Nmap (Network Mapper) is popularly known as the sysadmin’s Swiss Army knife. Since things in a corporate network don’t go as smoothly as desired, those debug/"Save me" tickets can pile up in your work log.
Nmap comes to your rescue. In this article, I explore six practical use cases for Nmap.
Using Nmap
Nmap allows you to scan your network and discover not only everything connected to it, but also a wide variety of information about what's connected, what services each host is operating, and so on. It allows a large number of scanning techniques, such as UDP, TCP connect (), TCP SYN (half-open), and FTP. It also offers a wide variety of scan types, including Proxy (bounce attack), Reverse-ident, ICMP (ping sweep), FIN, ACK sweep, Xmas, SYN sweep, IP Protocol, and Null scan. See the man page's Scan Techniques section for more details.
Nmap also offers a number of advanced features such as operating system (OS) detection
via TCP/IP fingerprinting, stealth scanning, dynamic delay and retransmission calculations, parallel scanning, detection of down hosts via parallel pings, decoy scanning, port filtering detection, direct (non-portmapper) RPC scanning, fragmentation scanning, and flexible target and port specification.
Let's explore some of the practical use cases that can help you deal with your network.
Use case one
The Nmap syntax outlined in the man page is as follows:
nmap [ <Scan Type> ...] [ <Options> ] { <target specification> }
There are many switch options that can be used along with Nmap, but let's focus on the practical one. For this use case, scan the hostname with the nmap <hostname> command like this:
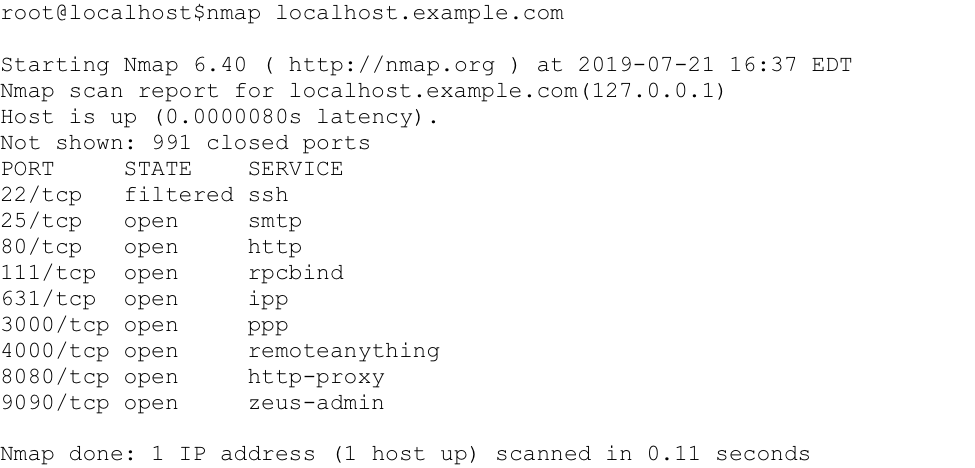
Use case two
If you have more than one host you need to scan, list all the hosts in a hosts.txt file. Then, use the command nmap -iL <file containing host names>, like so:
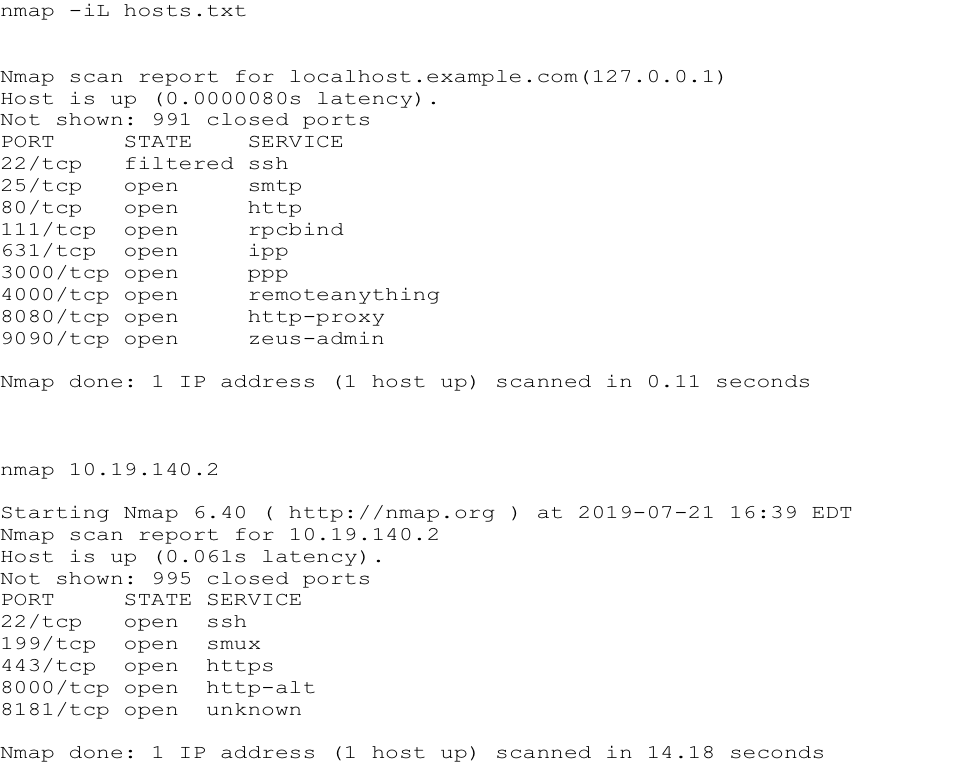
Use case three
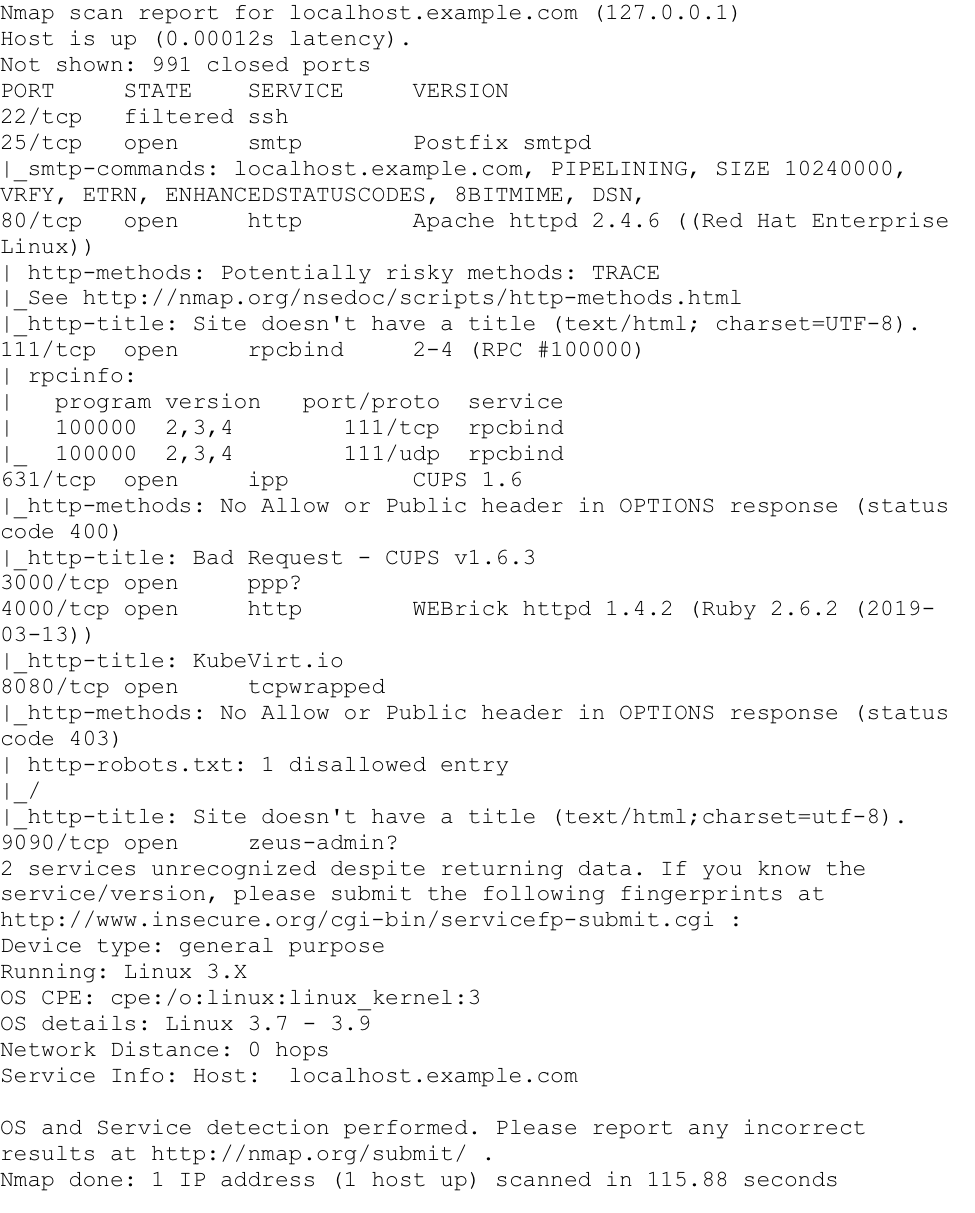
When using Nmap, it is possible to identify a host's operating system (OS), which is useful for an inventory sweep of your network. Use the -A switch to determine the OS for a remote system. For example, running:
$ nmap -A localhost.example.com
resulted in:
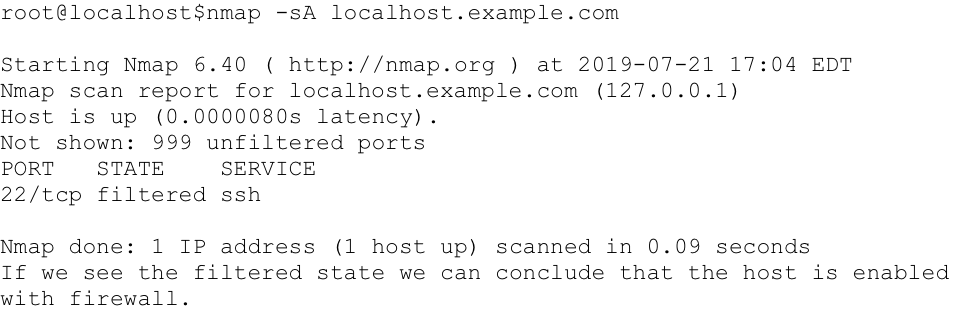
Use case four
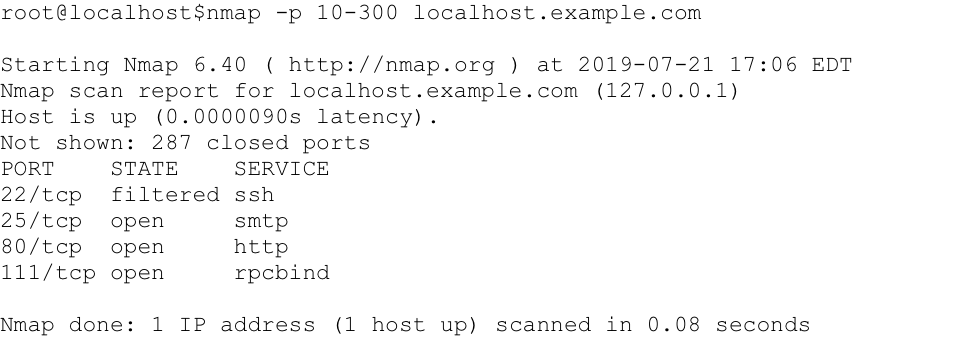
Nmap can help you gain a deeper understanding of your network's security concerns. To determine whether a remote host has a firewall enabled, and which ports are filtered, use -sA. The word filtered in the output below suggests that this host is enabled with a firewall:
Use case five
Whenever we want to check the weak points of a host we need to first analyze the open ports (well-known), to give us an idea of which services are enabled on that host. Using the -p switch, Nmap scans the range of ports specified, as shown below:
Use case six
To perform a stealth scan for TCP information, use the -sT option. This type of scan is handy when you can't use the -sS (SYN) type scan, which is the default—and is stealthier than the TCP connect scan shown below:

Exploring further
These six use cases will start you in the right direction with Nmap. As you discover more of Nmap's power as a network discovery and inventory tool, you'll see that Nmap is an essential part of your sysadmin toolbox.
Please exercise caution with Nmap, though. Either get permission to use it or inform your IT and security staff that you are performing network sweeps and probes so that your monitoring alerts don't trigger a security incident. Nmap is used by all shades of the hacker spectrum, so this warning should be taken seriously. As with any power tool in your toolbox, there is utility as well as danger.
About the author
I work as a Solutions Engineer at Red Hat and my day-to-day work involves OpenShift and Ansible. I'm highly passionate about open source software, cloud, security, and networking technologies.
More like this
4 reasons to start using image mode for Red Hat Enterprise Linux right now
Advancing post-quantum capabilities of SSH in Red Hat Enterprise Linux
OS Wars_part 1 | Command Line Heroes
OS Wars_part 2: Rise of Linux | Command Line Heroes
Browse by channel
Automation
The latest on IT automation for tech, teams, and environments
Artificial intelligence
Updates on the platforms that free customers to run AI workloads anywhere
Open hybrid cloud
Explore how we build a more flexible future with hybrid cloud
Security
The latest on how we reduce risks across environments and technologies
Edge computing
Updates on the platforms that simplify operations at the edge
Infrastructure
The latest on the world’s leading enterprise Linux platform
Applications
Inside our solutions to the toughest application challenges
Virtualization
The future of enterprise virtualization for your workloads on-premise or across clouds
