The Vault Secrets Operator has achieved Red Hat OpenShift operator certification, allowing OpenShift users to easily install and deploy secrets management on their OpenShift clusters.
HashiCorp Vault: identity-based security to manage access to secrets and protect sensitive data
HashiCorp is a leading provider of multi-cloud infrastructure automation and security software. One of their flagship products, Vault, provides organizations with identity-based security to automatically authenticate and authorize access to secrets and other sensitive information on the cluster.
Kubernetes secret management
There are numerous tools to use to manage secrets. When deciding which ones to use, developers or operators need to address several key challenges:
- Secure storage of the secrets
- Access control
- Managing secrets at scale
- Compliance restrictions
- Secrets rotation
Kubernetes secrets are consumed multiple ways: through files in volumes mounted by containers, container environment variables, or via the Secrets API by an application running on the cluster. Kubernetes natively supports the management and distribution of secrets within the cluster, but it does not support dynamic secrets or secret rotation. These additional functions are left up to the user to manage independently or via additional services.
Using Vault for a complete secrets management solution provides your organization with several benefits, including:
- Reducing security risks and incidents
- Reducing manual effort through automation
- Cost savings
- Increased efficiency
*New* Vault Secrets Operator
HashiCorp Vault provides a complete and comprehensive solution for secrets lifecycle management. However, it also requires users to upskill and learn an entirely new tool and system. Developers and operators need to save time where they can, and they need to focus on meaningful work. They want a cloud-native way to access secrets through Kubernetes without having to deeply understand the Vault product.
Through the newly GA’d Vault Secrets Operator, secrets are accessed as native Kubernetes secrets while still managed by Vault.
The Vault Secrets Operator also enables SecOps to have more control over operational boundaries within engineering teams. SecOps can define, enforce, and control security policies and leverage auditing and monitoring capabilities provided by Vault for access and permissions. This enables overall best practices for secrets management without involving or interacting with developers or complicating application code.
How it works
Kubernetes operators, through the extension of the Kubernetes API, automate and simplify the management of complex applications on Kubernetes clusters.
The Vault Secrets Operator syncs secrets between Vault and Kubernetes natively, in a specified namespace where the applications have access to the secrets. This configuration enables secrets management with Vault using standard Kubernetes integration.
The operator watches for changes to the supported set of Custom Resource Definitions (CRDs) that it manages. These CRDs provide the specifications needed for the operator to synchronize a Vault secret to a Kubernetes secret. The operator writes source Vault secret data directly to the destination Kubernetes secret via the Kubernetes API server. This ensures that as the source changes, the destination changes with it over its lifetime. An application only needs access to the native Kubernetes destination secret to make use of the secret data.
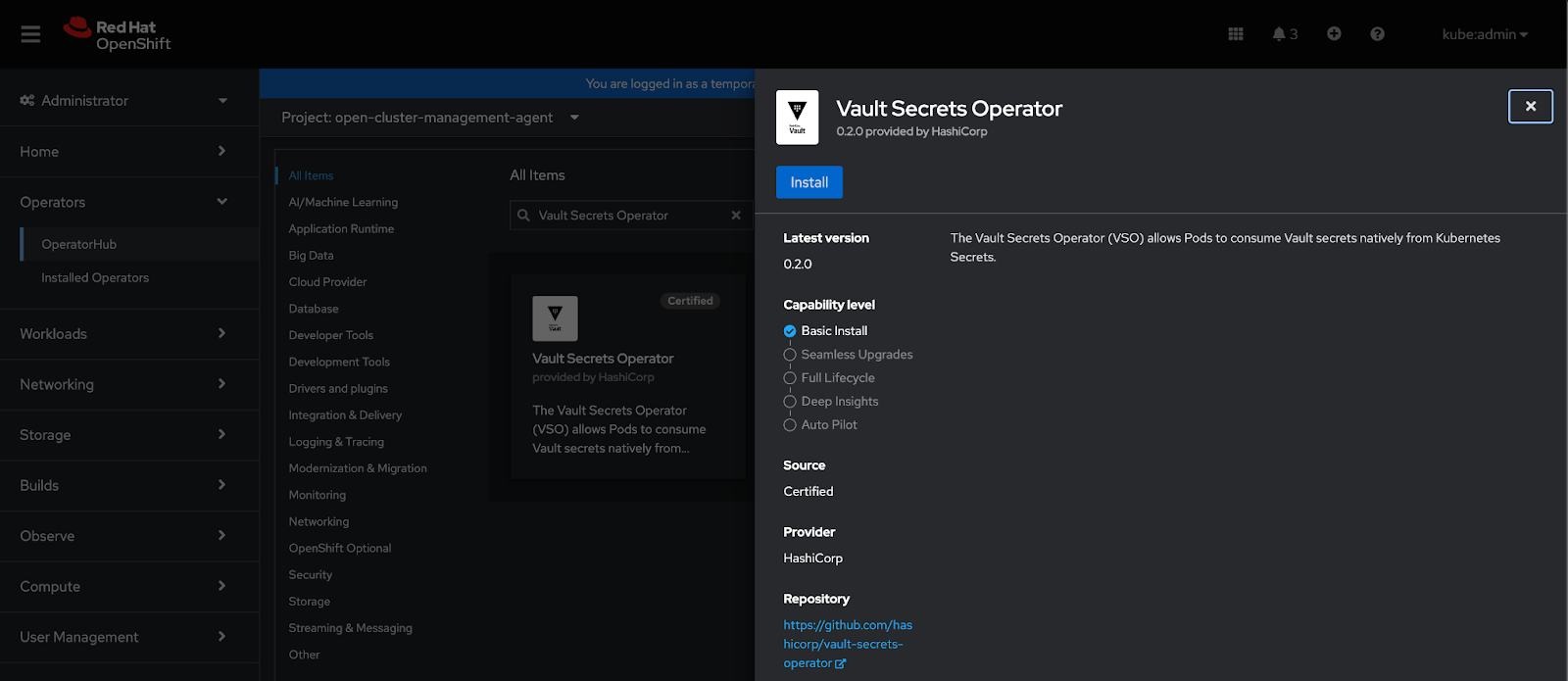
The new operator build, deployable directly from the embedded OperatorHub within the OpenShift console, is the preferred method of managing CRDs, and provides an enhanced installation and upgrade management experience. You may also deploy the operator by using Helm or kustomize.
Getting started
Now that the Vault Secrets Operator is Red Hat certified, you can find and install it directly from the embedded OperatorHub of any OpenShift Container Platform within the administrator console, versions 4.10 through 4.13, and follow their official documentation.
Further Reading
- Vault Secrets Operator documentation for OpenShift
- Vault Secrets Operator tutorial
- Vault Secrets Operator GA blog announcement
Acknowledgments
- David Mills, Senior Technical Product Marketing Manager, HashiCorp
- Steve Almy, Senior Product Manager, HashiCorp
About the author
More like this
CVE-2026-31431: How Red Hat Advanced Cluster Security and Red Hat Advanced Cluster Management can help
Strengthening the enterprise foundation: Red Hat and Oracle’s expanding collaboration
Collaboration In Product Security | Compiler
Keeping Track Of Vulnerabilities With CVEs | Compiler
Browse by channel
Automation
The latest on IT automation for tech, teams, and environments
Artificial intelligence
Updates on the platforms that free customers to run AI workloads anywhere
Open hybrid cloud
Explore how we build a more flexible future with hybrid cloud
Security
The latest on how we reduce risks across environments and technologies
Edge computing
Updates on the platforms that simplify operations at the edge
Infrastructure
The latest on the world’s leading enterprise Linux platform
Applications
Inside our solutions to the toughest application challenges
Virtualization
The future of enterprise virtualization for your workloads on-premise or across clouds