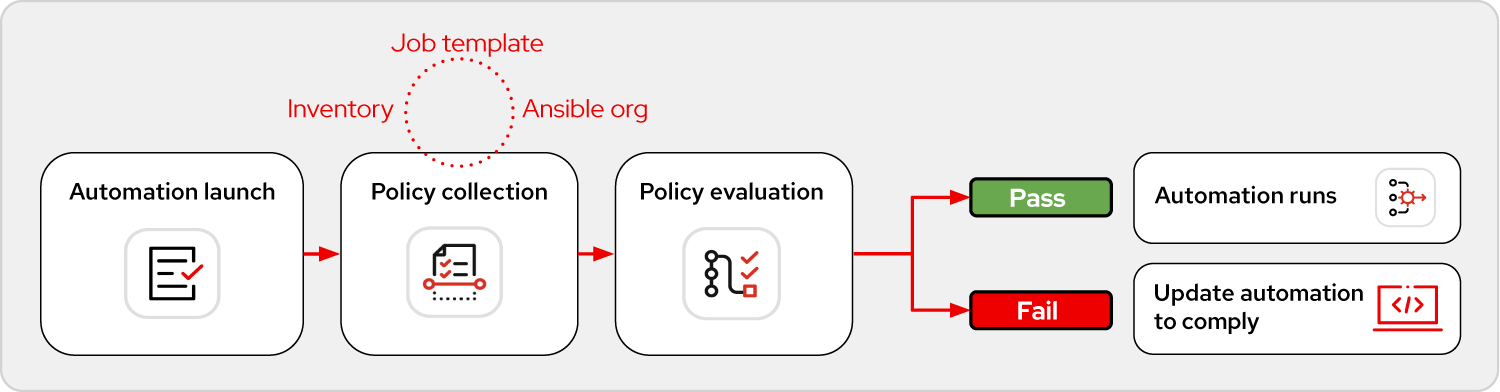
In our first installment of Policy as Code capabilities, Red Hat is focusing on the manage aspect of the vision described above. Ansible Automation Platform now includes policy enforcement that checks automation against externally-stored policies associated with the job template, Ansible organization, and inventory levels at automation runtime—to ensure automation is compliant before it runs.
The policies you design are stored in an Open Policy Agent (OPA) server. These policies describe what you want to be checked or enforced. Before an automation job runs, Ansible Automation Platform validates it against the policies you specify. If the policies pass, the automation is allowed to run. If a policy fails, the automation doesn't run and the user receives feedback on the failure.
Policy enforcement examples
Red Hat recommends a “start small, think big” approach to automation adoption—and the policy enforcement component is no exception. The following use cases are good starting points for automated policy enforcement, and you can grow from these into many others. For each of the use cases described below, we’ve created example policies which you can use to get started.
Control where a policy applies
Set where you want a policy to be applied across the job template, Ansible organization, or inventory level. Associate the policy you define with one of these levels to prevent undesired actions.
Manage who automates which inventory
Create policies that prevent certain users from automating portions of your operation. For example, a policy can prevent a superuser from executing automation at the job template, Ansible organization, or inventory levels.
Regulate when automation runs
Use policy enforcement to control when automation is allowed to run, as you design it in the policy. For example, allow automation only during planned maintenance or disallow it during peak operational timeframes.
Control which variables can be passed into automation
Ansible Automation Platform enables flexible automation by passing in extra variables and their values. Policy enforcement can allow or prohibit specific variables and their values from being used in automation, based on what you define in your policy.
Prevent mismatches between credentials and inventory
Prevent mismatched use of automation, such as a job template intended for development inventory that is attempting to run on production inventory. This can help minimize security risks, human error, and disruptions to the production environment.
Enforce naming conventions
Apply naming conventions based on standards included in a policy. For example, check that dev_, test_ or prod_ is included in the name of platform components. This helps you match naming standards between jobs, inventories, projects, and credentials so automation runs only on the correct targets.
See how it works
Discover how to automate policy enforcement with Ansible Automation Platform.
Applying runtime policy enforcement
Ansible Automation Platform is a highly flexible platform for automating within and across many areas of your IT operations. You can start by applying the above use cases to your operations, but automated policy enforcement can quickly produce benefits in the following three areas:
Enable policy-driven AIOps
Policy enforcement at automation runtime is a recommended best practice for AIOps actions. Set boundaries around automation jobs, inventories, and event-driven automation to ensure the AI only executes automation that fits within your policy.
Manage security and compliance
Apply policies to many aspects of your security and compliance process. Control which users or user types can automate specific actions. Stop automation from executing for a period of time—for example, during an incident investigation window.
Control CloudOps
Use policy enforcement to optimize CloudOps and limit associated costs. For example, set policies that prevent the provisioning of new cloud resources by specific users or within specific dynamic inventory groups.
FAQs
As an Ansible Automation Platform subscriber, how can I get access to the new policy enforcement feature?
Ansible Automation Platform customers can access the new policy enforcement feature by downloading Ansible Automation Platform 2.5.5. Policy enforcement works with external Open Policy Agent (OPA) servers which contain the policies you want to enforce. You can link to the specific policy you want to check in the job template, inventory, and Ansible organization menus.
Does the new policy enforcement feature require an Open Policy Agent server?
Yes, this is a current requirement. Your policies will be stored in this server and you will provide a path to the specific policy you want to enforce in Ansible Automation Platform menus. Red Hat is interested in your feedback about which policy server technologies you are interested in using. You can provide this feedback through your sales team or submit your idea here.
Where can I learn more about the policy enforcement component?
Refer to the documentation which will be updated when policy enforcement is generally available. The policy enforcement examples repository is also an excellent resource to help you with idea generation for your own policy checks.
Partners: join the automated Policy as Code ecosystem
Partners can work with Red Hat to develop automated Policy as Code in two ways:
- System integrators and resellers can include automated Policy as Code as part of service offerings—such as part of an automation or Governance, Risk and Compliance (GRC) practice—to help customers advance on their automation journey.
- Technology partners can create Ansible Content Collections to help joint customers implement best practices using automated Policy as Code. This is a means of codifying the best practices customers should follow to optimize success with your solution.
If you would like to participate in the Ansible Automation Platform ecosystem, contact your Red Hat partner team.
Red Hat named the leader in infrastructure automation platforms
Forrester Research named Red Hat Ansible Automation Platform the leader in The Forrester WaveTM: Infrastructure Automation Platforms, Q4, 2024—with the highest score in the strategy category.
Keep learning
Checklist
6 reasons to automate Policy as Code for better compliance
Explore 6 key benefits of using automated Policy as Code (PaC) for GRC practices.
Video
Automated Policy as Code overview
Watch a conversation about automated Policy as Code, why it's important now, and how Ansible Automation Platform can help.
Checklist
4 ways to prepare for automated Policy as Code
Development and operations teams can take these steps now to get ready for automated PaC.