Red Hat Ansible Automation Platform (AAP) is a complete suite for multilevel automation tasks in on-premises, cloud, edge, and other environments. It also handles different types of assets, from operating systems to network devices. The platform is modular and consists of at least 8 different components you can integrate according to your needs. The primary component is the automation controller. From there, you can implement and combine the other pieces.
In this article, I focus on one of those pieces—the Private Automation Hub—and show you how to get started with it.
Note: If you have already read my colleague Ashraf Hassan's great article Introducing the new Ansible Private Automation Hub, then you know what it is and how its software-as-a-service (SaaS) model works. I encourage you to read this article to learn some core concepts and then come back here to continue the step-by-step process of configuring your own Hub.
[ Get started with automation controller in this hands-on interactive lab. ]
Ansible Private Automation Hub deployment
To keep this content as objective and concise as possible, I won't go into detail about the steps needed to install Private Automation Hub in your environment. I suggest you follow the available official documentation for that information. Instead, I'll share which deployment inventory file variables I enabled and how I set them up.
[root@controller ansible-automation-platform-setup-2.3-1]# pwd
/opt/ansible-automation-platform-setup-2.3-1
[root@controller ansible-automation-platform-setup-2.3-1]# grep hub inventory | grep -v '#'
[automationhub]
ansiblehub.example.local
automationhub_admin_password='mypass'
automationhub_pg_host='ansiblecontroller.example.local'
automationhub_pg_port=5432
automationhub_pg_database='automationhub'
automationhub_pg_username='automationhub'
automationhub_pg_password='mypass'
automationhub_pg_sslmode='prefer'
automationhub_upgrade='true'
automationhub_api_token='mytoken'
Remember that this is a lab environment and that other configuration options are available, especially in a production environment. Another useful note is that my automation controller is also my database host, and I refer to it as such.
Finally, be aware that Private Automation Hub integrates with a Red Hat Single Sign-On (RH-SSO) by default, whether implemented alongside AAP or an external RH-SSO. In my case, I removed this integration for my own benefit, but don't do this in production.
Now that you have some context on the environment, it's time to configure the Private Automation Hub as an on-premises repository for Ansible Collections (it can also be a repository for other resources). It replaces Ansible Galaxy (which is upstream) or the Private Automation Hub in the SaaS model.
Configure and sync the repositories
With the Private Automation Hub installed, configured, and running, access its URL address and use the side menu on the left to navigate to the Repository Management option under the Collections option, as shown below.
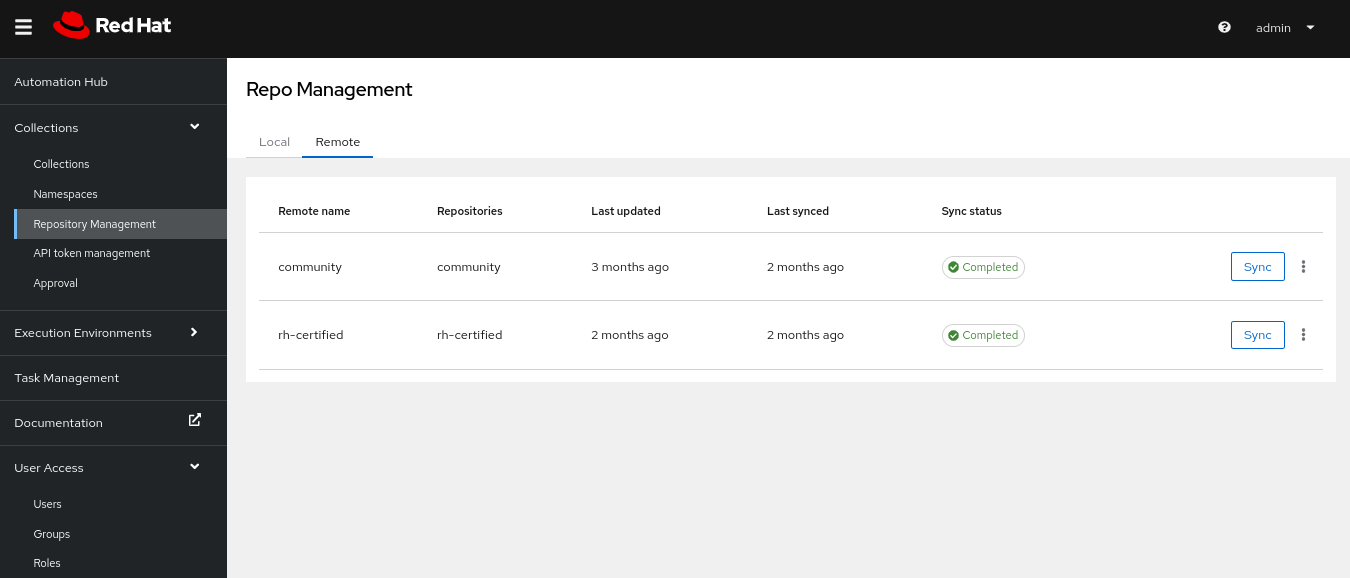
Two options are available: community (for upstream content) and rh-certified (for Red Hat-certified content). I'll configure both. Click on the ellipses (...) icon to open an editing window.

Start with the community repository. Fill in the following values in this window:
- Name: The repository name (automatically filled)
- URL: The repository URL, in this case https://galaxy.ansible.com/api/
- YAML requirements: A YAML file with the names of the collections you want to import. Below is an example:
---
# requirements.yml
# This requirements file lists all the collections from
# the red hat ansible automation hub that we want installed on Controller
collections:
- community.general
- ansible.posix
- Username:: Your Ansible Galaxy username
- Password: Your Ansible Galaxy password
Save the file and go to the next one. Use it to configure the rh-certified repository, shown below.

Fill in the following values in this window:
- Name: The repository name (automatically filled)
- URL: The repository URL, in this case
https://console.redhat.com/api/automation-hub/ - Token: The token you create in the Red Hat cloud portal (see the official documentation to create this token)
- SSO URL: The URL to authenticate clients to download content from Private Automation Hub, in this case,
https://sso.redhat.com/auth/realms/redhat-external/protocol/openid-connect/token - Username: Your Private Automation Hub username
- Password: Your Private Automation Hub password
Once you finish, click the Sync button on both repositories and wait for it to finish synchronizing with the remote repositories. The status will show as "Running" while synchronization takes place.

When both finish, the status changes to "Completed."

Navigate to the side menu again in the collections option and sub-option of the same name and change "Filter by repository" to "Red Hat Certified" to see all the new certified repositories available for on-premises use through Private Automation Hub.
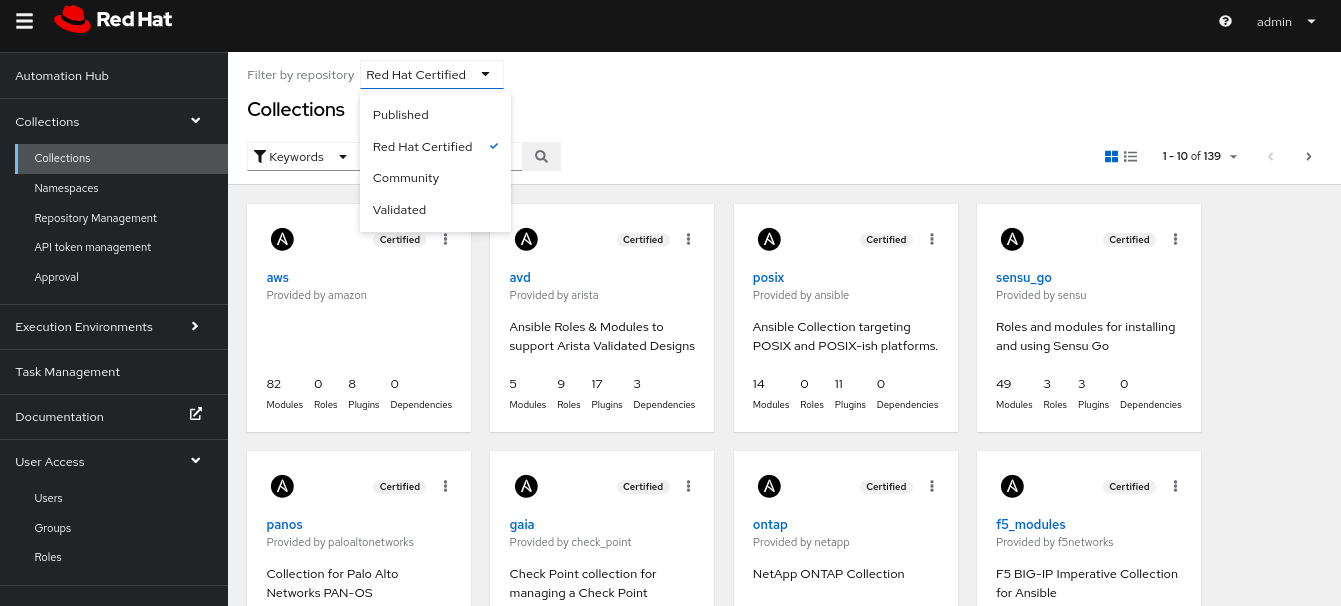
If you want more details about a specific collection, navigate to it, click on it, and information about it will be available. This approach works for modules, installation, documentation, dependencies, and more. See an example of the redhat.satellite collection below.

To use this collection, install it on the target machine using the command given in the installation field. The Private Automation Hub will deliver it to the machine. I'll create a prerequisite configuration for this and then install a couple of example collections.
[ Need more on Ansible? Take a no-cost technical overview course from Red Hat. Ansible Essentials: Simplicity in Automation Technical Overview. ]
Define Private Automation Hub as a content source
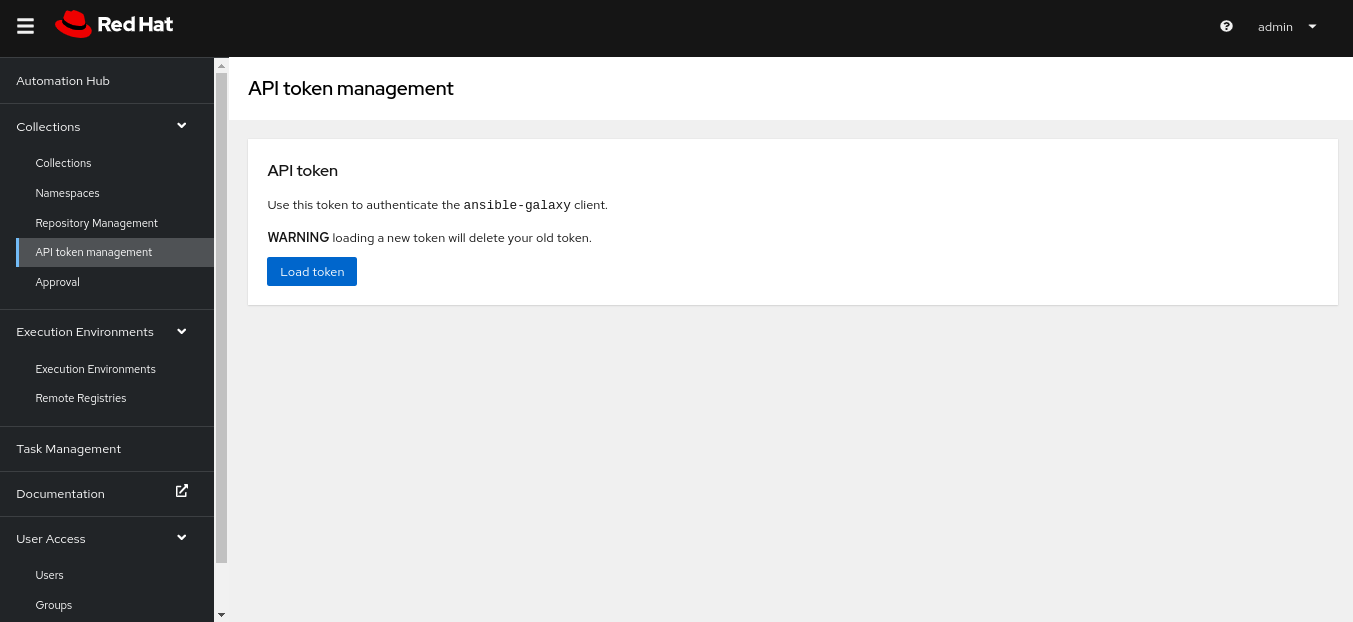
As a good security and administration practice, first create a token to connect from the target machine on Private Automation Hub to download the desired collections. To do this, go to the Collection option again in the side menu and then to the API-token-management option. Click the Load-token option to generate a new token. Keep this token secure. If you lose it, you must generate a new one and every time you do, the previous token is erased. For obvious reasons, I won't show my generated token, but only the window where you can generate yours.
Go to the Collection option again and select the Repository-management option and you'll see the list of synced and locally available repositories.
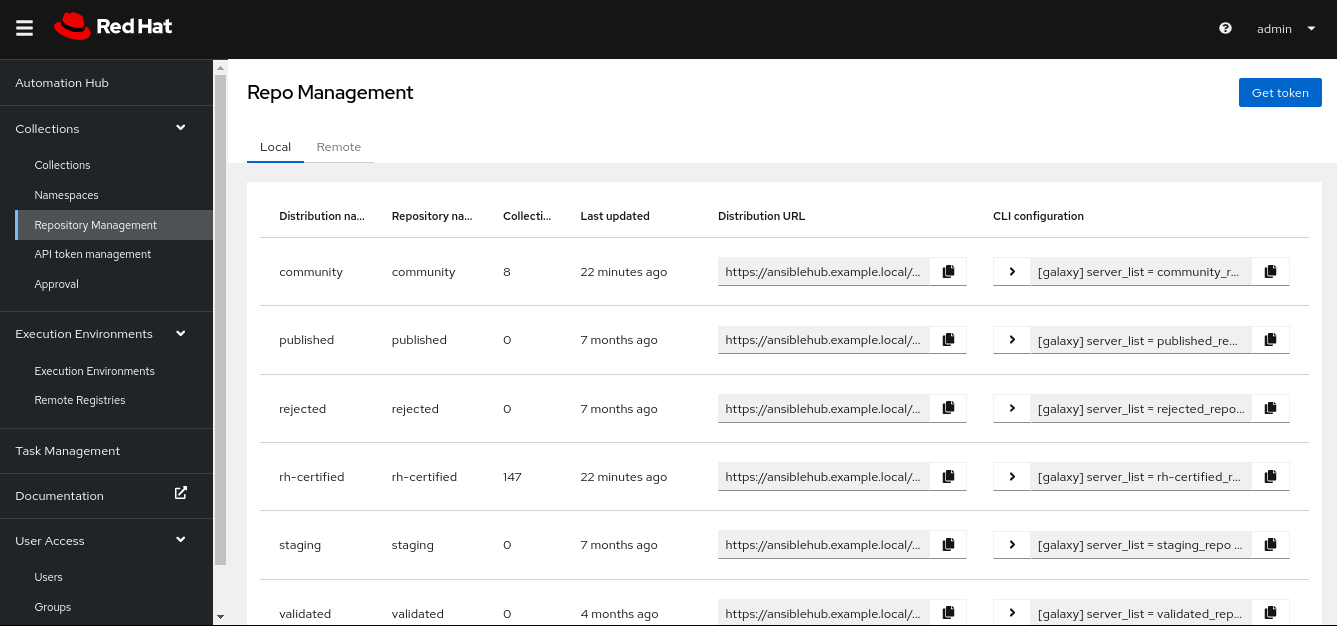
To use one or more of these repositories on your target machines, click on the Copy icon in the field under the CLI-configuration option. It will copy the parameters and configuration needed to the target machine. With this information, go to the desired target machine, edit the /etc/ansible/ansible.cfg file, and paste the content you copied from Private Automation Hub so that this configuration is globally available on your system. As a demo, I copied it from the rh-certified and community repositories.
# cat /etc/ansible/ansible.cfg | grep -v '#'
[galaxy]
server_list = rh-certified_repo, community_repo
[galaxy_server.rh-certified_repo]
url=https://ansiblehub.example.local/api/galaxy/content/rh-certified/
token=mytoken
[galaxy_server.community_repo]
url=https://ansiblehub.example.local/api/galaxy/content/community/
token=mytoken
Done! I have now met all the requirements to start using these collections on the target machine. It's time to test it.
Pull and install collections from Private Automation Hub
If you're already used to doing this with Ansible Galaxy, the process is exactly the same. The example below shows the installation of the redhat.satellite collection from the certified repository and the forced reinstallation of the ansible.posix collection from the upstream repository, both configured in my Private Automation Hub as follows.
# ansible-galaxy collection install redhat.satellite
Starting galaxy collection install process
Process install dependency map
Starting collection install process
Downloading https://ansiblehub.example.local/api/galaxy/v3/plugin/ansible/content/rh-certified/collections/artifacts/redhat-satellite-3.9.0.tar.gz to /root/.ansible/tmp/ansible-local-4150manjntxi/tmpngxsrxpt/redhat-satellite-3.9.0-59s7m38e
[WARNING]: The GnuPG keyring used for collection signature verification was not configured but signatures were provided by the Galaxy server to
verify authenticity. Configure a keyring for ansible-galaxy to use or disable signature verification. Skipping signature verification.
Installing 'redhat.satellite:3.9.0' to '/root/.ansible/collections/ansible_collections/redhat/satellite'
redhat.satellite:3.9.0 was installed successfully
# ansible-galaxy collection install ansible.posix --force
Starting galaxy collection install process
Process install dependency map
Starting collection install process
Downloading https://ansiblehub.example.local/api/galaxy/v3/plugin/ansible/content/rh-certified/collections/artifacts/ansible-posix-1.5.1.tar.gz to /root/.ansible/tmp/ansible-local-44409w0lnbxs/tmperthobvl/ansible-posix-1.5.1-peo4wva5
[WARNING]: The GnuPG keyring used for collection signature verification was not configured but signatures were provided by the Galaxy server to
verify authenticity. Configure a keyring for ansible-galaxy to use or disable signature verification. Skipping signature verification.
Installing 'ansible.posix:1.5.1' to
'/root/.ansible/collections/ansible_collections/ansible/posix'
ansible.posix:1.5.1 was installed successfully
# ansible-galaxy collection list
# /root/.ansible/collections/ansible_collections
Collection Version
--------------------------- -------
ansible.posix 1.5.1
redhat.satellite 3.9.0
Now that I have both collections installed, I can start using them. For example, I could check which modules I have available for each, as shown below.
# ansible-doc -l | grep ansible.posix
[WARNING]: Collection redhat.insights does not support Ansible version 2.14.0
ansible.posix.acl Set and retrieve ...
ansible.posix.at Schedule the exec...
ansible.posix.authorized_key Adds or removes a...
ansible.posix.firewalld Manage arbitrary ...
ansible.posix.firewalld_info Gather informatio...
ansible.posix.mount Control active an...
ansible.posix.patch Apply patch files...
ansible.posix.rhel_facts Facts module to s...
ansible.posix.rhel_rpm_ostree Ensure packages e...
ansible.posix.rpm_ostree_upgrade Manage rpm-ostree...
ansible.posix.seboolean Toggles SELinux b...
ansible.posix.selinux Change policy and...
ansible.posix.synchronize A wrapper around ...
ansible.posix.sysctl Manage entries in…
# ansible-doc -l | grep redhat.satellite
[WARNING]: Collection redhat.insights does not support Ansible version 2.14.0
redhat.satellite.activation_key Manage Activation...
redhat.satellite.architecture Manage Architectu...
redhat.satellite.auth_source_ldap Manage LDAP Authe...
redhat.satellite.bookmark Manage Bookmarks
redhat.satellite.compute_attribute Manage Compute At...
redhat.satellite.compute_profile Manage Compute Pr...
redhat.satellite.compute_resource Manage Compute Re...
redhat.satellite.config_group Manage (Puppet) C...
redhat.satellite.content_credential Manage Content Cr...
redhat.satellite.content_export_info List content expo...
redhat.satellite.content_export_library Manage library co...
redhat.satellite.content_export_repository Manage repository...
redhat.satellite.content_export_version Manage content vi...
redhat.satellite.content_upload Upload content to...
redhat.satellite.content_view Manage Content Vi...
redhat.satellite.content_view_filter Manage Content Vi...
redhat.satellite.content_view_filter_info Fetch information...
redhat.satellite.content_view_filter_rule Manage content vi...
redhat.satellite.content_view_filter_rule_info Fetch information...
redhat.satellite.content_view_info Fetch information...
redhat.satellite.content_view_version Manage Content Vi...
redhat.satellite.content_view_version_info Fetch information...
redhat.satellite.discovery_rule Manage Host Disco...
redhat.satellite.domain Manage Domains
redhat.satellite.domain_info Fetch information...
redhat.satellite.external_usergroup Manage External U...
redhat.satellite.global_parameter Manage Global Par...
redhat.satellite.hardware_model Manage Hardware M...
redhat.satellite.host Manage Hosts
redhat.satellite.host_collection Manage Host Colle...
redhat.satellite.host_errata_info Fetch information...
redhat.satellite.host_info Fetch information...
redhat.satellite.host_power Manage Power Stat...
redhat.satellite.hostgroup Manage Hostgroups
redhat.satellite.hostgroup_info Get information a...
redhat.satellite.http_proxy Manage HTTP Proxi...
redhat.satellite.image Manage Images
redhat.satellite.installation_medium Manage Installati...
redhat.satellite.job_invocation Invoke Remote Exe...
redhat.satellite.job_template Manage Job Templa...
redhat.satellite.lifecycle_environment Manage Lifecycle ...
redhat.satellite.location Manage Locations
redhat.satellite.operatingsystem Manage Operating ...
redhat.satellite.organization Manage Organizati...
redhat.satellite.organization_info Get information a...
redhat.satellite.os_default_template Manage Default Te...
redhat.satellite.partition_table Manage Partition ...
redhat.satellite.product Manage Products
redhat.satellite.provisioning_template Manage Provisioni...
redhat.satellite.puppet_environment Manage Puppet Env...
redhat.satellite.puppetclasses_import Import Puppet Cla...
redhat.satellite.realm Manage Realms
redhat.satellite.redhat_manifest Interact with a R...
redhat.satellite.repository Manage Repositori...
redhat.satellite.repository_info Fetch information...
redhat.satellite.repository_set Enable/disable Re...
redhat.satellite.repository_set_info Fetch information...
redhat.satellite.repository_sync Sync a Repository...
redhat.satellite.resource_info Gather informatio...
redhat.satellite.role Manage Roles
redhat.satellite.scap_content Manage SCAP conte...
redhat.satellite.scap_tailoring_file Manage SCAP Tailo...
redhat.satellite.setting Manage Settings
redhat.satellite.setting_info Fetch information...
redhat.satellite.smart_class_parameter Manage Smart Clas...
redhat.satellite.smart_proxy Manage Smart Prox...
redhat.satellite.status_info Get status info
redhat.satellite.subnet Manage Subnets
redhat.satellite.subnet_info Fetch information...
redhat.satellite.subscription_info Fetch information...
redhat.satellite.subscription_manifest Manage Subscripti...
redhat.satellite.sync_plan Manage Sync Plans
redhat.satellite.templates_import Sync Templates fr...
redhat.satellite.user Manage Users
redhat.satellite.usergroup Manage User Group...
You can use Ansible playbooks to do this setup and download collections automatically on other machines in your environment.
Wrap up
Red Hat Ansible Automation Platform provides a complete and modular suite for all types of automation. One of its modular services is Private Automation Hub, which you can deploy in the on-premises model. That way, you can have all the necessary content—like collections—available to your environment in a controlled way. Private Automation Hub also provides many other features, but those are subjects for other articles.
About the author
Alexon has been working as a Senior Technical Account Manager at Red Hat since 2018, working in the Customer Success organization focusing on Infrastructure and Management, Integration and Automation, Cloud Computing, and Storage Solutions. He is a part of the TAM Practices LATAM team based in São Paulo, Brazil, where his job is partnering with, advocating, trust-advising, and supporting customers in their success goals while making use of the complete portfolio. He also contributes to produce and enhance documentation, knowledge-base articles, blog posts, presentations, webinars, and workshops. He is a member of numerous communities in addition to the Sudoers, like Red Hat Academy and Red Hat Accelerators. When he’s not at work, he enjoys spending quality time with his family (wife, daughter, and cat) and participating in several volunteer jobs.
More like this
Managing IT Operations when AI outpaces your patching cycle
Stop managing, start orchestrating: Streamlining catalyst operations with Red Hat Ansible Automation Platform
Operating System Management | Compiler
Technically Speaking | Taming AI agents with observability
Browse by channel
Automation
The latest on IT automation for tech, teams, and environments
Artificial intelligence
Updates on the platforms that free customers to run AI workloads anywhere
Open hybrid cloud
Explore how we build a more flexible future with hybrid cloud
Security
The latest on how we reduce risks across environments and technologies
Edge computing
Updates on the platforms that simplify operations at the edge
Infrastructure
The latest on the world’s leading enterprise Linux platform
Applications
Inside our solutions to the toughest application challenges
Virtualization
The future of enterprise virtualization for your workloads on-premise or across clouds
