昨今のビジネス環境において、知的財産およびプロプライエタリー AI (人工知能) モデルの保護はますます重要になっています。不正アクセスは、競争力、コンプライアンス、その他の重要な要素に壊滅的な結果をもたらす可能性があるため、最新のセキュリティ対策を導入することが不可欠です。
そのためのテクノロジーの 1 つとして挙げられるのが、ハードウェアベースの 高信頼実行環境 (TEE) を使用してセキュリティ対策を強化したエンクレーブを作成する コンフィデンシャル・コンピューティング です。エンクレーブを使用することで、たとえ権限を持つソフトウェアや管理者によるものであっても、不正アクセスから機密データや計算を保護できます。データは使用中に暗号化されます。コンフィデンシャル・コンピューティングでは、複数層で構成される多層防御戦略に保護層をさらに追加することで、機密データや知的財産の保護を強化します。
CNCF Confidential Containers (CoCo) プロジェクトは、コンフィデンシャル・コンピューティング・テクノロジーを使用するクラウドネイティブ・ソリューションを構築するためのプラットフォームを提供します。Kubernetes ワークロードを高信頼実行環境内で実行して保護する必要がある場合、CoCo は理想的な選択です。
AI のコンプライアンス、プライバシー、セキュリティ、計測などに対するニーズが高まる中、Enkrypt AI はそれに応えるソリューションを構築しています。AI が導き出す洞察にビジネスがますます依存するにつれ、AI モデルおよびデータのインテグリティ、信頼性、プライバシーの確保が最優先事項になっていますが、市場の現行ソリューションはそれに対処しきれていません。このような状況を踏まえ、このブログでは Enkrypt AI が重点を置く分野であるモデルデプロイメントのセキュリティ強化において、同社がどのように CNCF CoCo プロジェクトをその基盤として使用しているか説明します。
コンフィデンシャルコンテナ (CoCo) プロジェクト
CoCo プロジェクトは、Pod レベルでコンフィデンシャル・コンピューティングを 標準化 し、Kubernetes での使用を 単純化 することを目的としています。これにより Kubernetes ユーザーは、基盤となるコンフィデンシャル・コンピューティング・テクノロジーに関する専門知識がなくても、使い慣れたワークフローやツールを使用してコンフィデンシャル・コンテナ・ワークロードをデプロイできます。
CoCo を使用すると、他者が所有するインフラストラクチャに自分のワークロードをデプロイできるため、無許可のエンティティがワークロードデータにアクセスして機密情報を抽出するリスクが大幅に軽減されます。このブログでは、Azure クラウド・インフラストラクチャ に焦点を当てています。技術的には、コンピューターのメモリーを暗号化し、ワークロードが必要とする低レベルのリソースをハードウェアレベルで保護することで機密保持機能を実現しています。
CoCo の脅威モデル、Kata containers プロジェクト (CoCo で広く使用)、CoCo アーキテクチャ、および主要な構成要素の詳細は、パブリッククラウド上でのコンフィデンシャルコンテナのデプロイ をご一読ください。
次の図は、CoCo プロジェクトの最新アーキテクチャ (2023 年 11 月現在) を示しています。
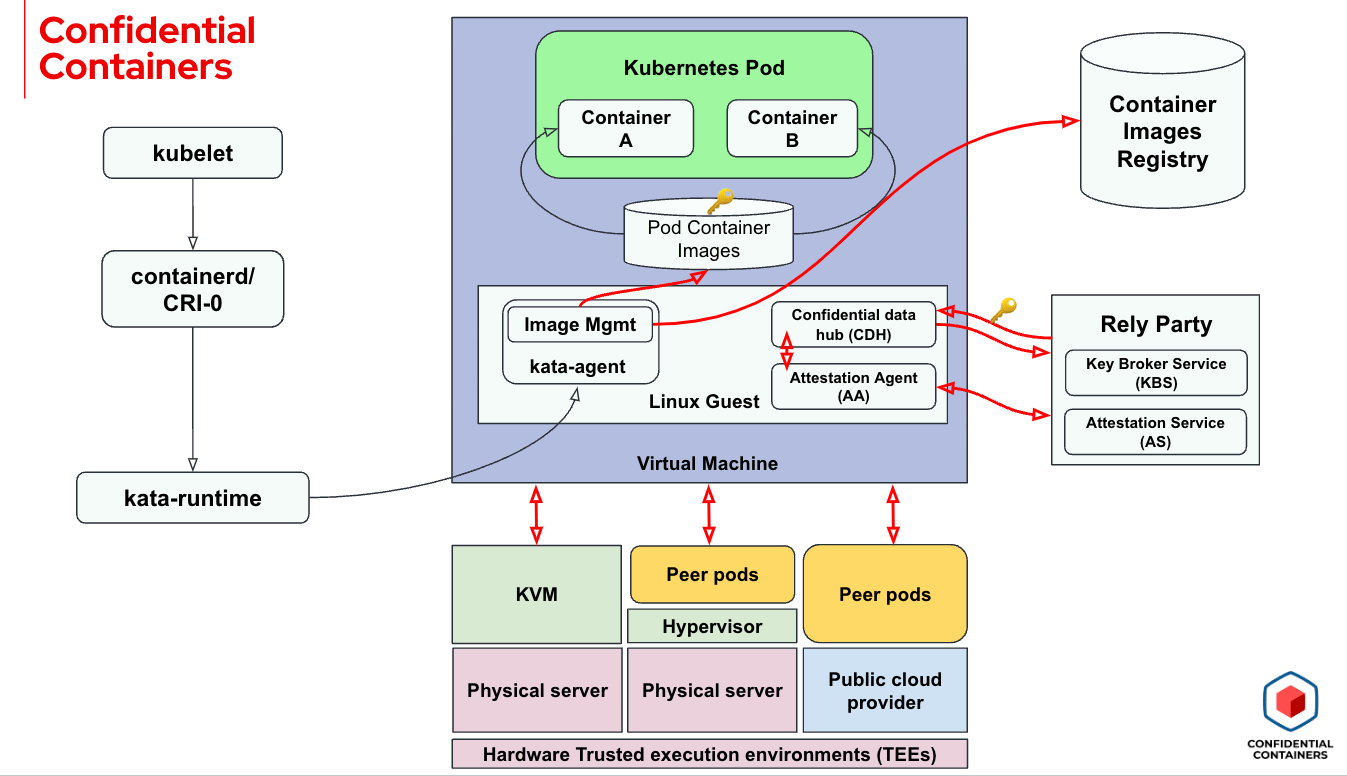
このブログは概要を示すもので、説明を省略したコンポーネントもありますが、読み進める上で理解が必要なポイントを以下でいくつか説明してます。
ピア Pod とは
ピア Pod アプローチでは、環境のネイティブ・インフラストラクチャ管理アプリケーション・プログラミング・インタフェース (API) を使用して、その環境内で Kata 仮想マシンを作成できます。たとえば、Microsoft Azure API を使用して Azure 上に Kata 仮想マシンを作成できます。これは、ローカルハイパーバイザー API (例:QEMU/KVM) を使用して Kata 仮想マシンを作成する代替アプローチとは対照的です。CNCF コンフィデンシャルコンテナ・プロジェクトのサブプロジェクトである cloud-api-adaptor は、ピア Pod アプローチを実装しています。
次の図は、ピア Pod ソリューションを構成する主要コンポーネントを示しています。
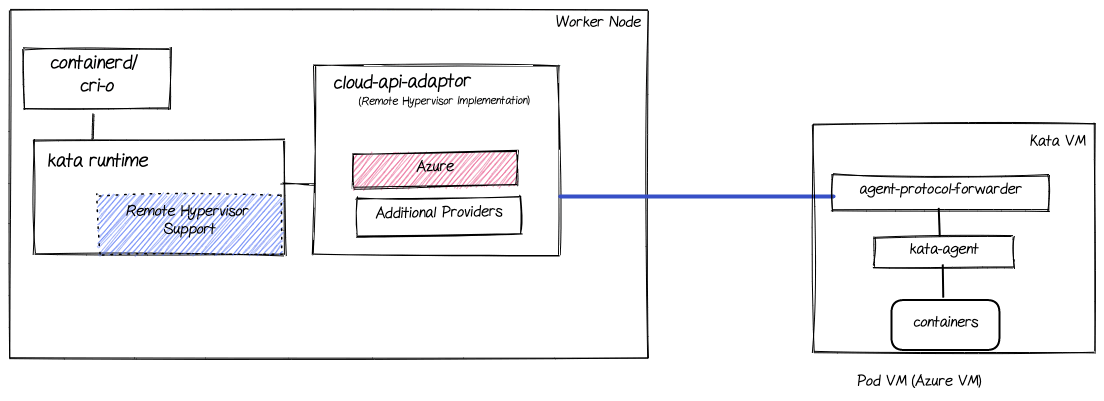
主要コンポーネントの概要:
- リモート・ハイパーバイザー・サポート:ローカルハイパーバイザー API を呼び出すのではなく、インフラストラクチャ・プロバイダー API と対話 (cloud-api-adapter を使用) するために Kata ランタイムを強化します。
- Cloud-api-adaptor:それぞれのインフラストラクチャ API を使用して、サードパーティのインフラストラクチャ上に Kata 仮想マシンライフサイクル管理を実装します。たとえば、cloud-api-adaptor における Azure クラウドプロバイダーのサポートは、Azure クラウドで Kata 仮想マシンライフサイクルを管理するために使用されます。
- Agent-protocol-forwarder:ワーカーノード上で実行されている Kara ランタイムとリモート Kata 仮想マシン間の TCP 経由の通信を可能にします。
ピア Pod が重要な理由
AMD SEV-SNP または Intel TDX が提供する高信頼実行環境で Kubernetes Pod を実行する Azure コンフィデンシャル仮想マシンを作成するにはピア Pod が必要なため、このブログの主題を論じるにあたりピア Pod を欠かすことはできません。
ピア Pod の詳細については、過去記事の ピア Pod ソリューションの概要、ピア Pod の技術的詳細、ピア Pod ハンズオン を参照してください。
アテステーションと鍵管理コンポーネント
CoCo での アテステーション には、暗号ベースの証明を使用してワークロードを改ざんから保護することが含まれます。このプロセスを実行することで、初期状態を侵害する不正なソフトウェア、メモリー変更、悪意のある CPU 状態の影響を受けることなくソフトウェアが稼働していることを検証できます。つまり、CoCo を使用することで、ソフトウェアが信頼される実行環境で改ざんされることなく稼働していることを確認できます。
アテステーション・エージェント (AA) は、仮想マシン (この場合はピア Pod 仮想マシン) 上のプロセスであり、安全に鍵を Pod に解放するためのローカル機能を提供します。AA はゲストコンポーネントの一部で、環境の機密性を証明する TEE エビデンスを収集します。収集されたエビデンスは、固有鍵のリクエストと共にキーブローカーサービス (以下参照) に渡されます。
キーブローカーサービス (KBS) は、リライングパーティとして機能する、リモートでデプロイされる個別サービスです。秘密鍵へのアクセスを管理し、AA が提供するエビデンスの信頼性と事前に定義されたポリシーへの準拠状況に応じて鍵を解放します。KBS は、アテステーションサービス (以下参照) を統合して TEE エビデンスを検証するリモートアテステーションのエントリーポイントです。
アテステーションサービス (AS) は、アテスターが KBS に提供したエビデンスが本物であることを検証するコンポーネントです。AS は、エビデンスの署名と、そのエビデンスが記述するトラステッド・コンピューティング・ベース (TCB) を検証します。検証が成功すると、指定されたエビデンスから TEE に関するファクトを抽出し、統一された要求として KBS に返します。AS は、個別サービスとしてデプロイするか、モジュールとして KBS デプロイメントに統合できます。
次の図は、秘密鍵を必要とする (コンフィデンシャル仮想マシンでバックアップされる) コンフィデンシャル Pod 内でアプリケーションが実行されている場合の、CoCo アテステーション・ワークフローを示しています。

以下はその手順です (図内の番号を参照)。
- ピア Pod のコンフィデンシャル仮想マシン内で、コンフィデンシャル Pod がゲストコンポーネント内の AA に到達し、秘密鍵を取得します。
- AA は KBS に秘密鍵を要求します。
- KBS は、暗号化ナンスで応答します。この暗号化ナンスは、やり取りを再生できないようにするため、エビデンス に埋め込む必要があります。
- AA はエビデンスを KBS に送信します。
- KBS は、AS を使用してこのエビデンスを検証します。
- 検証が成功すると、KBS は 鍵を AA に解放します。
- AA は鍵をコンフィデンシャル Pod に返し、フローを続行します。
アテステーションの詳細は、連載ブログの コンフィデンシャル・コンピューティングのアテステーション を参照してください。
こAMD SEV-SNP (この作業のベース) の場合に、Azure クラウド上でアテステーションがどのように実行されるかについては、OpenShift を備えた Azure 上のコンフィデンシャルコンテナ:技術的側面の詳細 を参照してください。
パブリッククラウドの AI ワークロードと機密性
AI ワークロードの実行において、パブリッククラウドには次のようなメリットがあります。
- スケーラビリティ:AI モデル、特に深層学習モデルには膨大な計算能力が必要ですが、パブリッククラウドを使用することで、事前の設備投資を行うことなく必要なリソースを使用できます。リソースは、作業完了後に削除できます。
- データストレージ:AI には大量のデータが必要です。パブリッククラウドは、柔軟性とコスト効率に優れた大規模なストレージソリューションを提供します。
- 高度なツールとサービス:AWS、Azure、Google Cloud などのクラウドプロバイダーは、AI や機械学習に特化したツールを提供しており、開発者はこれらのツールを使用することで容易にモデルを構築およびデプロイできます。その例として、高度 GPU 機能の使用が挙げられます。
- グローバルな展開:パブリッククラウドのデータセンターは世界中に存在するため、エンドユーザーの近くで AI サービスを展開して遅延を削減できます。
- 共同開発環境:クラウドを活用することで、共同ワークスペースの使用が容易になります。複数のチームが AI プロジェクトに同時に取り組み、リソースを共有し、迅速に反復することができます。このような協働アプローチにより、開発サイクルが加速され、知識の共有が促進されます。
上記のようなメリットがある一方で、訓練に使用される機密データの機密性と訓練済みモデルの保護などの課題もいくつかあり、各種ワークロードに固有の機密性要件を理解することが重要です。それを踏まえ、どの AI ワークロードになぜ厳格な機密性が必要なのか詳しく見てみましょう。
機密性の保持が必要な AI ワークロードとその理由
すべての AI ワークロードに厳格な機密性が求められるわけではありません。しかし、機密データを処理する AI ワークロードの場合は例外なく機密性が求められます。その理由は次のとおりです。
- 医療診断:病気の予測や治療法の提案を行う AI モデルは、機密性の高い患者データを処理します。機密性侵害が発生すると、患者のプライバシーや信頼が損なわれる可能性があります。
- 財務予測:株式市場の動向や信用スコアを予測するモデルは、機密性のある財務データを処理します。不正アクセスは、経済的損失や不当な利益をもたらす可能性があります。
- パーソナルアシスタント:AI 対応パーソナルアシスタントは、個人のメール、スケジュール、設定にアクセスできます。ユーザーのプライバシーを保護するためには、機密性を確保することが重要です。
- 自動運転対応車:これらの車両は、周囲とユーザーのリアルタイムデータを収集します。ユーザーの信頼と安全の観点から、データの機密性保持が不可欠です。
基本的に、AI をパブリッククラウドと統合することで機能が強化されますが、倫理的で、安全かつ効率的な運用には、各種ワークロードの僅かな違いとその機密性要件を理解する必要があります。
以降のセクションでは、AI ワークロードを保護して安全にデプロイするために、Enkrypt AI がどのように CNCF CoCo プロジェクトを活用しているか紹介します。
AI ワークロードに対する Enkrypt AI と CoCo の使用
Enkrypt AI とは
AI のコンプライアンス、プライバシー、セキュリティ、計測などに対するニーズが高まる中、Enkrypt AI はそれに応えるソリューションを構築しています。AI が導き出す洞察にビジネスがますます依存するにつれ、AI モデルおよびデータのインテグリティ、信頼性、プライバシーの確保が最優先事項になっていますが、市場の現行ソリューションはそれに対処しきれていません。
Enkrypt AI のソリューションは、VPC やエッジデバイスをはじめとするサードパーティ・インフラストラクチャにデプロイされた場合に、AI モデルの機密性とインテグリティを実現します。Enkrypt AI は、CNCF CoCo プロジェクトと 準同型暗号 を組み合わせるなどして、最先端の暗号化技術を同社のソリューションに活用しています。
準同型暗号は暗号化方式のひとつであり、これを使用することで復号化せずに 計算 を実行できます。プロセスの出力も暗号化されますが、復号化した場合の結果は、すべての作業を暗号化されていないデータに対して実行した場合と同じになります。「準同型」は、同型の 2 構造間の構造保存写像である 代数準同型 に由来します。この場合、暗号化と復号化は非暗号化データと復号化データ間の準同型です。
このアプローチは、復号化データの処理に対する潜在的な攻撃を防止し、一般的にはデータが常に暗号化されるクラウド環境でのデータ処理に使用されます。ここで強調したいのは、たとえそれがクラウドプロバイダー管理者であっても、鍵にアクセスできないためデータの復号化や操作ができない点です。
暗号化データに対する計算 は、実際には変数、係数、および加算、減算、乗算などの演算で構成される式を計算するための標準的な計算モデルである ブーリアン演算 (yes/no) または 算術回路 の実行を意味します。これらは、実際に (秘密鍵/公開鍵などの) 暗号化や復号化を実行する際に使用する構成要素です。
ここで話を戻しますが、準同型暗号には実際に実行する計算に基づき、いくつかの種類があります (一部はある程度レベル分けされています)。このブログでは、暗号化データに対してほとんどの計算を実行できる 完全準同型暗号 (FHE) に焦点を当てます。
FHE は、AI ワークロードに対し、計算中もデータの暗号化が維持されるよう保証するという極めて重要な役割を果たします。この FHE 固有の特性により、基盤となるデータを公開することなく AI モデルを認証できます。以前は FHE がデータに適用されていましたが、現在は Enkrypt AI がこれをモデルの重みに適用します。ほとんどの一般的な暗号化スキームと同様に、FHE は公開鍵と秘密鍵 (公開鍵は暗号化、秘密鍵は復号化に使用) を生成します。Enkrypt AI ソリューションにおいて、秘密鍵を保護することは極めて重要です。
FHE はプライバシーとセキュリティの観点から大きなメリットをもたらしますが、独自のオーバーヘッドも伴います。
- 前述した操作を実行するための 計算オーバーヘッド
- ストレージのオーバーヘッド:FHE を使用してデータを暗号化すると、パターンや構造が不明瞭になるエンコード方式が原因で、通常はプレインテキストの暗号化データよりもデータサイズが大きくなります。
Enkrypt AI は、この FHE に伴う 計算オーバーヘッドの課題 を、AI モデルの一部を選択的に暗号化することで克服しています。このアプローチでは、フルモデルの暗号化に関連する計算オーバーヘッドと遅延が劇的に削減されますが、同時に高レベルのセキュリティも維持され、モデル出力 (基本的には使用可能なモデル) を判読できるのが認証および許可されたユーザーのみであることが検証されます。
Enkrypt AI は、リスクベースのアプローチを適用してモデルのどの部分を暗号化するかを決定します。つまり、機密情報を含むコンポーネントやモデルのパフォーマンスにとって重要なコンポーネントなど、高リスクコンポーネントのみが暗号化の対象として優先されます。この選択的な暗号化戦略により、計算コストと遅延コストが削減されるだけでなく、暗号化されたモデルファイルのサイズも小さくなり、保存と送信が容易になります。これにより、FHE に伴う ストレージオーバーヘッドの課題 が克服されます。典型的な例としては、部分的に暗号化されたモデルからの出力が常に暗号化された状態を維持するために、モデルの最終層 (細かなチューニングにおいて重要な層) を暗号化する場合が挙げられます。
要約すると、セキュリティ、ストレージ容量、処理速度の間のバランスを整え、FHE が原因で発生する計算とストレージの課題を軽減しつつ、効果的に FHE に対処できるソリューションこそが Enkrypt AI が提供する価値です。
Enkrypt AI ソリューションは、3 つのパーツに分割できます。
- モデル所有者 (モデル開発者):訓練済みモデルをセキュアなモデルに変換します。
- モデルユーザー (コンピュート・インフラストラクチャ上にデプロイされたモデルが必要なエンドユーザー):保護されたモデルをロードし、それと対話します (データをプッシュしたり、結果を取得したりします)。
- Enkrypt AI キーマネージャー:復号化に使用する秘密鍵を管理します。
次の図は、上記のパーツの構成を示しています。
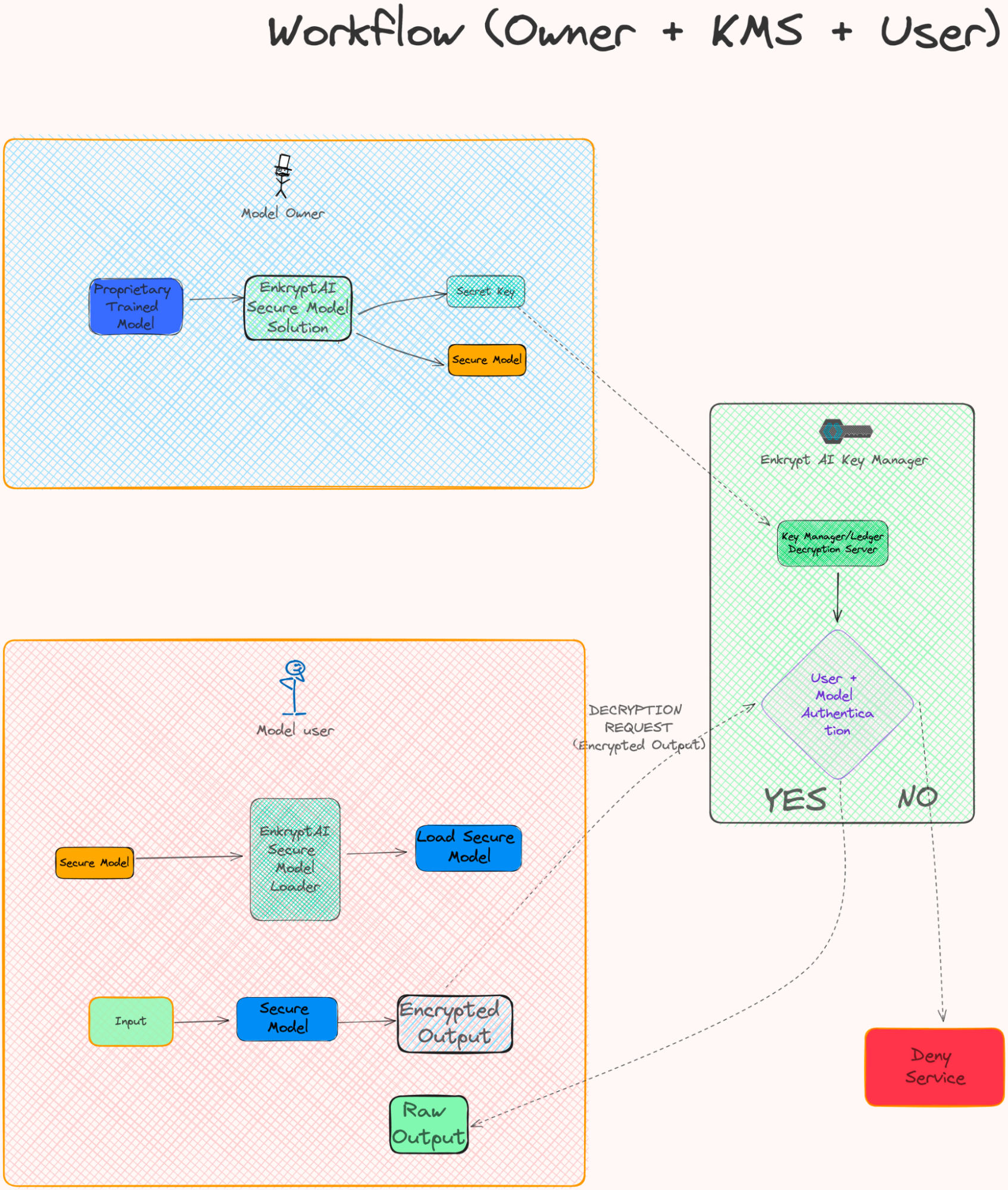
以下の点に留意してください。
- このモデルは、最初に強化されたセキュリティで暗号化され、モデル所有者によってデプロイされます。
- モデル所有者は、秘密鍵を Enkrypt AI キーマネージャーにプッシュします。
- モデルユーザーは、その鍵で復号化される暗号化出力でリクエストを送信します。
- 生データは、復号化した後にモデルユーザーに送信されます。
Enkrypt AI ソリューションの詳細は、White Paper - Enkrypt AI を参照してください。
CoCo の役割
Enkrypt AI キーマネージャーは、悪意のあるインフラストラクチャ管理者による鍵の抽出に対して脆弱である可能性のあるワークロードです。前のセクションで述べた内容は、秘密鍵が安全に保存され、Enkrypt AI キーマネージャー内で使用されることを前提としていました。Enkrypt AI キーマネージャーが、完全に隔離および保護された環境で実行されると想定できれば、ソリューションはそのまま使用できます。しかし現実はそうではありません。特にサードパーティのクラウドデプロイメントには当てはまりません。
2 つめの課題は、AI モデルと、AI ワークロードに使用される機密データの保護です。たとえばメンタルヘルス・チャットボットの場合、ユーザーが入力したデータは非常に機密性が高いため、改ざんを防ぐためにモデル自体を保護する必要があります。
CoCo ソリューションは、この課題を次のように克服しました。
- キーマネージャーを保護する:Enkrypt AI キーマネージャーをコンフィデンシャルコンテナ内で実行することで、クラウドプロバイダーによる秘密鍵へのアクセスを確実に防止できます。
- AI ワークロードを保護する:モデルユーザーをコンフィデンシャルコンテナ内で実行することで、データとモデルを確実に保護できます。
キーマネージャーの保護
前のセクションで説明したとおり、Enkrypt AI キーマネージャーは Enkrypt AI ソリューションの重要な構成要素です。その Enkrypt AI キーマネージャーのコードを保護し、それが管理する鍵を使用中も含めて保護するために使用されるのが CoCo です。
Enkrypt AI キーマネージャーは、実行時にコードとキーを保護するために、高信頼実行環境内にコンフィデンシャルコンテナとしてデプロイされます。
次の図は、そのデプロイメントを示しています。
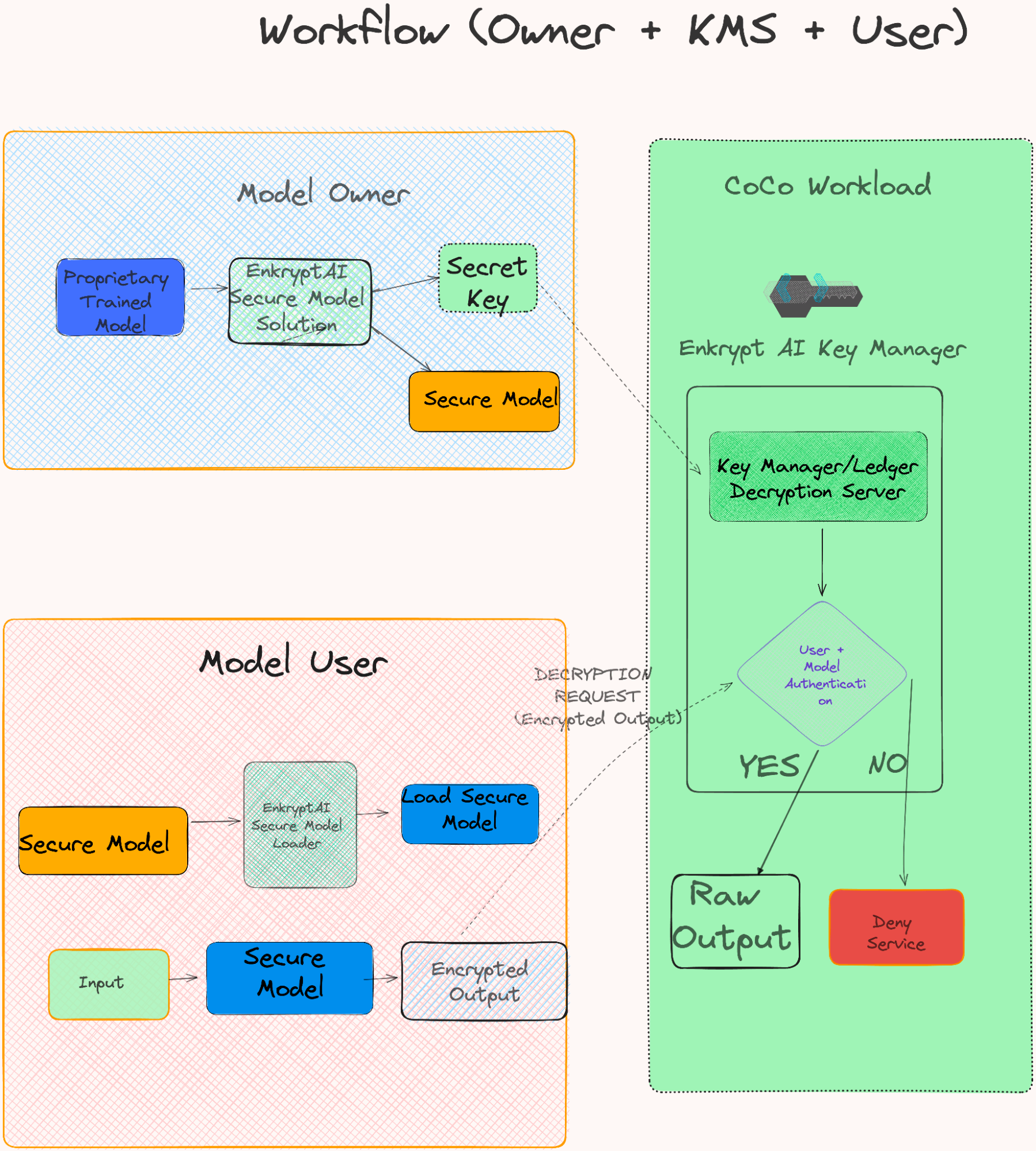
ユーザーデータと AI ワークロードの保護
従来の機械学習 (ML) モデルや非 GPU アクセルレーテッド・ワークロードなど、コンフィデンシャルコンテナ内に完全なモデルをデプロイできるシナリオもあります。そのような場合、Enkrypt AI は CoCo を使用して高信頼実行環境内にモデルをデプロイします。さらに、Enkrypt AI の社内 SDK クライアントは、推論に使用されるデータが常に暗号化され、エンドユーザー側でのみ復号化されることを保証して、推論ワークフロー全体でエンドツーエンドのプライバシーとセキュリティを提供します。
次の図は、そのデプロイメントを示しています。
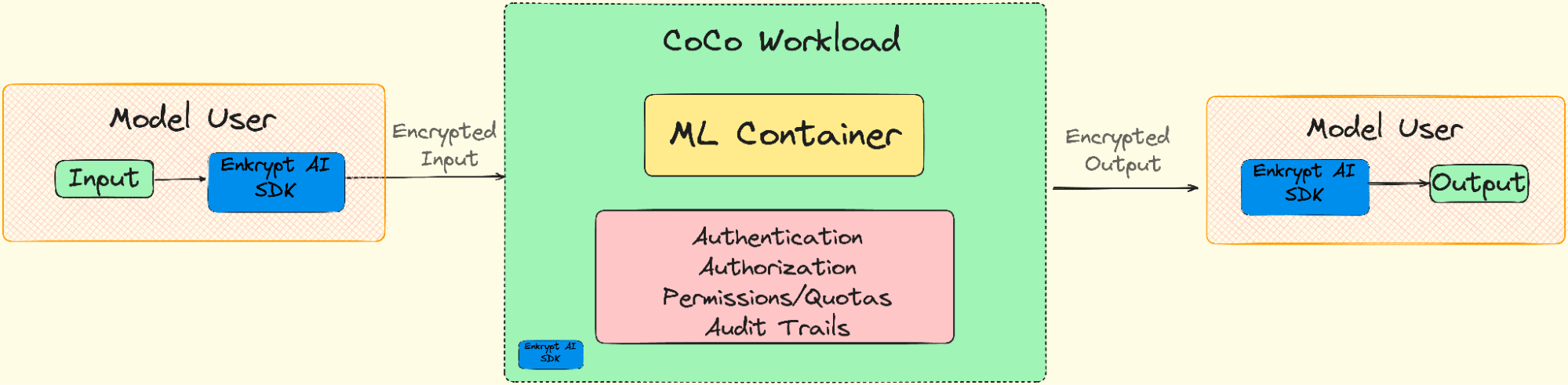
Enkrypt AI のソフトウェア開発キット (SDK) は、コンフィデンシャルコンテナに配置して不正アクセスから保護することで、AI モデルのデプロイメントを合理化します。権限、必要なアテステーション、検証を処理し、デプロイメントプロセスを単純化します。
SDK は暗号化、鍵管理、復号化も処理するため、ユーザーは SDK を使用することで、より安全な入力送信と出力受信を容易に実現できます。
ユーザーにとって、データのセキュリティは最重要事項です。入力と推論出力はいずれも暗号化された状態で維持され、鍵へのアクセスはセキュリティが強化された CoCo 環境内でのみ可能になります。AI モデルのインテグリティは保証され、権限を持つ当事者が検証できます。
ユースケースのデモ
Azure 上の Red Hat OpenShift コンフィデンシャルコンテナ環境
Red Hat OpenShift 上のコンフィデンシャルコンテナ・ソリューションを構成するコンポーネントの概要を説明するデモビデオ。
デモ:コンフィデンシャルコンテナでの鍵の取得
コンフィデンシャルコンテナ・ワークロードのサンプルを使用した安全な鍵取得のデモビデオ。
コンフィデンシャルコンテナを使用した暗号化コンテナイメージのワークフロー
暗号化されたコンテナイメージを使用したコンフィデンシャルコンテナ・デプロイメントのサンプルを示すデモビデオ。
コンフィデンシャルコンテナとして Enkrypt AI を実行
Azure 上に OpenShift コンフィデンシャルコンテナを持つ AMD SEV-SNP 高信頼実行環境内 (TEE) で実行されている Enkrypt AI を使用して AI モデルを保護する場合のデモビデオ。
要約
この記事では、CNCF コンフィデンシャルコンテナ・プロジェクトを紹介しました。いくつかの CoCo 構成要素 (ピア Pod、KBS、AS など) について説明し、コンフィデンシャルコンテナがパブリッククラウド内の AI ワークロードを保護する基盤となることを取り上げました。
また、CoCo を使用した安全な鍵管理と改ざん防止が講じられた機械学習 (ML) のデプロイメントを実現することで、顧客が直面しているモデルの管理と保護に関する課題を Enkrypt AI が 克服したことに注目しました。
最後に、Azure confidential computing を活用して、OpenShift サンドボックスコンテナ と CoCo コンポーネントで Enkrypt AI ワークロードを実行する場合のデモを紹介しました。
執筆者紹介
Tanay is working in the area of large language model security, privacy and governance. He is a key software engineer at Enkrypt AI, responsible for the work on productizing confidential containers for AI workloads.
Pradipta is working in the area of confidential containers to enhance the privacy and security of container workloads running in the public cloud. He is one of the project maintainers of the CNCF confidential containers project.
Suraj Deshmukh is working on the Confidential Containers open source project for Microsoft. He has been working with Kubernetes since version 1.2. He is currently focused on integrating Kubernetes and Confidential Containers on Azure.
Jens Freimann is a Software Engineering Manager at Red Hat with a focus on OpenShift sandboxed containers and Confidential Containers. He has been with Red Hat for more than six years, during which he has made contributions to low-level virtualization features in QEMU, KVM and virtio(-net). Freimann is passionate about Confidential Computing and has a keen interest in helping organizations implement the technology. Freimann has over 15 years of experience in the tech industry and has held various technical roles throughout his career.
Magnus has received an academic education in Humanities and Computer Science. He has been working in the software industry for around 15 years. Starting out in the world of proprietary Unix he quickly learned to appreciate open source and has applied it everywhere since. He was engaged mostly in the niches of automation, virtualization and cloud computing. During his career in various industries (mobility, sustainability, tech) he exercised various contributor and leadership roles. Currently he's employed as a Software Engineer at Microsoft, working in the Azure Core organization.
Prashanth is working in the area of large language model security, privacy and governance. He is co-founder of Enkrypt AI.
類似検索
さらに強化され、すぐに使用でき、コストがかからない:コンテナセキュリティの進化
Red Hat Universal Base Image の (再) 紹介
Collaboration In Product Security | Compiler
Keeping Track Of Vulnerabilities With CVEs | Compiler
チャンネル別に見る
自動化
テクノロジー、チームおよび環境に関する IT 自動化の最新情報
AI (人工知能)
お客様が AI ワークロードをどこでも自由に実行することを可能にするプラットフォームについてのアップデート
オープン・ハイブリッドクラウド
ハイブリッドクラウドで柔軟に未来を築く方法をご確認ください。
セキュリティ
環境やテクノロジー全体に及ぶリスクを軽減する方法に関する最新情報
エッジコンピューティング
エッジでの運用を単純化するプラットフォームのアップデート
インフラストラクチャ
世界有数のエンタープライズ向け Linux プラットフォームの最新情報
アプリケーション
アプリケーションの最も困難な課題に対する Red Hat ソリューションの詳細
仮想化
オンプレミスまたは複数クラウドでのワークロードに対応するエンタープライズ仮想化の将来についてご覧ください






